10-16
Cisco ASA Series Firewall CLI Configuration Guide
Chapter 10 NAT Examples and Reference
NAT for VPN
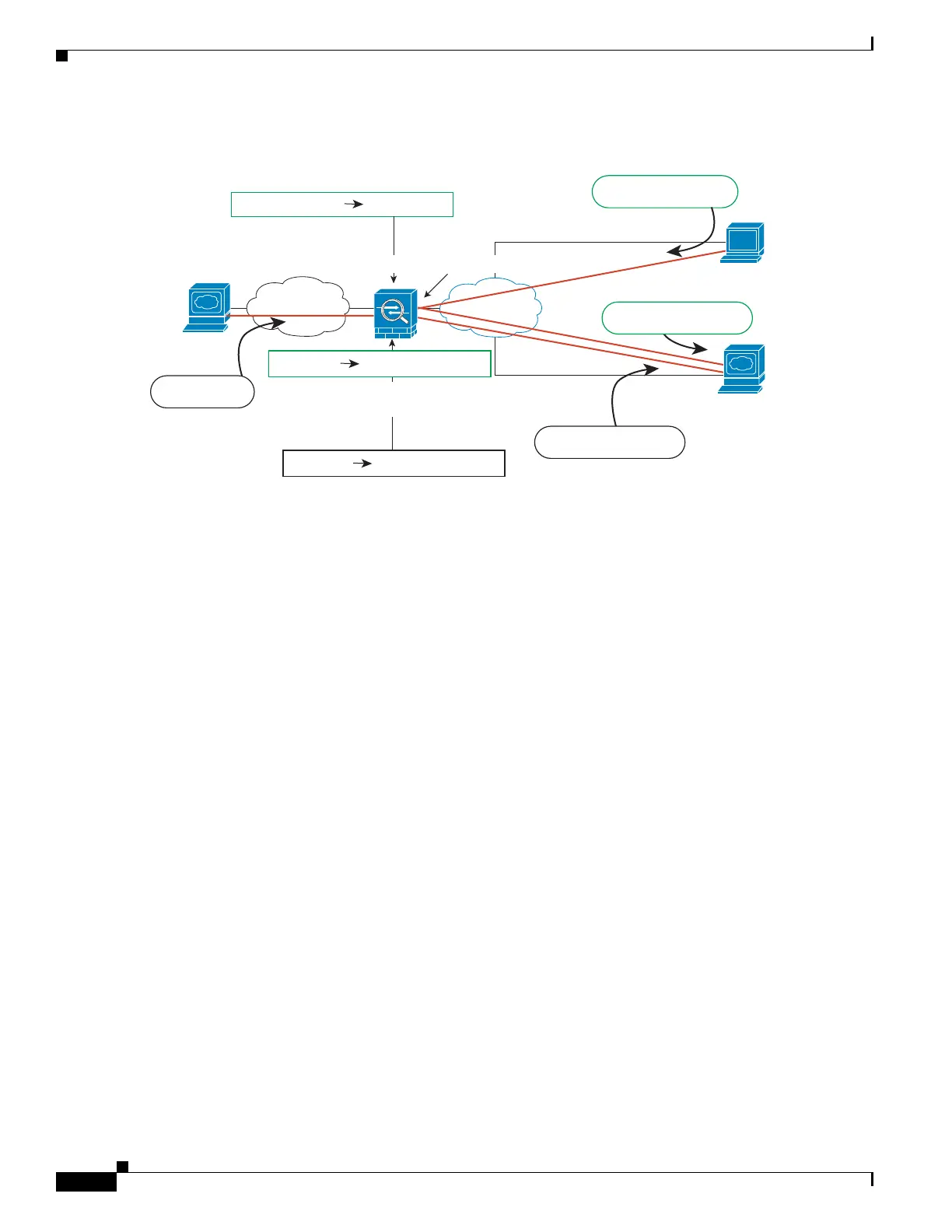
Figure 10-13 Interface PAT for Internet-Bound VPN Traffic (Intra-Interface)
The following figure shows a VPN client that wants to access an inside mail server. Because the ASA
expects traffic between the inside network and any outside network to match the interface PAT rule you
set up for Internet access, traffic from the VPN client (10.3.3.10) to the SMTP server (10.1.1.6) will be
dropped due to a reverse path failure: traffic from 10.3.3.10 to 10.1.1.6 does not match a NAT rule, but
returning traffic from 10.1.1.6 to 10.3.3.10 should match the interface PAT rule for outgoing traffic.
Because forward and reverse flows do not match, the ASA drops the packet when it is received. To avoid
this failure, you need to exempt the inside-to-VPN client traffic from the interface PAT rule by using an
identity NAT rule between those networks. Identity NAT simply translates an address to the same
address.
VPN Client
209.165.201.10
Internet
Src: 209.165.201.10
10.3.3.10
203.0.113.1:6070
10.3.3.10
10.1.1.6
www.example.com
Inside
209.165.201.10
1. HTTP request to www.example.com
4. HTTP request to
www.example.com
C. HTTP request to www.example.com
2. ASA decrypts packet; src address is
now local address
Src: 203.0.113.1:6070
ASA Outside IP: 203.0.113.1
10.1.1.6
203.0.113.1:6075
Src: 10.1.1.6
A. HTTP to
www.example.com
B. ASA performs interface PAT for
outgoing traffic.
Src: 203.0.113.1:6075
3. ASA performs interface PAT for outgoing traffic.
Intra-interface config req’d.
303462

 Loading...
Loading...