(for example, to a manager or security
officer).
9.10 Ensure that security policies and
operational procedures for restricting
physical access to cardholder data are
documented, in use, and known to all
affected parties.
You are also responsible for
maintaining appropriate
policies and processes.
Note: additional policies or
procedures may be required
if employees hande physical
payment cards or cardholder
data is received via
telephone or other
electronic means and
manually entered.
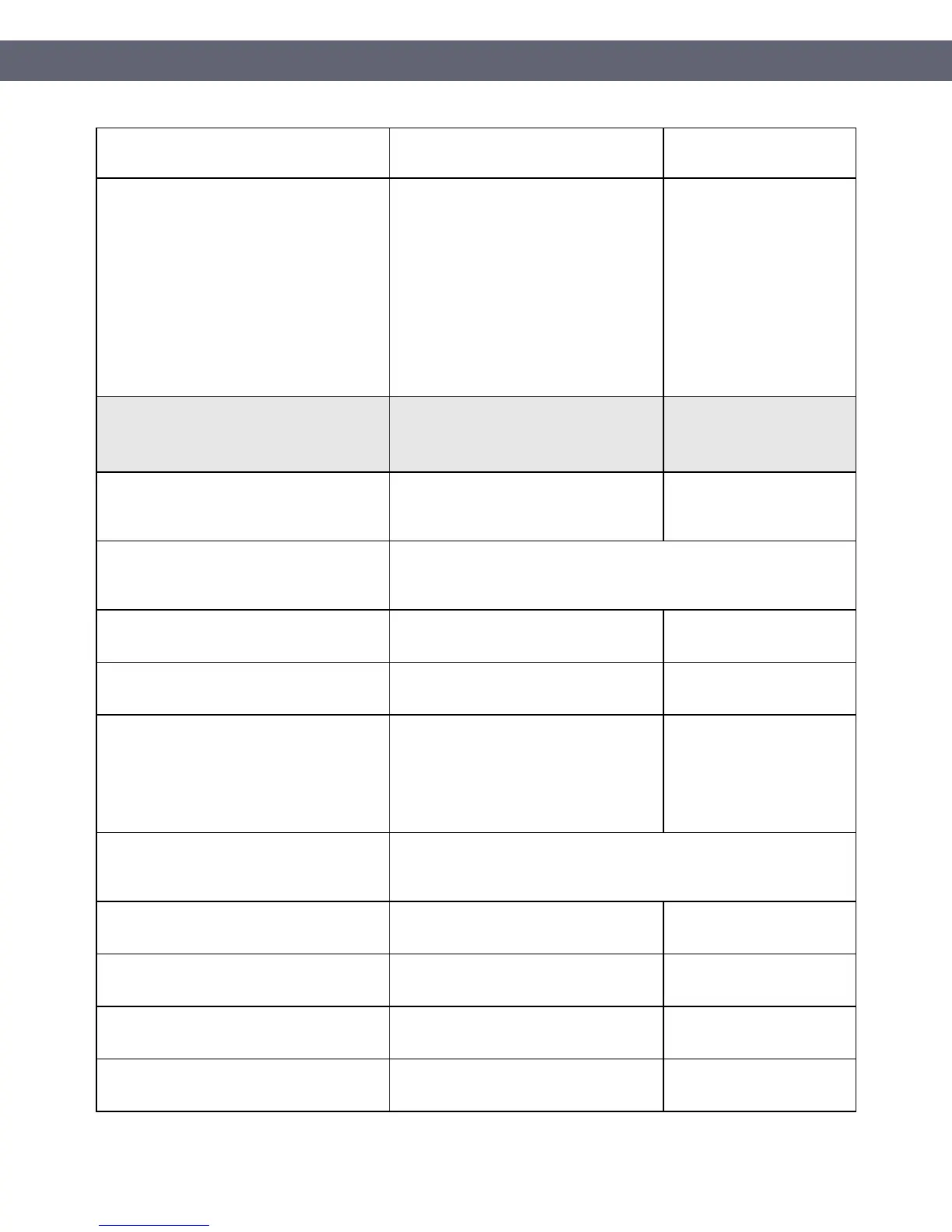
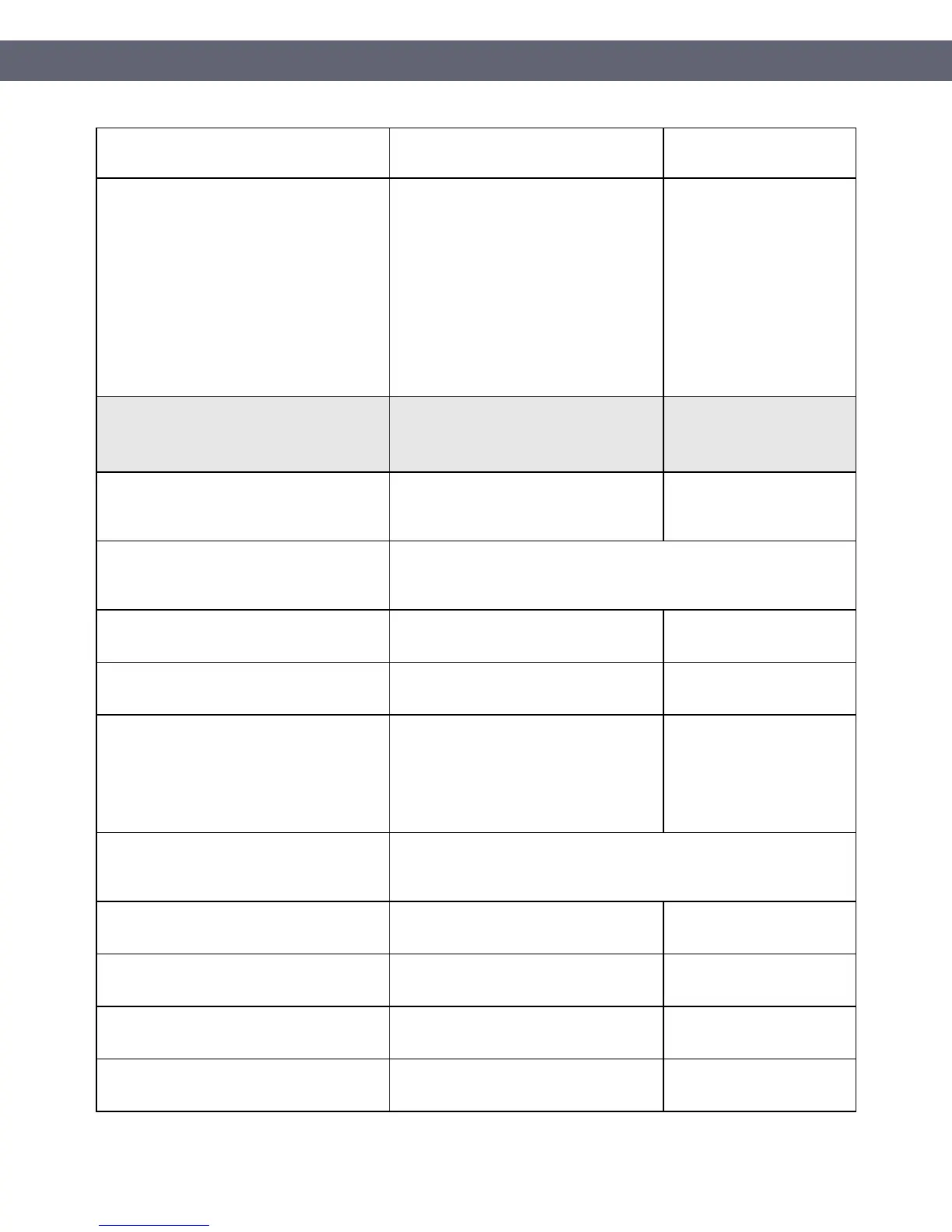
Requirement 10: Track and monitor all
access to network resources and cardholder
data
What you will need to do
10.1 Implement audit trails to link all access
to system components to each individual
user.
The Toast POS solution is setup by default
to implement PCI DSS compliant logging.
10.2 Implement automated audit trails for all
system components to reconstruct the
following events:
10.2.2 All actions taken by any individual
with root or administrative privileges
The Toast POS solution is setup by default
to implement PCI DSS compliant logging.
10.2.4 Invalid logical access attempts
The Toast POS solution is setup by default
to implement PCI DSS compliant logging.
10.2.5 Use of and changes to identification
and authentication mechanisms—including
but not limited to creation of new accounts
and elevation of privileges—and all changes,
additions, or deletions to accounts with root
or administrative privileges
The Toast POS solution is setup by default
to implement PCI DSS compliant logging.
10.3 Record at least the following audit trail
entries for all system components for each
event:
10.3.1 User identification
The Toast POS solution is setup by default
implement PCI DSS compliant logging.
The Toast POS solution is setup by default
implement PCI DSS compliant logging.
The Toast POS solution is setup by default
implement PCI DSS compliant logging.
10.3.4 Success or failure indication
The Toast POS solution is setup by default
implement PCI DSS compliant logging.
PCI Instruction Guide
© Toast 2018
Page 35 of 44
 Loading...
Loading...