RADIUS Authentication and Accounting
Configuring the Switch for RADIUS Authentication
• Determine how many times you want the switch to try contacting a RADIUS server before trying another RADIUS
server or quitting. (This depends on how many RADIUS servers you have configured the switch to access.)
• Determine whether you want to bypass a RADIUS server that fails to respond to requests for service. To shorten
authentication time, you can set a bypass period in the range of 1 to 1440 minutes for non-responsive servers. This
requires that you have multiple RADIUS servers accessible for service requests.
• Optional: Determine whether the switch access level (Manager or Operator) for authenticated clients can be set by
a Service Type value the RADIUS server includes in its authentication message to the switch. (Refer to
“2. Enable the
(Optional) Access Privilege Option” on page 6-12.)
• Configure RADIUS on the server(s) used to support authentication on the switch. For more on this topic, refer to
Configuring the Switch for RADIUS
Authentication
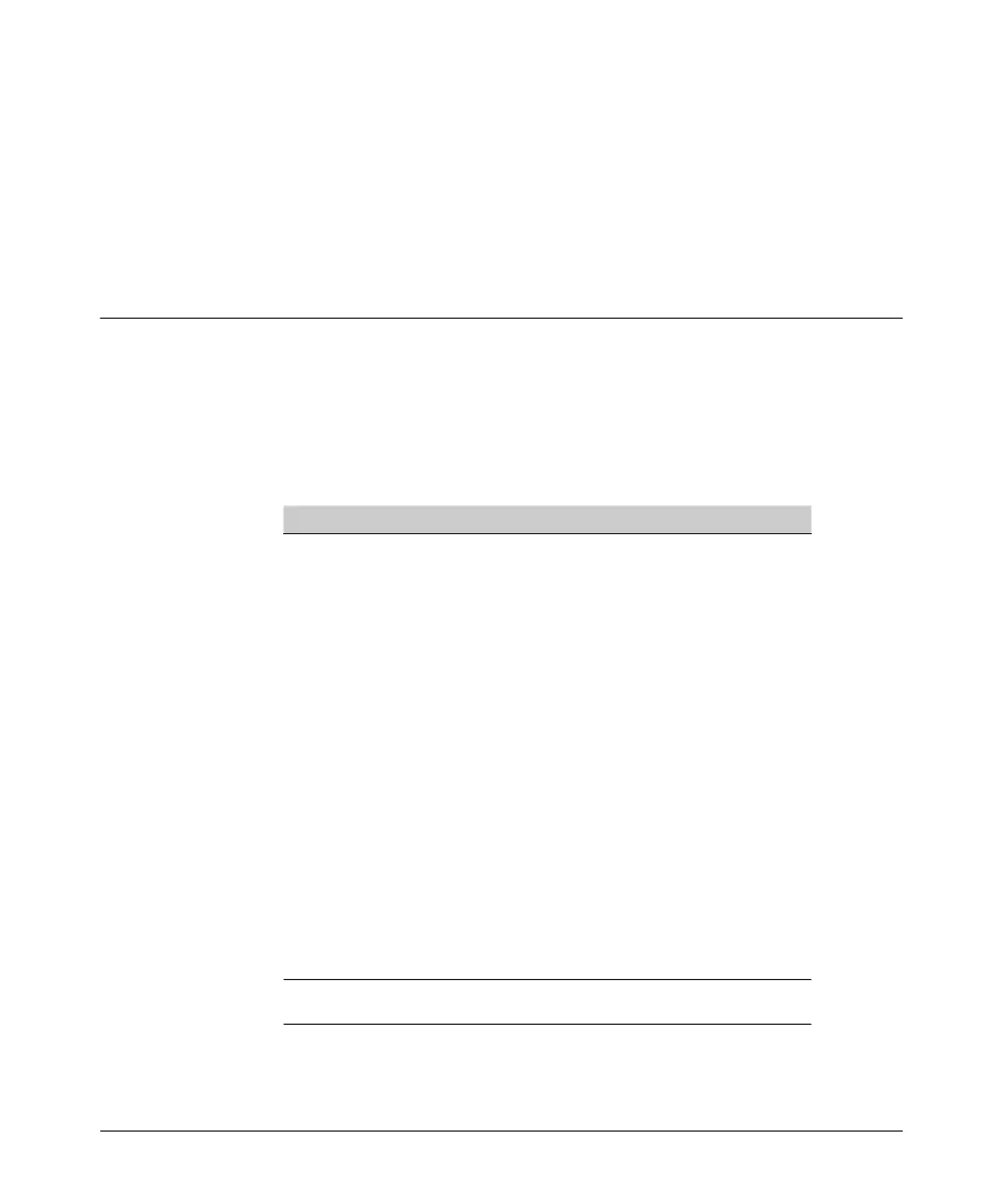
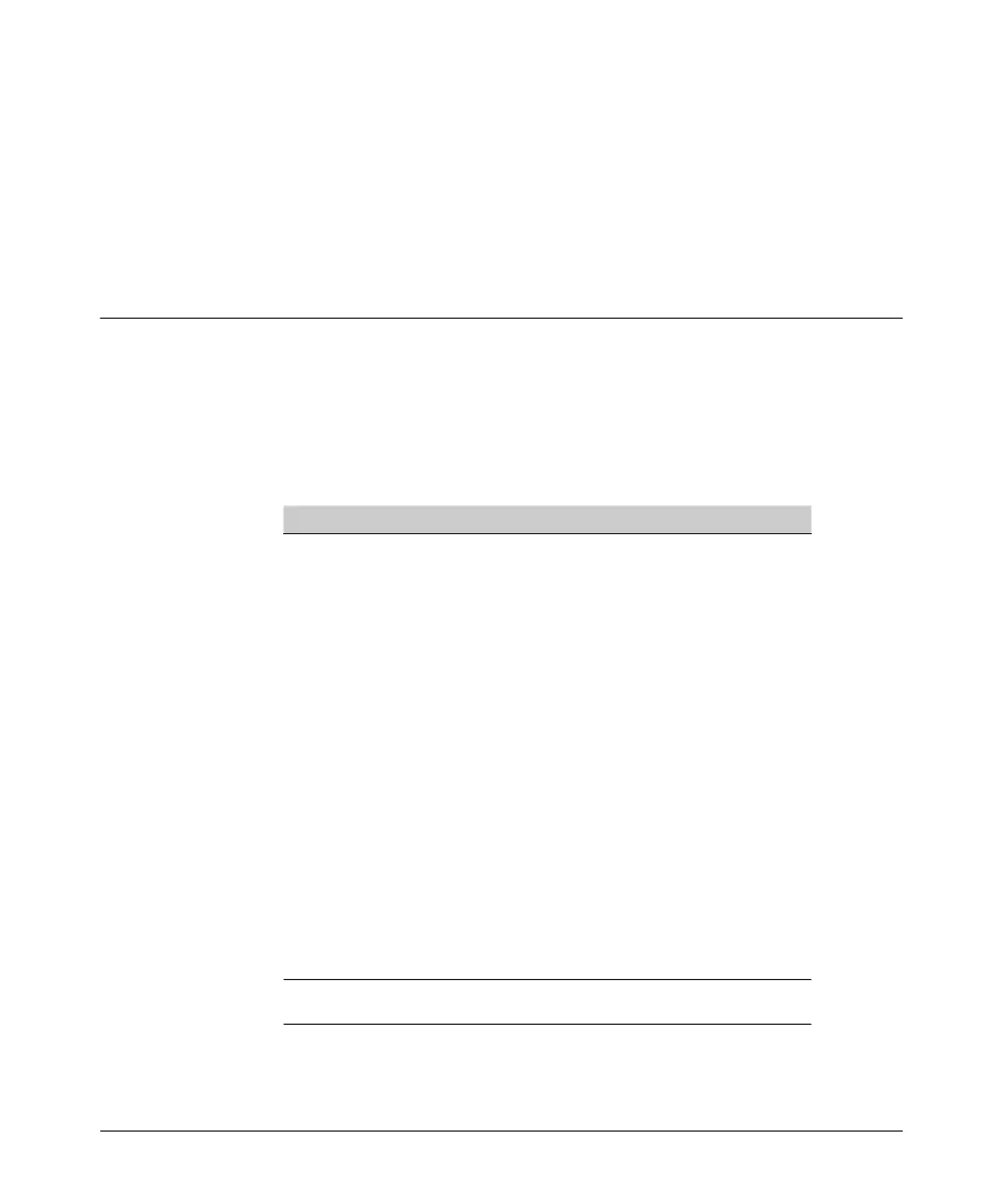
PageRADIUS Authentication Commands
aaa authentication 6-10
< console | telnet | ssh | web > < enable | login > radius* 6-10
[ local | none ] 6-10
[login privilege-mode]* 6-12
[no] radius-server host < IP-address > 6-13
[auth-port < port-number >] 6-13
[acct-port < port-number >] 6-13, 6-51
[key < server-specific key-string >] 6-13
[no] radius-server key < global key-string > 6-16
radius-server timeout < 1 - 15> 6-16
radius-server retransmit < 1 - 5 > 6-16
[no] radius-server dead-time < 1 - 1440 > 6-17
show radius 6-56
[< host < ip-address>] 6-57
show authentication 6-58
show radius authentication 6-58
*The web authentication option for the web browser interface is available on
the 5300xl switches running software release E.09.xx or greater.
6-8

 Loading...
Loading...