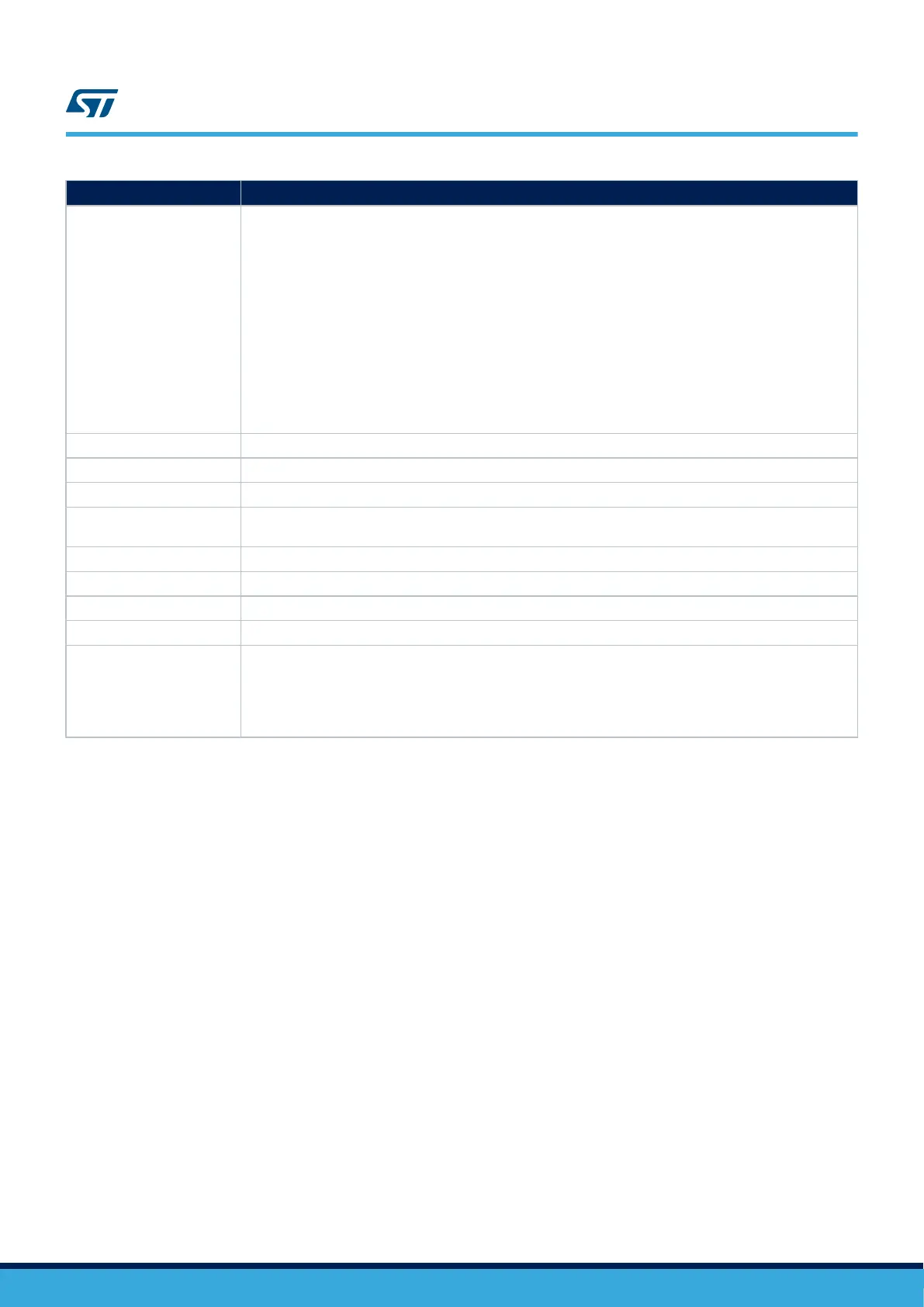
SM CODE CAN_SM_2
Detailed implementation
This method aims to protect the communication between a peripheral and his external counterpart establishing
a kind of “protected” channel. The aim is to specifically address communication failure modes as reported in
IEC61508:2, 7.4.11.1.
Implementation guidelines are the following:
• Data packet must be protected (encapsulated) by an information redundancy check, like for instance a
CRC checksum computed over the packet and added to payload. Checksum encoding capability must
be robust enough to guarantee at least 90% probability of detection for a single bit flip in the data packet.
• Additional field added in payload reporting an unique identification of sender or receiver and an unique
increasing sequence packet number
• Timing monitoring of the message exchange (for example check the message arrival within the expected
time window), detecting therefore missed message arrival conditions
• Application software must verify before consuming data packet its consistency (CRC check), its
legitimacy (sender or receiver) and the sequence correctness (sequence number check, no packets lost)
Error reporting Depends on implementation
Fault detection time Depends on implementation
Addressed fault model Permanent and Transient
Dependency on MCU
configuration
None
Initialization Depends on implementation
Periodicity On demand
Test for the diagnostic Not needed
Multiple faults protection CPU_SM_0: periodical core self-test software
Recommendations and
known limitations
Important note: it is assumed that the remote CAN counterpart has an equivalent capability of performing the
checks described.
A major overlap between the requirements of this method and the implementation of complex communication
software protocols can exists. Due to large adoption of these protocols in industrial applications, optimizations
can be possible
UM1845
Description of hardware and software diagnostics
UM1845 - Rev 4
page 33/108
 Loading...
Loading...