17-20
Cisco Security Appliance Command Line Configuration Guide
OL-10088-01
Chapter 17 Applying NAT
Using Dynamic NAT and PAT
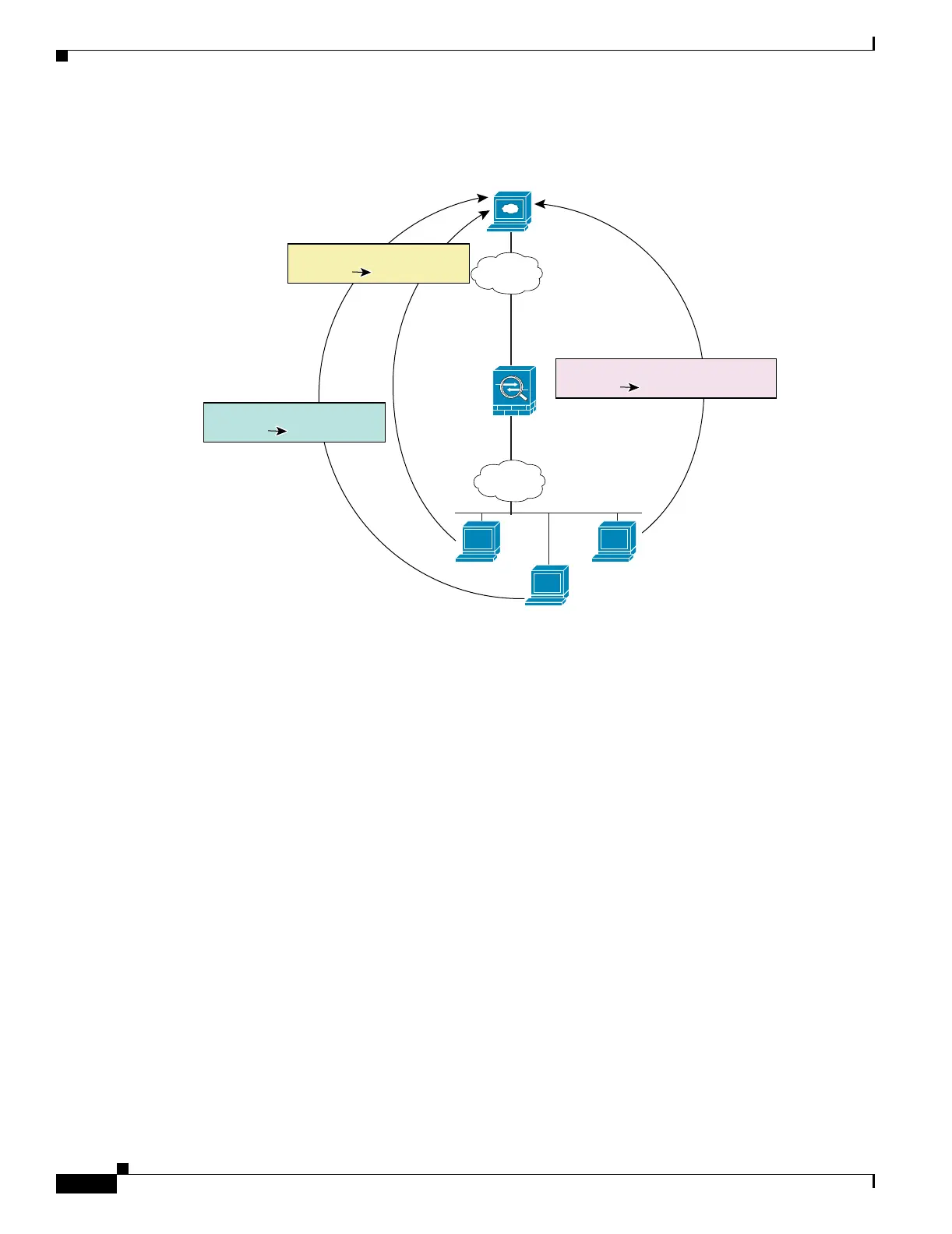
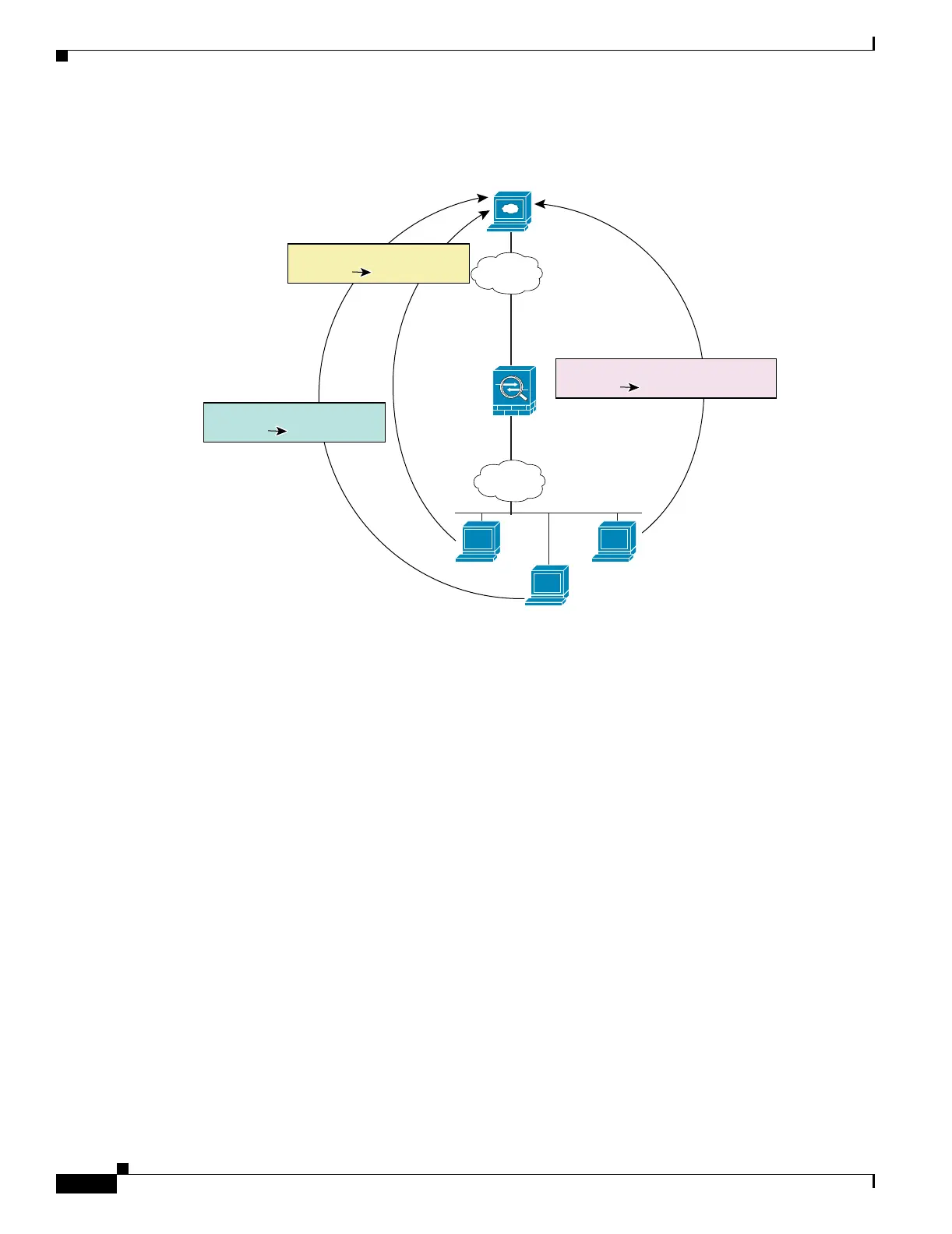
Figure 17-17 NAT and PAT Together
See the following commands for this example:
hostname(config)# nat (inside) 1 10.1.2.0 255.255.255.0
hostname(config)# global (outside) 1 209.165.201.3-209.165.201.4
hostname(config)# global (outside) 1 209.165.201.5
For outside NAT, you need to identify the nat command for outside NAT (the outside keyword). If you
also want to translate the same traffic when it accesses an inside interface (for example, traffic on a DMZ
is translated when accessing the Inside and the Outside interfaces), then you must configure a separate
nat command without the outside option. In this case, you can identify the same addresses in both
statements and use the same NAT ID (see Figure 17-18). Note that for outside NAT (DMZ interface to
Inside interface), the inside host uses a static command to allow outside access, so both the source and
destination addresses are translated.
Web Server:
www.cisco.com
Outside
Inside
Global 1: 209.165.201.3-
209.165.201.4
Global 1: 209.165.201.5
NAT 1: 10.1.2.0/24
10.1.2.27
10.1.2.28
10.1.2.29
130026
Translation
209.165.201.310.1.2.27
Translation
209.165.201.410.1.2.28
Translation
209.165.201.5:609610.1.2.29

 Loading...
Loading...