Creating an Access Control Policy
Next Generation Security Gateway Guide R80.20 | 136
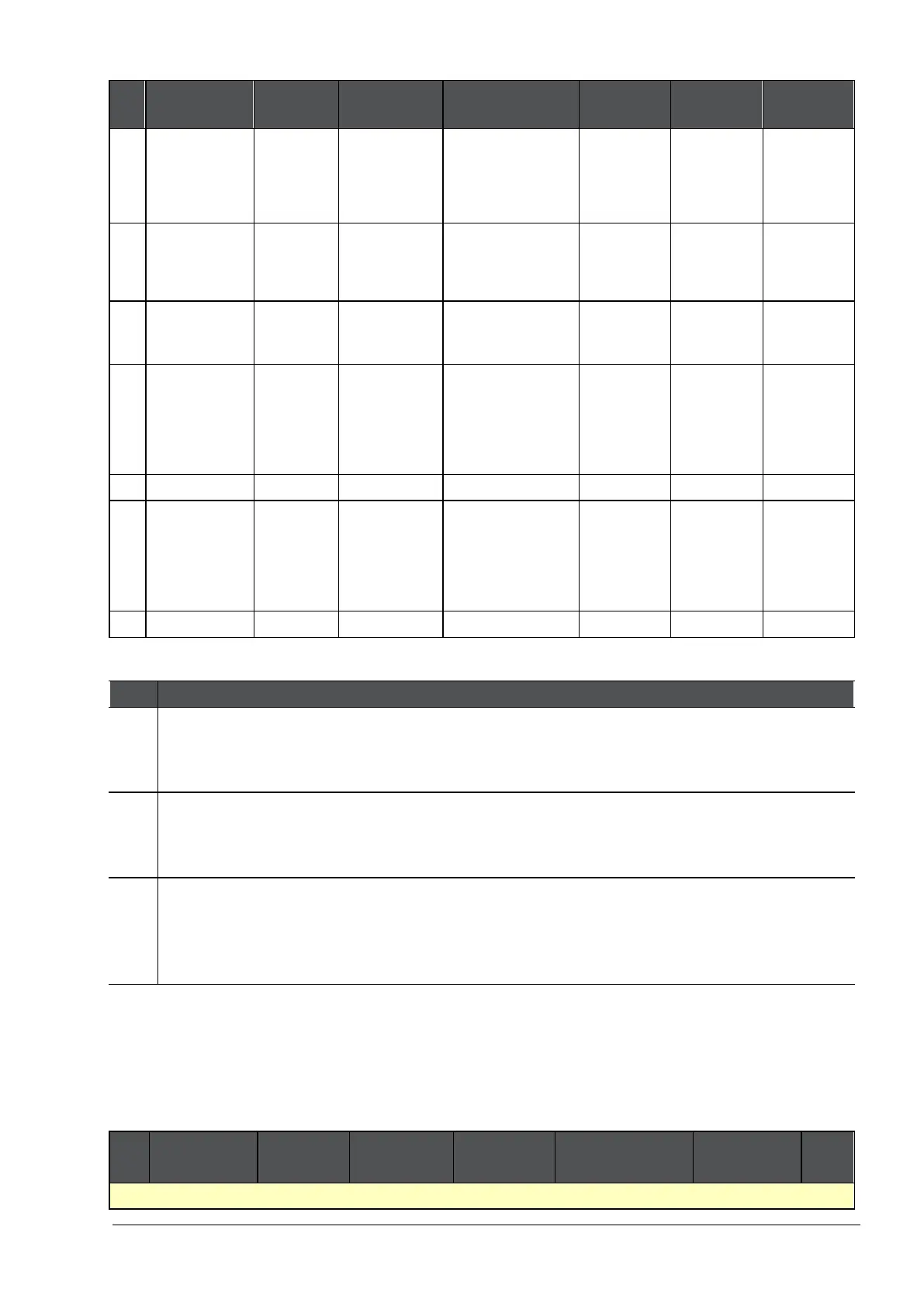
No Name Source Destination Services &
Content Action Track
4.1
Block browsing
with unapproved
browsers
Any Any NEGATED
Google Chrome
Internet Explorer 11
Firefox
Safari
Any Drop Log
4.2
Inform user when
uploading Credit
Cards only over
HTTPS
Any Any https Upload Traffic
PCI - Credit
Card Numbers
Inform
Access Noti...
once a day
per applic...
Log
4.3
Block Credit
Cards
Any Any Any Any Direction
PCI - Credit
Card Numbers
Drop
Block
Message
Log
4.4
Block
downloading of
sensitive content
Any Any Any
Download
Traffic
HIPAA -
Medical
Record
Headers
Drop Log
4.5 Cleanup rule Any Any Any Any Accept None
5
Ask user when
sending credit
cards to PayPal
InternalZone Internet PayPal Any Direction
PCI - Credit
Card Numbers
Ask
Company
Policy
Access Noti...
once a day
per applic...
Log
6 Cleanup rule Any Any Any Any Drop Log
4 This is the parent rule of the Inline Layer. The Action is the name of the Inline Layer. If a
packet matches on the parent rule, the matching continues to rule 4.1 of the Inline Layer. If
a packet does not match on the parent rule, the matching continues to rule 5.
4.1
-4.4
If a packet matches on rule 4.1, the rule action is done on the packet, and no more rule
matching is done. If a packet does not match on rule 4.1, continue to rule 4.2. The same
logic applies to the remaining rules in the Inline Layer.
4.5 If none of the higher rules in the Ordered Layer match the packet, the explicit
Cleanup
Rule
is applied. The
Cleanup rule
is a default explicit rule. You can change or delete it. We
recommend that you have an explicit cleanup rule as the last rule in each Inline Layer and
Ordered Layer.
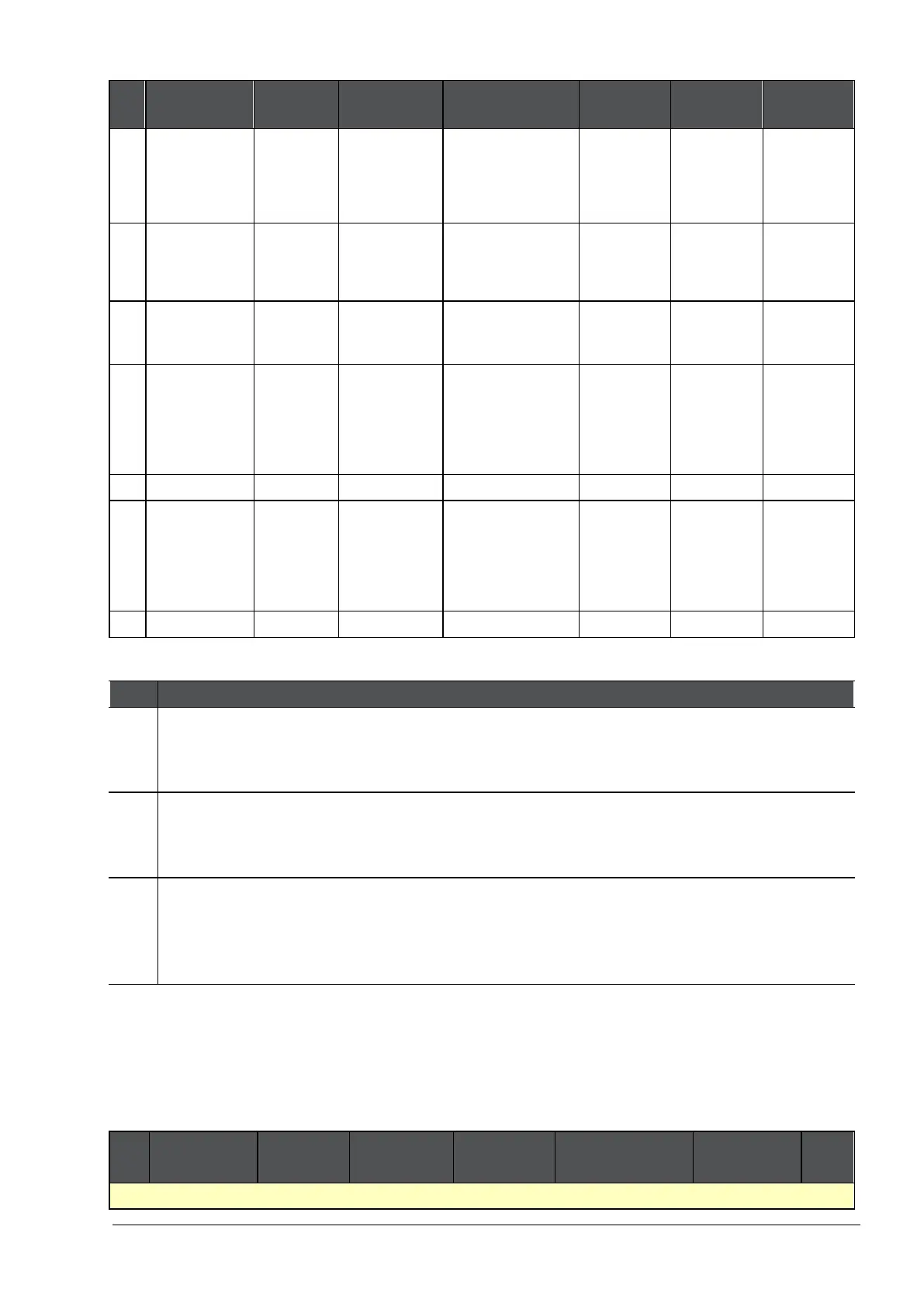
Use Case - Content Awareness Ordered Layer
This use case shows a Policy that controls the upload and download of data from and to the
organization.
There is an explanation of some of the rules below the Rule Base.
No Name Source Destination Services &
Applications
Content Action Track
Regulatory compliance
 Loading...
Loading...