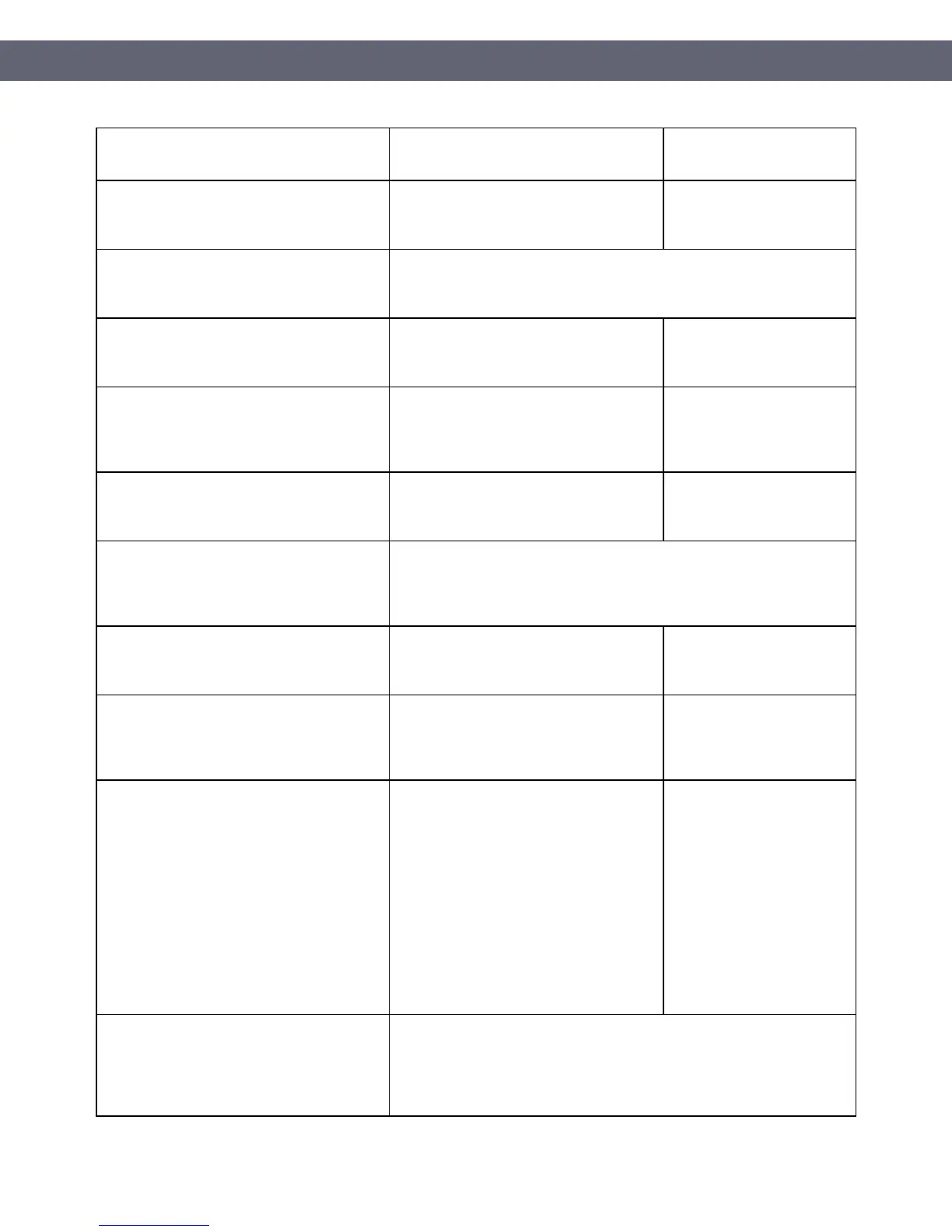
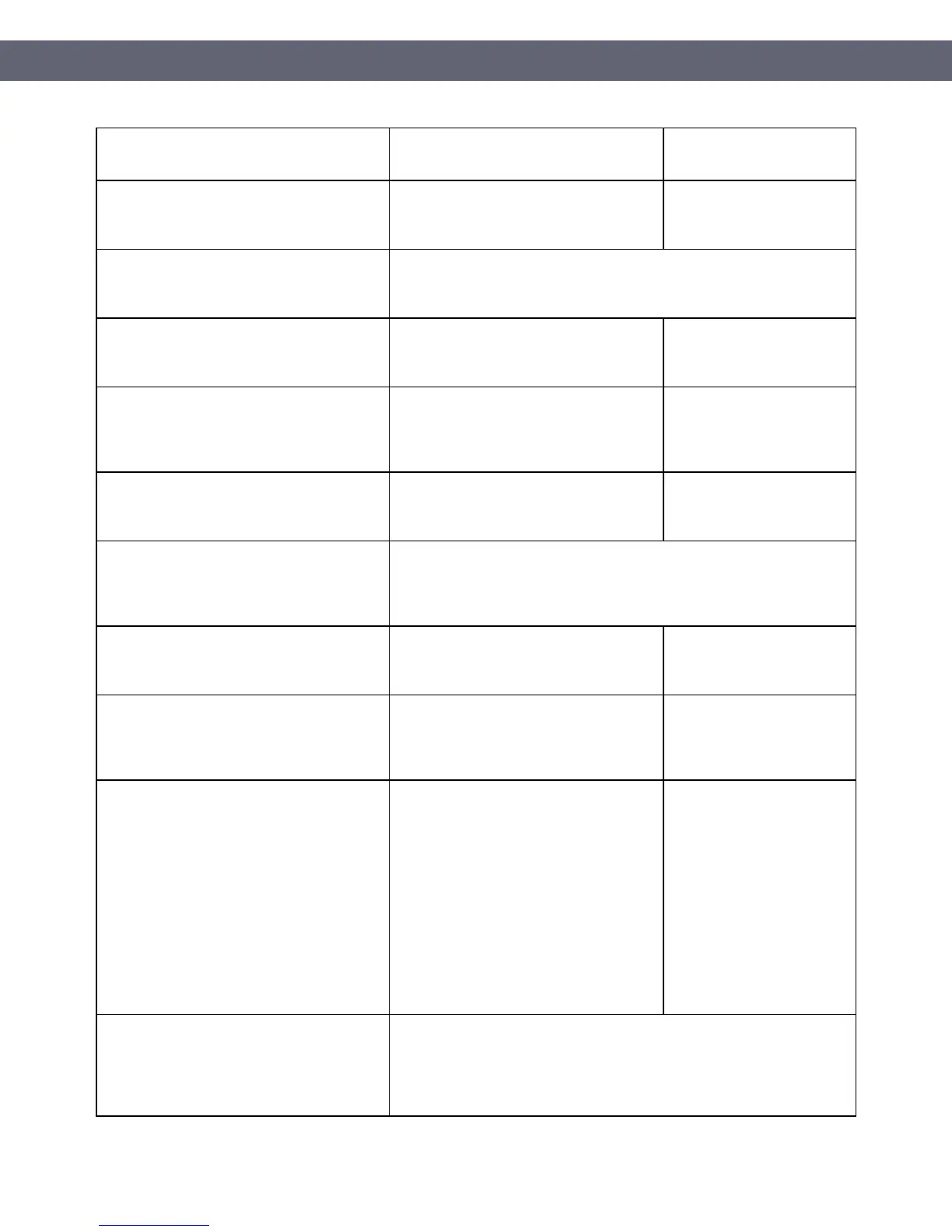
business partners, with immediate
deactivation after use
instruction on secure connection and
disconnection.
12.4 Ensure that the security policy and
procedures clearly define information
security responsibilities for all personnel.
You are responsible for
maintaining appropriate
policies and processes.
12.5 Assign to an individual or team the
following information security management
responsibilities:
12.5.1 Establish, document, and distribute
security policies and procedures.
You are responsible for
maintaining appropriate
policies and processes.
12.5.3 Establish, document, and distribute
security incident response and escalation
procedures to ensure timely and effective
handling of all situations.
You are responsible for
maintaining appropriate
policies and processes.
12.5.4 Administer user accounts, including
additions, deletions, and modifications.
You are responsible for
maintaining appropriate
policies and processes.
12.6 Implement a formal security awareness
program to make all personnel aware of the
cardholder data security policy and
procedures.
12.6.1 Educate personnel upon hire and at
least annually.
You are responsible for
maintaining appropriate
policies and processes.
12.6.2 Require personnel to acknowledge at
least annually that they have read and
understood the security policy and
procedures.
You are responsible for
maintaining appropriate
policies and processes.
12.7 Screen potential personnel prior to hire
to minimize the risk of attacks from internal
sources. (Examples of background checks
include previous employment history,
criminal record, credit history, and reference
checks.)
Note: For those potential personnel to be
hired for certain positions such as store
cashiers who only have access to one card
number at a time when facilitating a
transaction, this requirement is a
recommendation only.
You are responsible for
maintaining appropriate
policies and processes.
12.8 Maintain and implement policies and
procedures to manage service providers,
with whom cardholder data is shared, or that
could affect the security of cardholder data,
as follows
PCI Instruction Guide
© Toast 2018
Page 41 of 44
 Loading...
Loading...