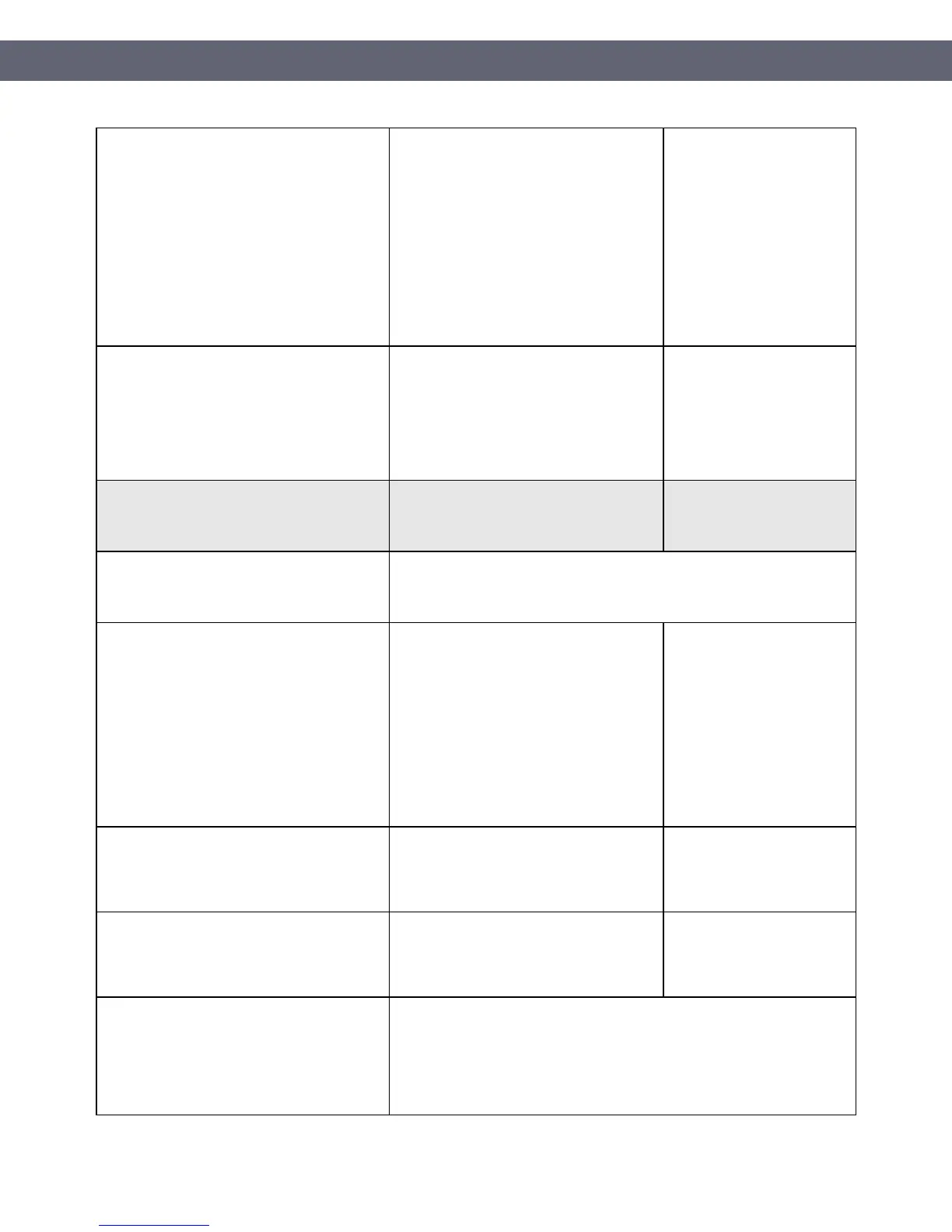
6.2 Ensure that all system components and
software are protected from known
vulnerabilities by installing applicable
vendor-supplied security patches. Install
critical security patches within one month of
release.
Note:
Critical security patches should be
identified according to the risk ranking
process defined in Requirement 6.1.
Toast monitors for security vulnerabilities
that affect the POS solution and
underlying systems and issues updates
and/or guidance as needed.
Toast-issued devices are preconfigured to
download security updates as they
become available.
You are responsible for
ensuring security updates
are installed on your
hardware as they become
available.
You are responsible for
replacing your hardware
once the support warranty
has ended and manufacturer
security updates are no
longer provided.
6.4.6 Upon completion of a significant
change, all relevant PCI DSS requirements
must be implemented on all new or changed
systems and networks, and documentation
updated as applicable.
Toast ensures any significant changes to
the solution comply with PCI DSS
requirements.
You are responsible for
ensuring any configuration
changes you make to Toast
POS solution or changes in
how the solution is used are
compliant with PCI DSS
requirements.
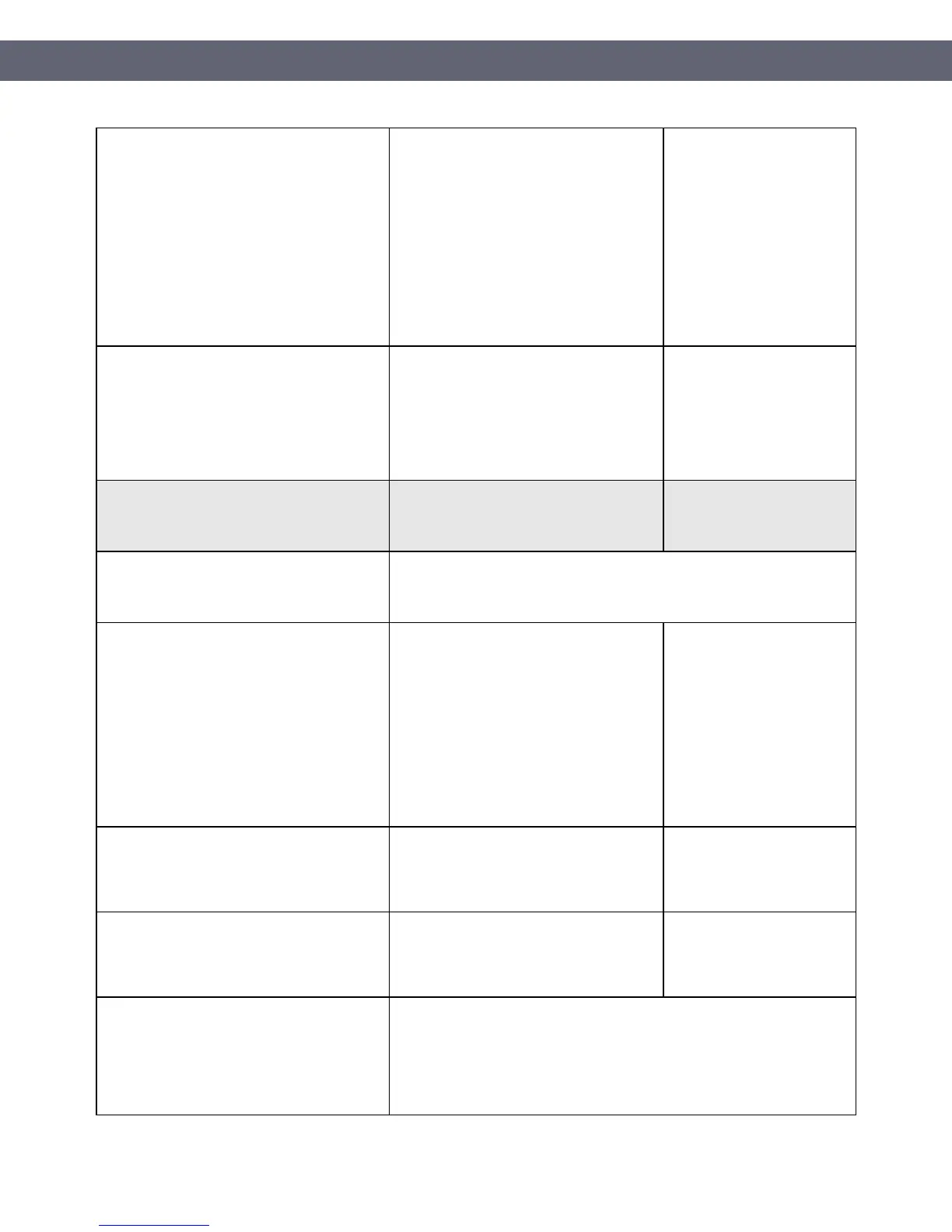
Requirement 7: Restrict access to
cardholder data by business need to know
What you will need to do
7.1 Limit access to system components and
cardholder data to only those individuals
whose job requires such access.
7.1.1 Define access needs for each role,
including:
● System components and data resources
that each role needs to access for their
job function
● Level of privilege required (for example,
user, administrator, etc.) for accessing
resources.
During deployment, Toast personnel will
create a user account with administrative
access for the restaurant point of contact.
Users with Administrator access can
invite or delete other account users and
modify access and system privileges for all
users.
Note: Toast POS limits user access to a
truncated PAN.
It is your responsibility to
ensure access and system
privileges are appropriate
for each user.
7.1.2 Restrict access to privileged user IDs to
least privileges necessary to perform job
responsibilities.
Users with Administrator access can
invite or delete other account users and
modify access and system privileges for all
users.
It is your responsibility to
ensure access and system
privileges are appropriate
for each user.
7.1.3 Assign access based on individual
personnel’s job classification and function.
Users with Administrator access can
invite or delete other account users and
modify access and system privileges for all
users.
It is your responsibility to
ensure access and system
privileges are appropriate
for each user.
7.2 Establish an access control system(s) for
systems components that restricts access
based on a user’s need to know, and is set to
“deny all” unless specifically allowed.
This access control system(s) must include
the following:
PCI Instruction Guide
© Toast 2018
Page 28 of 44
 Loading...
Loading...