18-11
Cisco ASA Series Firewall CLI Configuration Guide
Chapter 18 Threat Detection
Monitoring Threat Detection
8-hour Sent byte: 367 0 0 10580308
24-hour Sent byte: 122 0 0 10580308
1-hour Sent pkts: 28 0 0 104043
8-hour Sent pkts: 3 0 0 104043
24-hour Sent pkts: 1 0 0 104043
20-min Sent drop: 9 0 1 10851
1-hour Sent drop: 3 0 1 10851
1-hour Recv byte: 2697 0 0 9712670
8-hour Recv byte: 337 0 0 9712670
24-hour Recv byte: 112 0 0 9712670
1-hour Recv pkts: 29 0 0 104846
8-hour Recv pkts: 3 0 0 104846
24-hour Recv pkts: 1 0 0 104846
20-min Recv drop: 42 0 3 50567
1-hour Recv drop: 14 0 1 50567
Host:10.0.0.0: tot-ses:1 act-ses:0 fw-drop:0 insp-drop:0 null-ses:0 bad-acc:0
1-hour Sent byte: 0 0 0 614
8-hour Sent byte: 0 0 0 614
24-hour Sent byte: 0 0 0 614
1-hour Sent pkts: 0 0 0 6
8-hour Sent pkts: 0 0 0 6
24-hour Sent pkts: 0 0 0 6
20-min Sent drop: 0 0 0 4
1-hour Sent drop: 0 0 0 4
1-hour Recv byte: 0 0 0 706
8-hour Recv byte: 0 0 0 706
24-hour Recv byte: 0 0 0 706
1-hour Recv pkts: 0 0 0 7
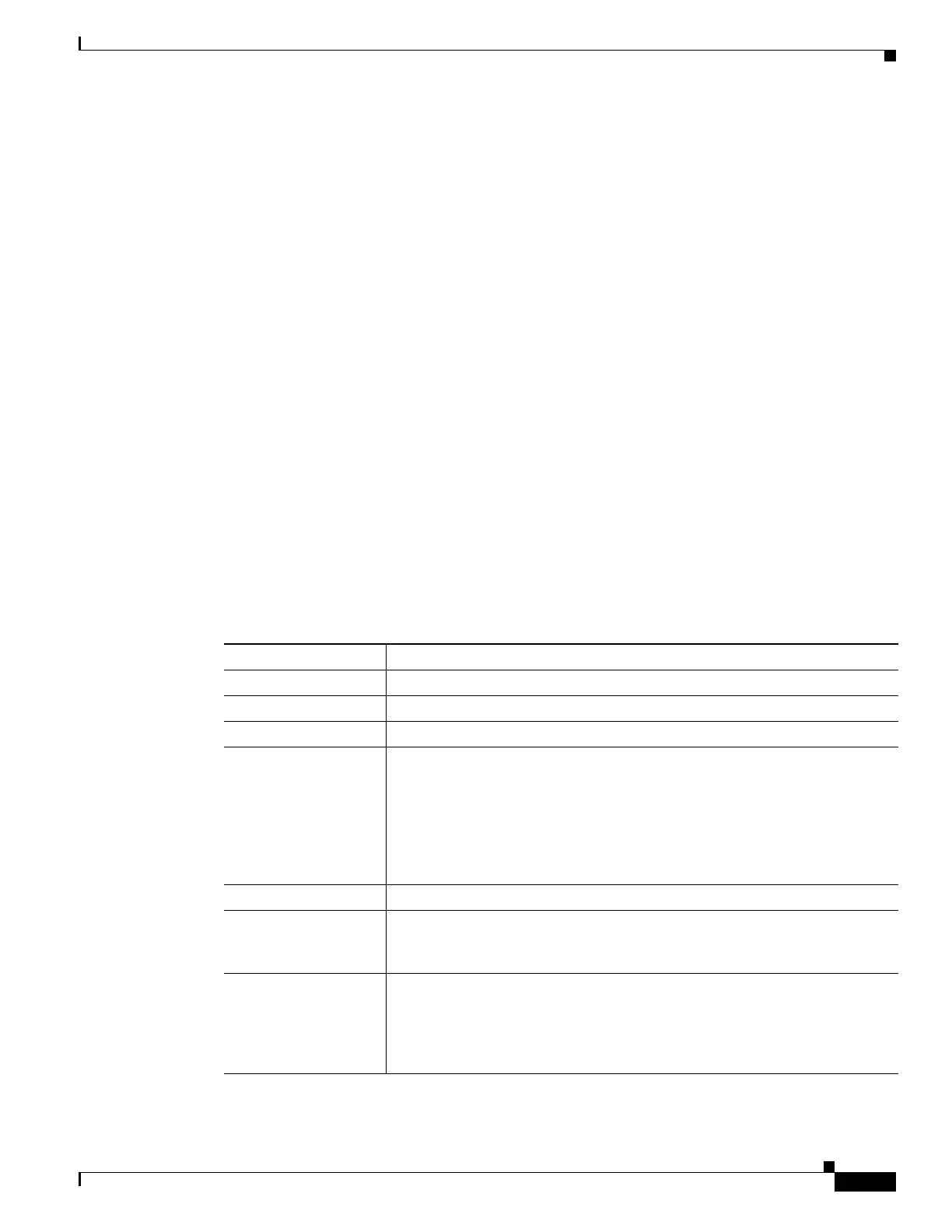
The following table explains the output.
Table 18-3 show threat-detection statistics host
Field Description
Host The host IP address.
tot-ses The total number of sessions for this host since it was added to the database.
act-ses The total number of active sessions that the host is currently involved in.
fw-drop The number of firewall drops. Firewall drops is a combined rate that includes
all firewall-related packet drops tracked in basic threat detection, including
ACL denials, bad packets, exceeded connection limits, DoS attack packets,
suspicious ICMP packets, TCP SYN attack packets, and UDP session with no
return data attack packets. It does not include non-firewall-related drops such
as interface overload, packets failed at application inspection, and scanning
attack detected.
insp-drop The number of packets dropped because they failed application inspection.
null-ses The number of null sessions, which are TCP SYN sessions that did not
complete within the 3-second timeout, and UDP sessions that did not have any
data sent by its server 3 seconds after the session starts.
bad-acc The number of bad access attempts to host ports that are in a closed state.
When a port is determined to be in a null session (see the null-ses field
description), the port state of the host is set to HOST_PORT_CLOSE. Any
client accessing the port of the host is immediately classified as a bad access
without the need to wait for a timeout.

 Loading...
Loading...