Access Control Lists (ACLs)
Traffic Management and Improved Network Performance
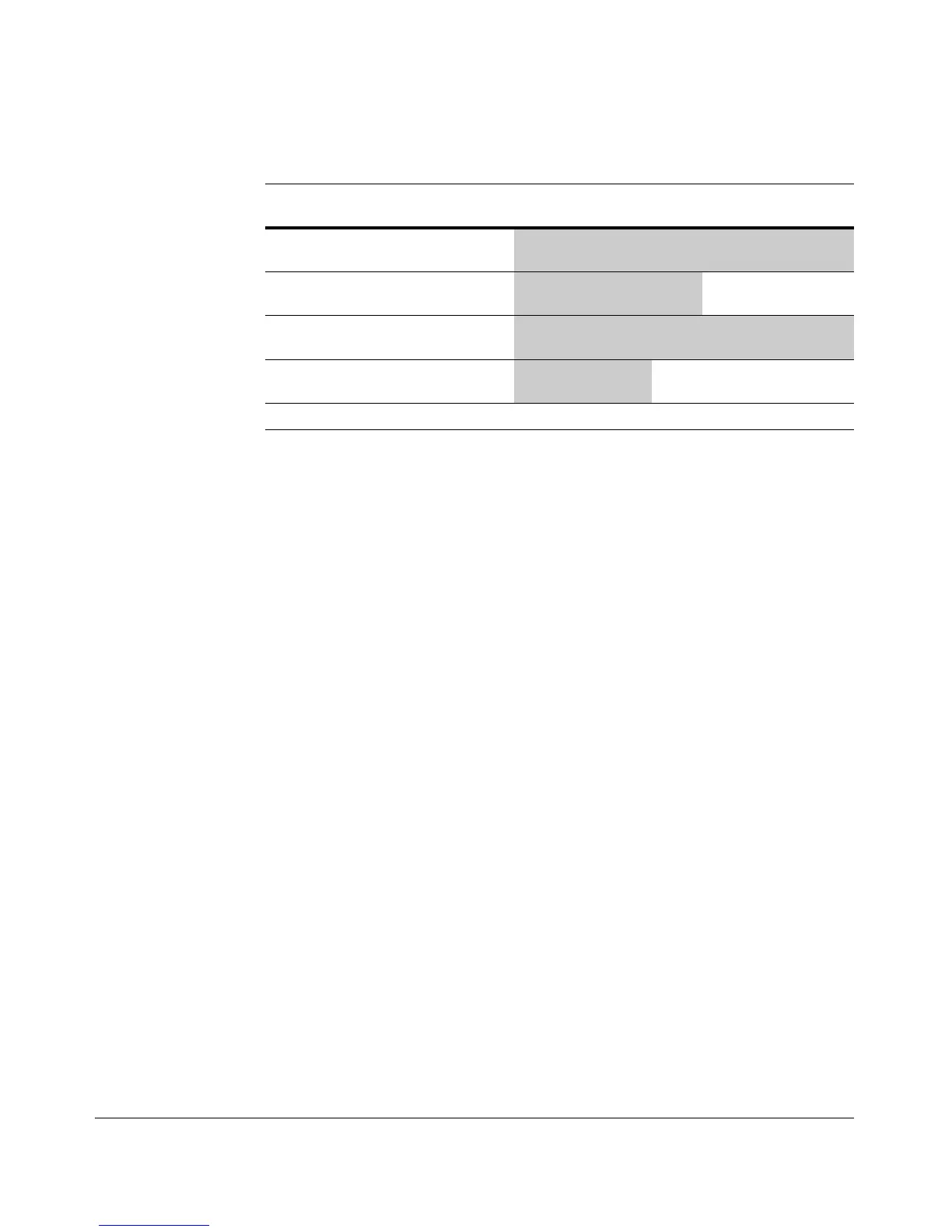
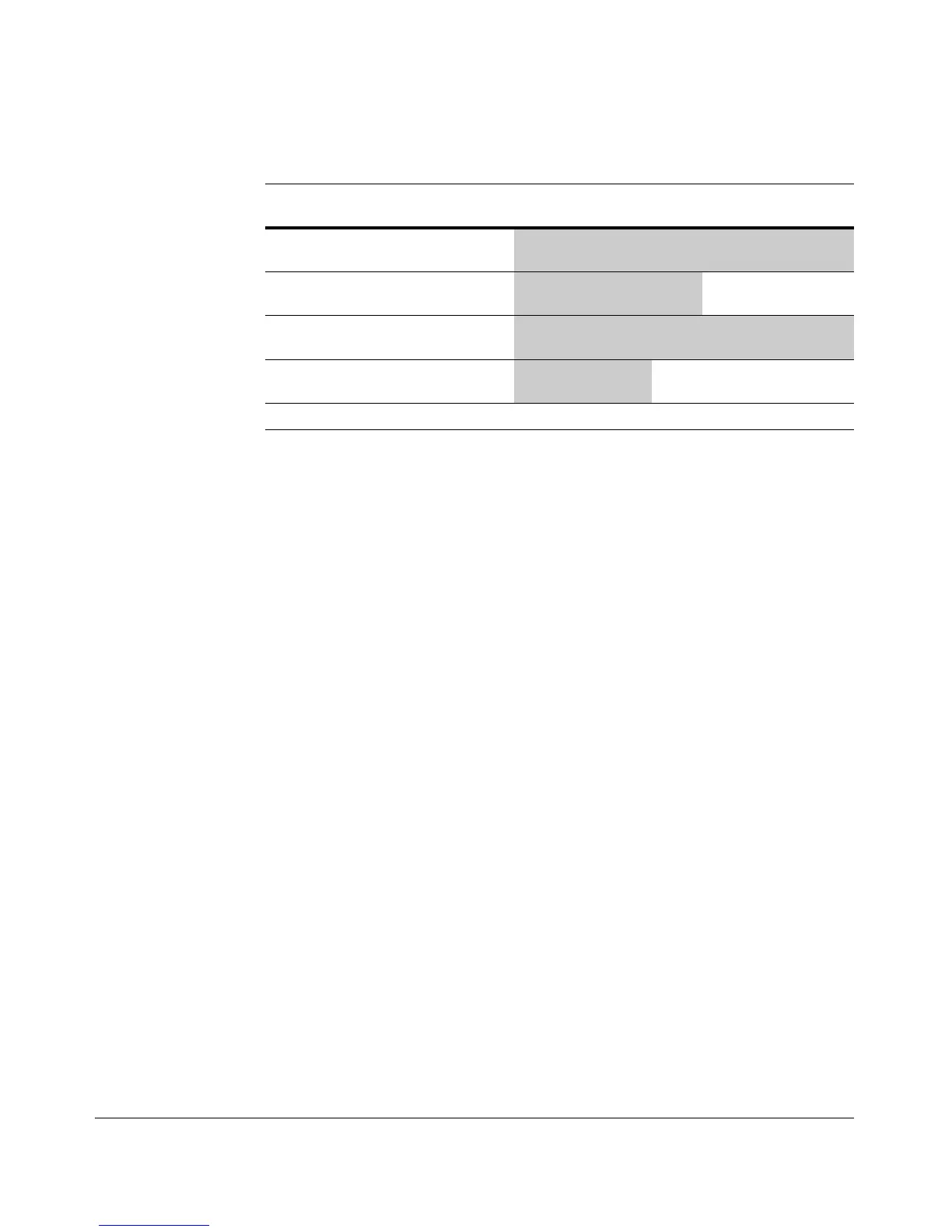
Table 9-5. Mask Effect on Selected Octets of the IP Addresses in Table 9-4
IP Octet Mask Octet 128 64 32 16 8 4 2 1
Addr Range
A 3 0
all bits
252
1 1 1 1 1 1 0 0
B 3 7
last 3 bits
248-255
1 1 1 1 1 0 or 1 0 or 1 0 or 1
C 4 0
all bits
195 1 1 0 0 0 0 1 1
D 2 15
last 4 bits
32-47
0 0 1 0 0 or 1 0 or 1 0 or 1 0 or 1
Shaded areas indicate bit settings that must be an exact match.
If there is a match between the policy in the ACE and the IP address in a packet,
then the packet is either permitted or denied, according to how the ACE is
configured. If there is not a match, the next ACE in the ACL is then applied to
the packet. The same operation applies to a destination IP address (DA) used
in an extended ACE. (Where an ACE includes both source and destination IP
addresses, there is one IP-address/ACL-mask pair for the source address, and
another IP-address/ACL-mask pair for the destination address. See “Configur-
ing and Assigning an ACL” on page 9-32.)
CIDR Notation. For information on using CIDR notation to specify ACL
masks, refer to “Using CIDR Notation To Enter the ACL Mask” on page 9-38.
9-31
 Loading...
Loading...