10-20
Cisco ASA Series Firewall CLI Configuration Guide
Chapter 10 NAT Examples and Reference
NAT for VPN
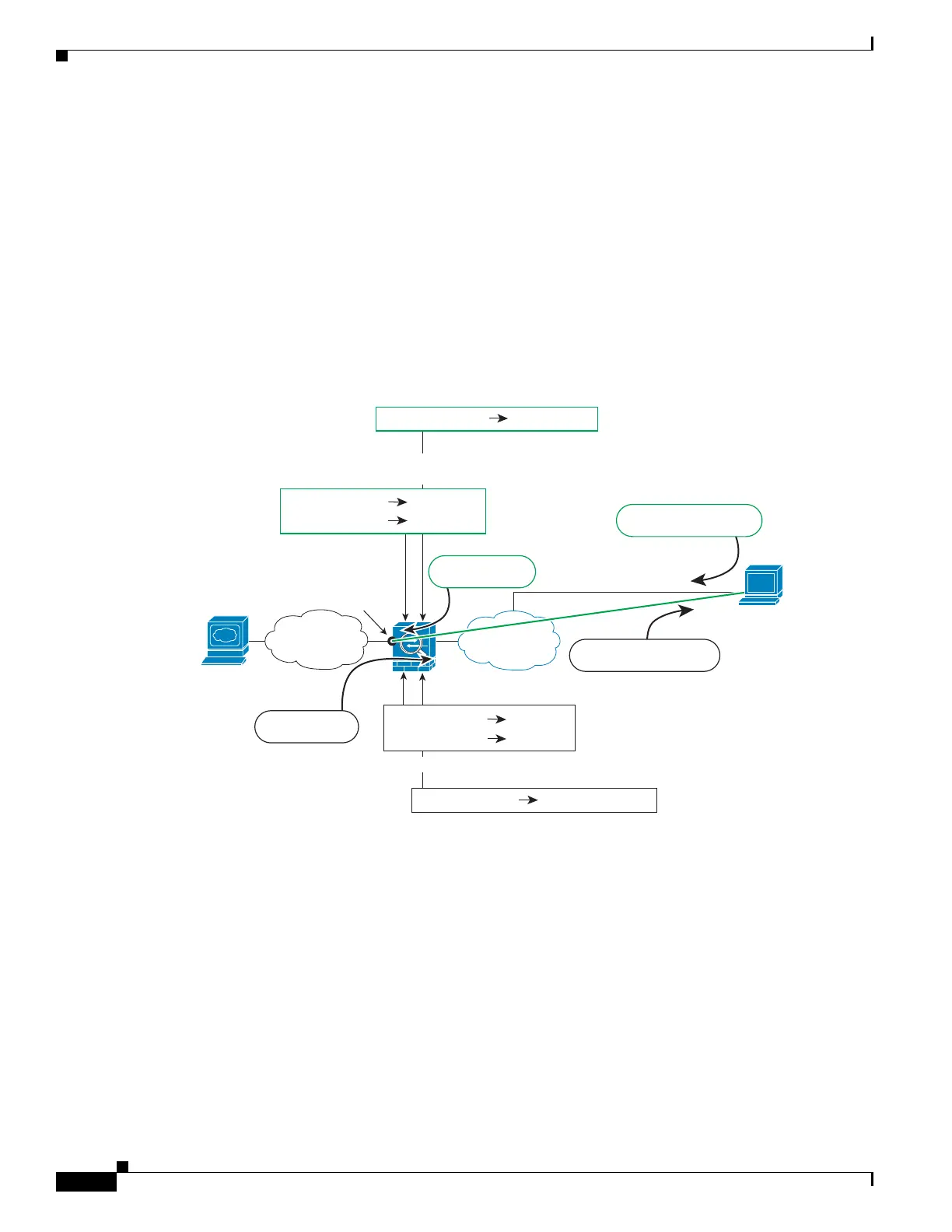
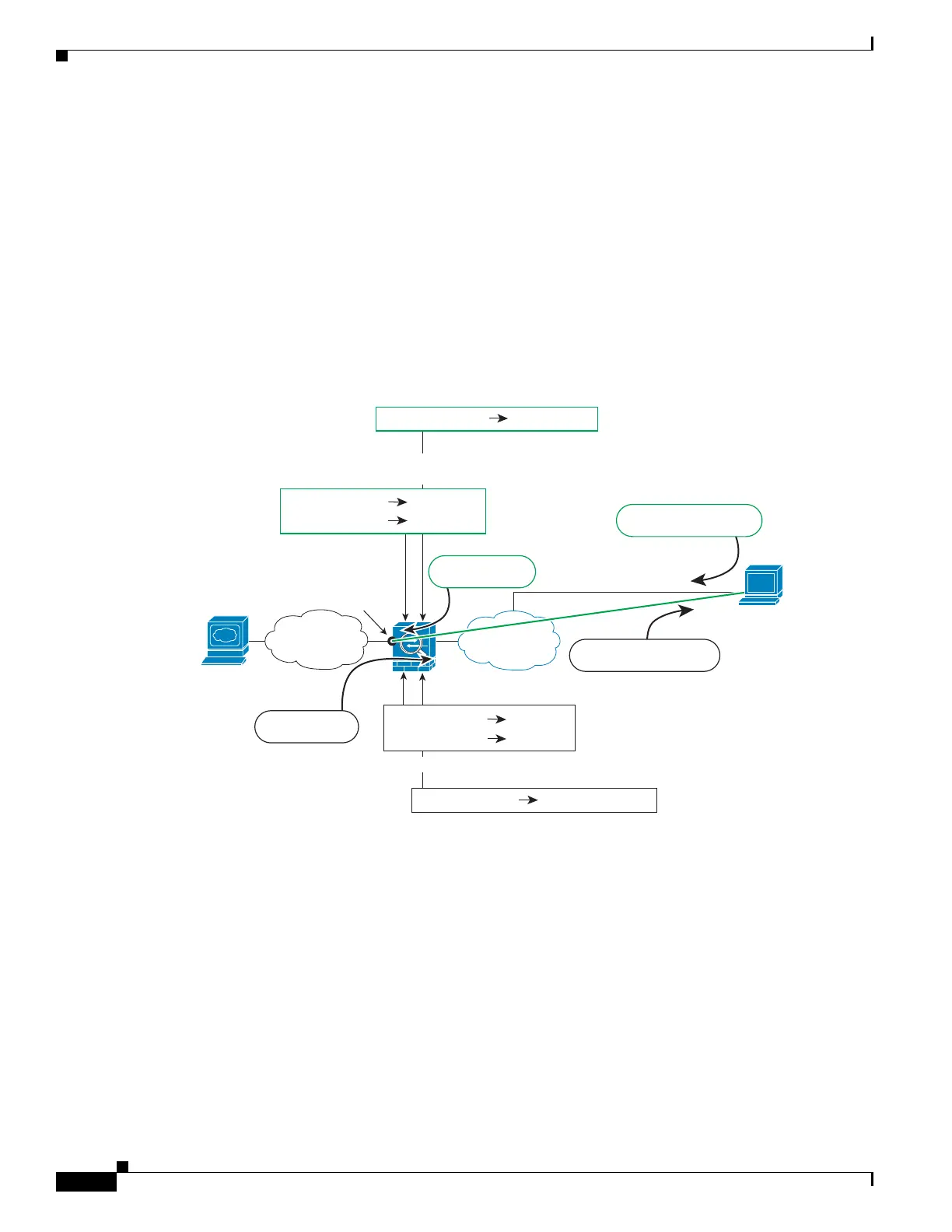
The following figure shows a VPN client Telnetting to the ASA inside interface. When you use a
management-access interface, and you configure identity NAT according to NAT and Remote Access
VPN, page 10-15 or NAT and Site-to-Site VPN, page 10-17, you must configure NAT with the route
lookup option. Without route lookup, the ASA sends traffic out the interface specified in the NAT
command, regardless of what the routing table says; in the below example, the egress interface is the
inside interface. You do not want the ASA to send the management traffic out to the inside network; it
will never return to the inside interface IP address. The route lookup option lets the ASA send the traffic
directly to the inside interface IP address instead of to the inside network. For traffic from the VPN client
to a host on the inside network, the route lookup option will still result in the correct egress interface
(inside), so normal traffic flow is not affected. See the Determining the Egress Interface, page 10-14 for
more information about the route lookup option.
Figure 10-17 VPN Management Access
See the following sample NAT configuration for the above network:
! Enable hairpin for non-split-tunneled VPN client traffic:
same-security-traffic permit intra-interface
! Enable management access on inside ifc:
management-access inside
! Identify local VPN network, & perform object interface PAT when going to Internet:
object network vpn_local
subnet 10.3.3.0 255.255.255.0
nat (outside,outside) dynamic interface
! Identify inside network, & perform object interface PAT when going to Internet:
object network inside_nw
subnet 10.1.1.0 255.255.255.0
nat (inside,outside) dynamic interface
VPN Client
209.165.201.10
Internet
Inside
1. Telnet request to ASA inside ifc;
management-access config req’d
4. Telnet request to 10.1.1.1
2. ASA decrypts packet; src address is now local address
Dst: 10.3.3.10 209.165.201.10
7. ASA encrypts packet; dst address is now real address
10.3.3.10
Src: 209.165.201.10
8. Telnet response to
VPN Client
Dst: 209.165.201.10
Dst: 10.3.3.10
10.1.1.1
Src: 10.1.1.1
10.3.3.10
3. Identity NAT between inside &
VPN client NWs; route-lookup req’d
Src: 10.3.3.10
10.1.1.1
Dst: 10.1.1.1
10.3.3.10209.165.201.10
ASA Inside IP:10.1.1.1
5. Telnet response
to VPN Client
Dst: 10.3.3.10
6. Identity NAT
Src: 10.3.3.10
303461

 Loading...
Loading...