10
Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy
OL-6262-01
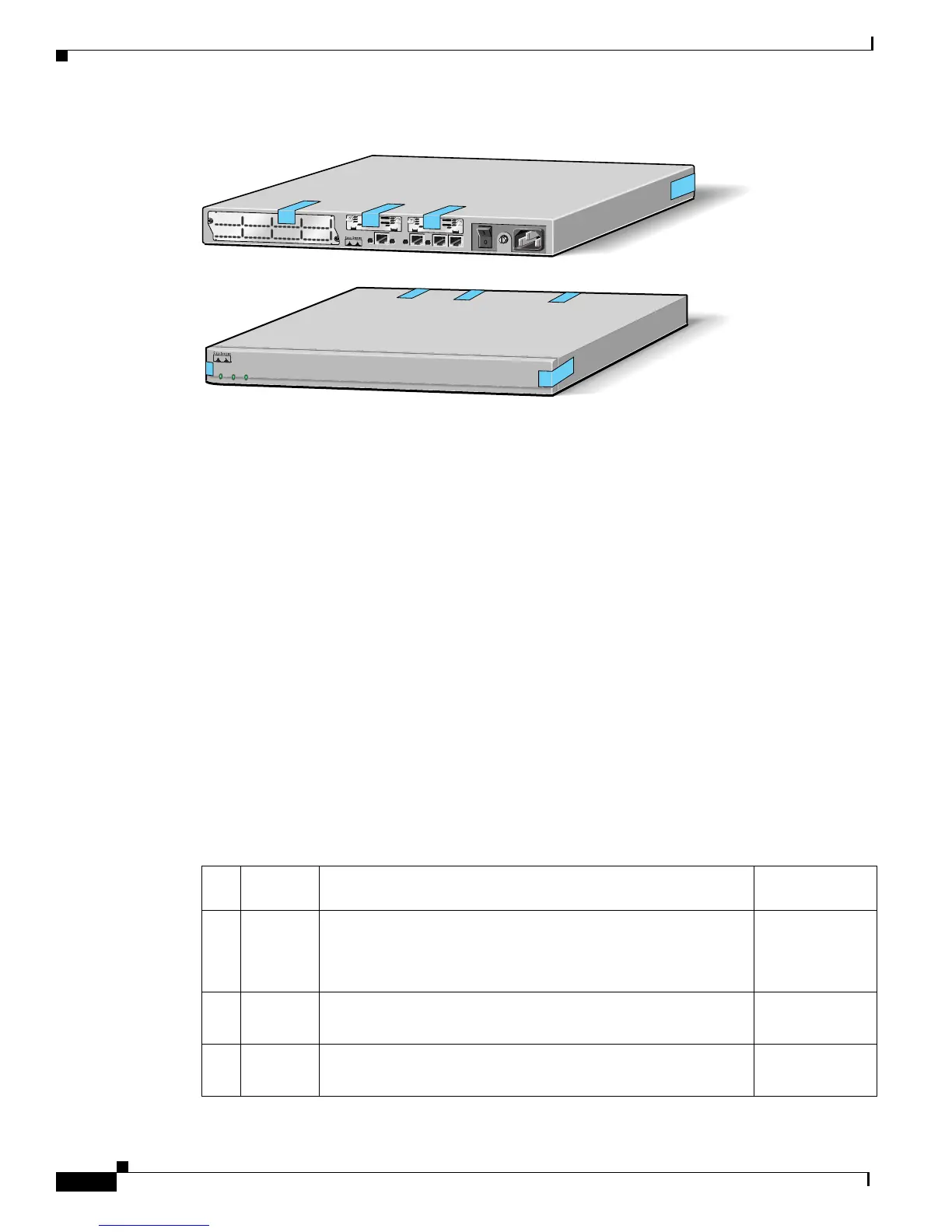
The 2621XM/2651XM Router
Figure 6 Cisco 2621XM and Cisco 2651XM Tamper Evidence Label Placement
The tamper evidence seals are produced from a special thin gauge vinyl with self-adhesive backing. Any
attempt to open the router, remove Network Modules or WIC cards, or the front faceplate will damage
the tamper evidence seals or the painted surface and metal of the module cover. Since the tamper
evidence seals have non-repeated serial numbers, they may be inspected for damage and compared
against the applied serial numbers to verify that the module has not been tampered. Tamper evidence
seals can also be inspected for signs of tampering, which include the following: curled corners, bubbling,
crinkling, rips, tears, and slices. The word “OPEN” may appear if the label was peeled back.
Cryptographic Key Management
The router securely administers both cryptographic keys and other critical security parameters such as
passwords. The tamper evidence seals provide physical protection for all keys. All keys are also
protected by the password-protection on the Crypto Officer role login, and can be zeroized by the Crypto
Officer. Keys are exchanged manually and entered electronically via manual key exchange or Internet
Key Exchange (IKE).
The modules contain a cryptographic accelerator card (the AIM-VPN/EP), which provides DES (56-bit)
(only for legacy systems) and 3DES (168-bit) IPSec encryption at up to 15Mbps, MD5 and SHA-1
hashing, and has hardware support for DH and RSA key generation.
The module supports the following critical security parameters (CSPs):
99498
SEE MANUAL BEFORE INSTALLATION
SERIAL 1
SERIAL 0
CONN
CONN
WIC
2A/S
SEE MANUAL BEFORE INSTALLATION
SERIAL 1
SERIAL 0
CONN
CONN
WIC
2T
Cisco 2611
100-240V– 1A
50/60 Hz 47 W
W0
AUX
CONSOLE
ETHERNET 0
ACT
LINKACTETHERNET 1
LINK
W1
POWER
RPS
ACTIVITY
Cisco 2600
SERIES
Table 4 Critical Security Parameters
# CSP
Name
Description Storage
1 CSP 1 This is the seed key for X9.31 PRNG. This key is stored in DRAM
and updated periodically after the generation of 400 bites; hence,
it is zeroized periodically. Also, the operator can turn off the
router to zeroize this key.
DRAM
(plaintext)
2 CSP 2 The private exponent used in Diffie-Hellman (DH) exchange.
Zeroized after DH shared secret has been generated.
DRAM
(plaintext)
3 CSP 3 The shared secret within IKE exchange. Zeroized when IKE
session is terminated.
DRAM
(plaintext)

 Loading...
Loading...