1-22
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Digital Certificates
Configuring Digital Certificates
Enabling the Local CA Server
Before enabling the local CA server, you must first create a passphrase of at least seven characters to
encode and archive a PKCS12 file that includes the local CA certificate and keypair to be generated. The
passphrase unlocks the PKCS12 archive if the CA certificate or keypair is lost.
To enable the local CA server, perform the following commands:
Examples
The following example enables the local CA server:
hostname (config)# crypto ca server
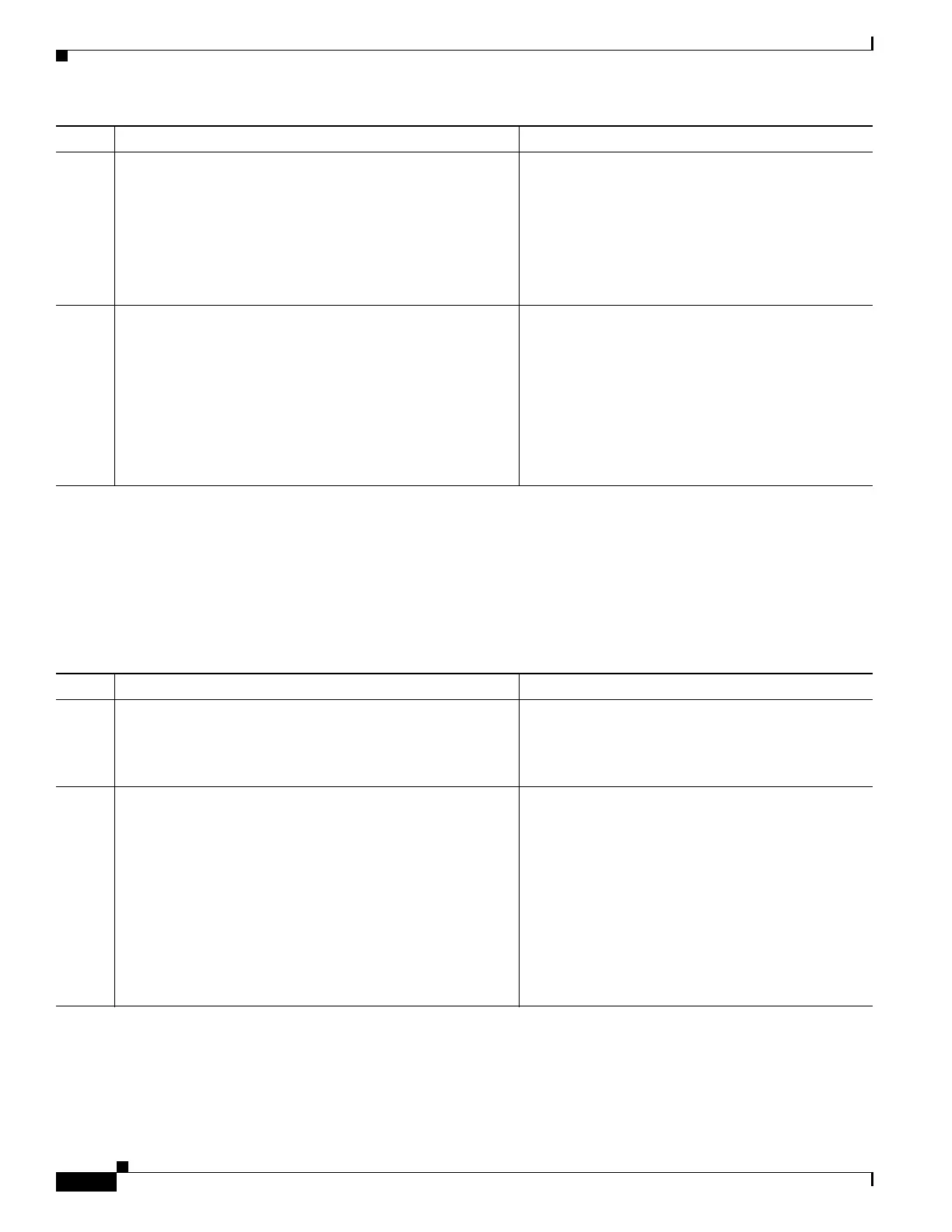
Step 5
secondary-pre-fill-username ssl-client hide
use-common-password password
Example:
hostname(config-tunnel-webvpn)#
secondary-pre-fill-username ssl-client hide
use-common-password secret
Hides the secondary prefill username for
AnyConnect VPN sessions.
Despite the ssl-client keyword inherited from earlier
releases, use this command to support AnyConnect
sessions that use either IKEv2 or SSL.
You must use the hide keyword to support the SCEP
proxy.
Step 6
secondary-username-from-certificate {use-entire-name
| use-script | {primary_attr [secondary-attr]}}
[no-certificate-fallback cisco-secure-desktop
machine-unique-id]
Example:
hostname(config-tunnel-webvpn)#
secondary-username-from-certificate CN
no-certificate-fallback cisco-secure-desktop
machine-unique-id
Supplies the username when a certificate is
unavailable.
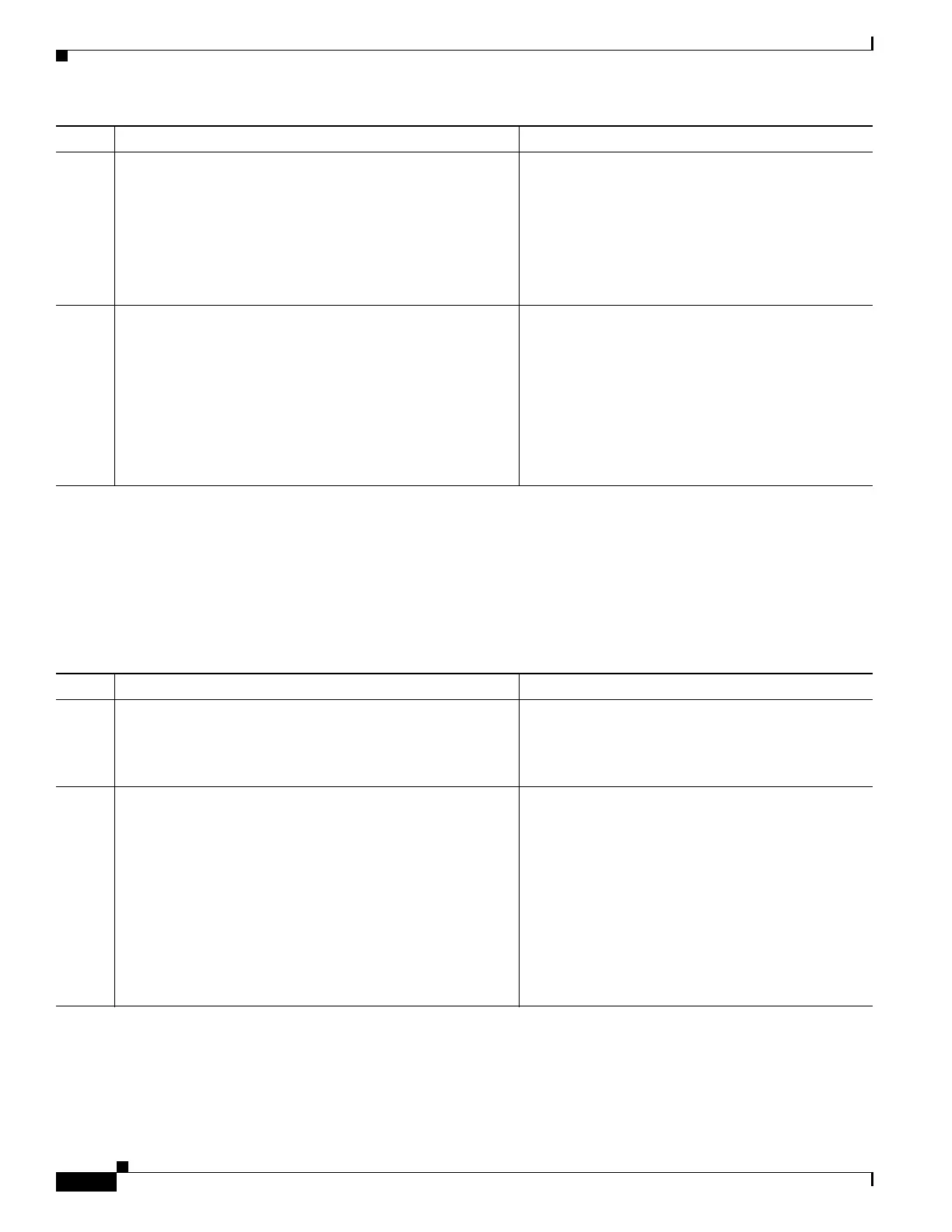
Command Purpose
Command Purpose
Step 1
crypto ca server
Example:
hostname (config)# crypto ca server
Enters local ca server configuration mode. Allows
you to configure and manage a local CA.
Step 2
no shutdown
Example:
hostname (config-ca-server)# no shutdown
Enables the local CA server. Generates the local CA
server certificate, keypair and necessary database
files, and archives the local CA server certificate and
keypair to storage in a PKCS12 file. Requires an 8-65
alphanumeric character password. After initial
startup, you can disable the local CA without being
prompted for the passphrase.
Note After you enable the local CA server, save the
configuration to make sure that the local CA
certificate and keypair are not lost after a
reboot occurs.

 Loading...
Loading...