3.6.28 Advanced encryption standard hardware accelerator (AES)
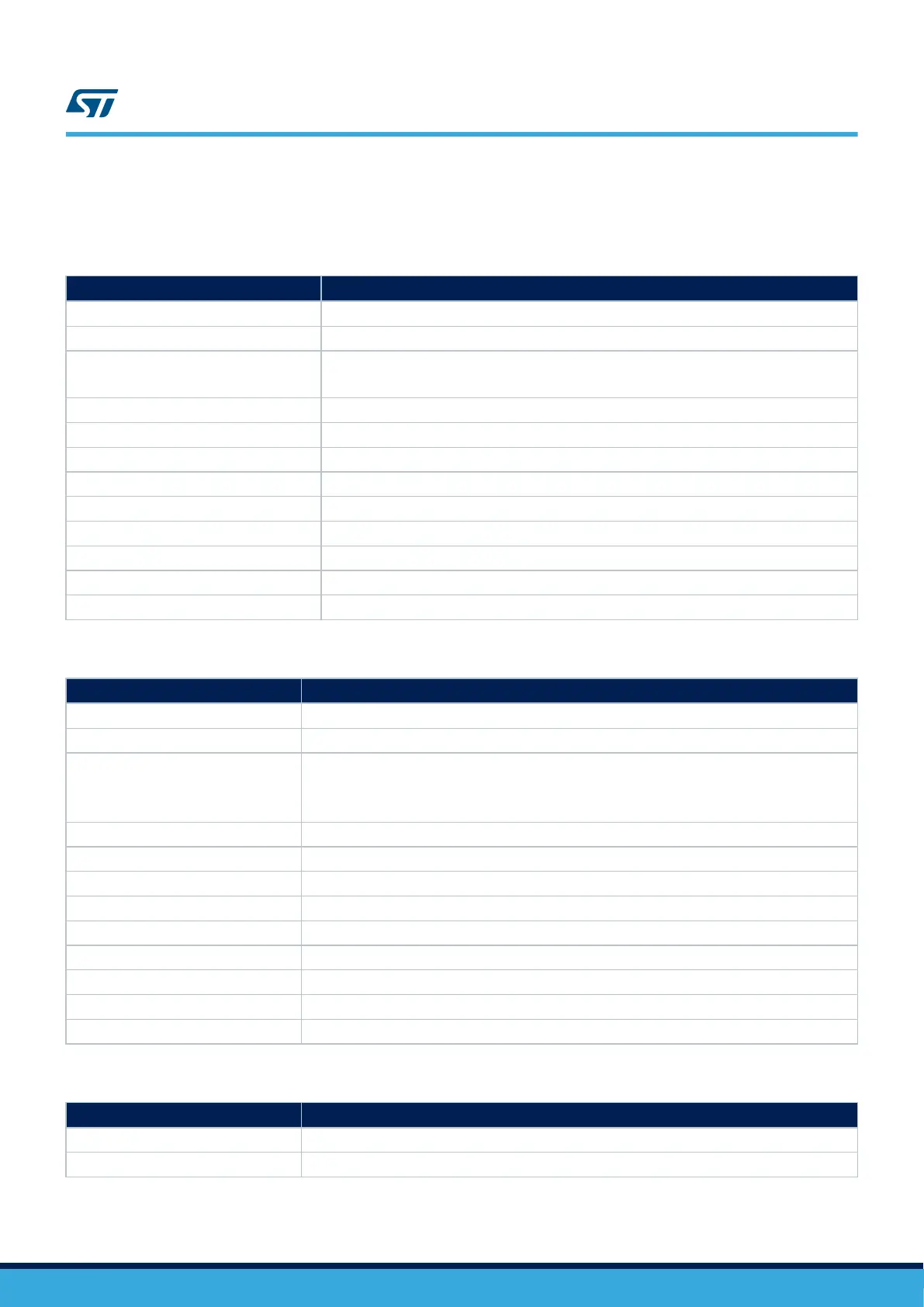
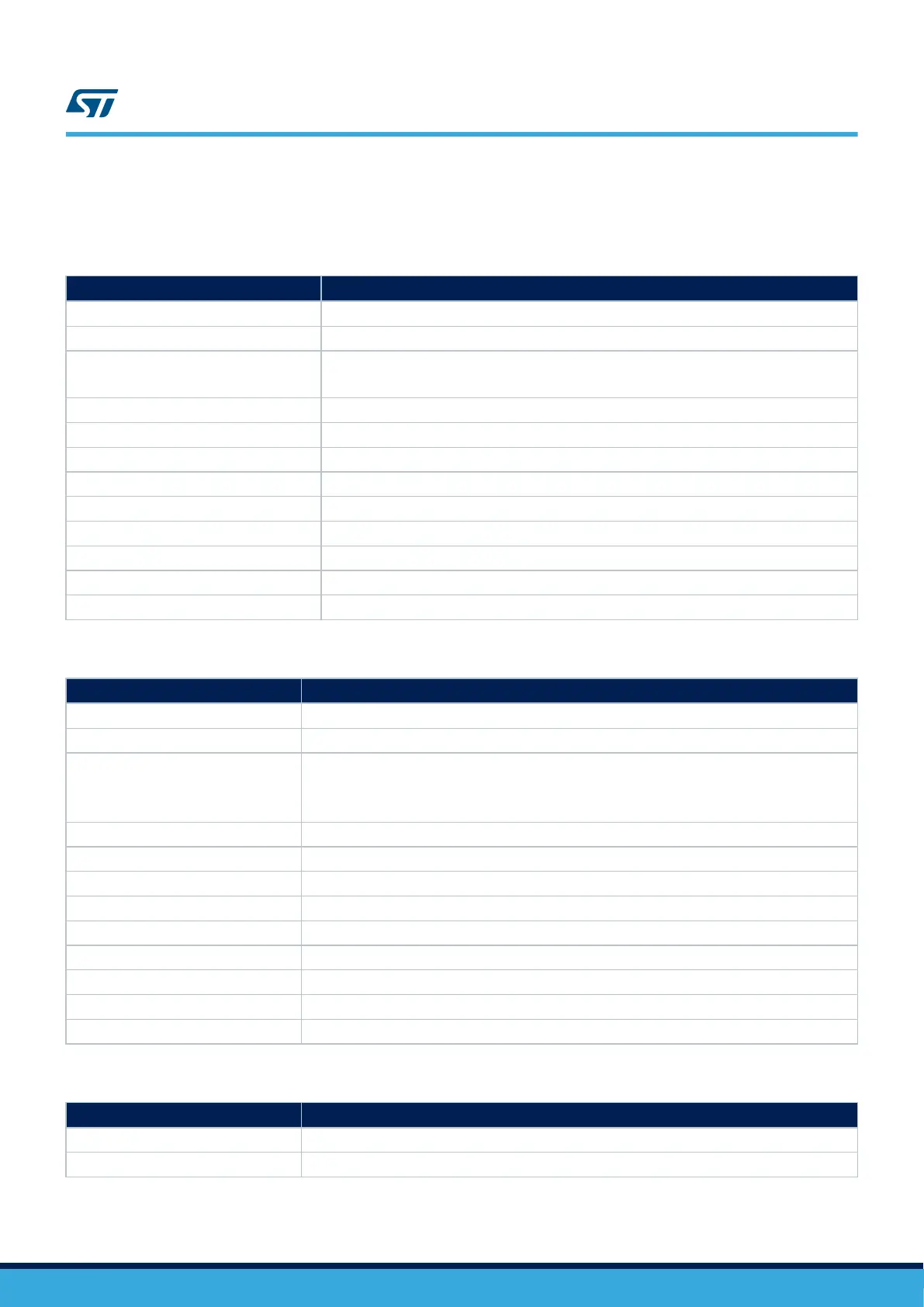
Table 107. AES_SM_0
SM CODE AES_SM_0
Description Periodical read-back of AES configuration registers
Ownership End user
Detailed implementation
This method must be applied to AES configuration registers.
Detailed information on the implementation of this method can be found in Section 3.6.5
Error reporting Refer to NVIC_SM_0
Fault detection time Refer to NVIC_SM_0
Addressed fault model Refer to NVIC_SM_0
Dependency on MCU configuration AES module available only on specific part numbers
Initialization Refer to NVIC_SM_0
Periodicity Refer to NVIC_SM_0
Test for the diagnostic Refer to NVIC_SM_0
Multiple faults protection Refer to NVIC_SM_0
Recommendations and known limitations Refer to NVIC_SM_0
Table 108. AES_SM_1
SM CODE AES_SM_1
Description Encryption/decryption collateral detection
Ownership ST
Detailed implementation
Encryption and decryption operations performed by AES module are composed by several data
manipulations and checks, with different level of complexity according to the selected chaining
algorithm. A major part of the hardware random failures affecting AES module leads to algorithm
violations/errors. Leading to decoding errors on the receiver side
Error reporting Several error condition can happens, check functional documentation
Fault detection time Depends on peripheral configuration
Addressed fault model Permanent and Transient
Dependency on MCU configuration AES module available only on specific part numbers
Initialization Depends on implementation
Periodicity Continuous
Test for the diagnostic N/A
Multiple faults protection AES_SM_2: Information redundancy techniques on messages
Recommendations and known limitations -
Table 109. AES_SM_2
SM CODE AES_SM_2
Description Information redundancy techniques on messages, including end-to-end safing
Ownership End user
UM1845
Description of hardware and software diagnostics
UM1845 - Rev 4
page 72/108

 Loading...
Loading...