xxxv
Cisco Security Appliance Command Line Configuration Guide
OL-10088-01
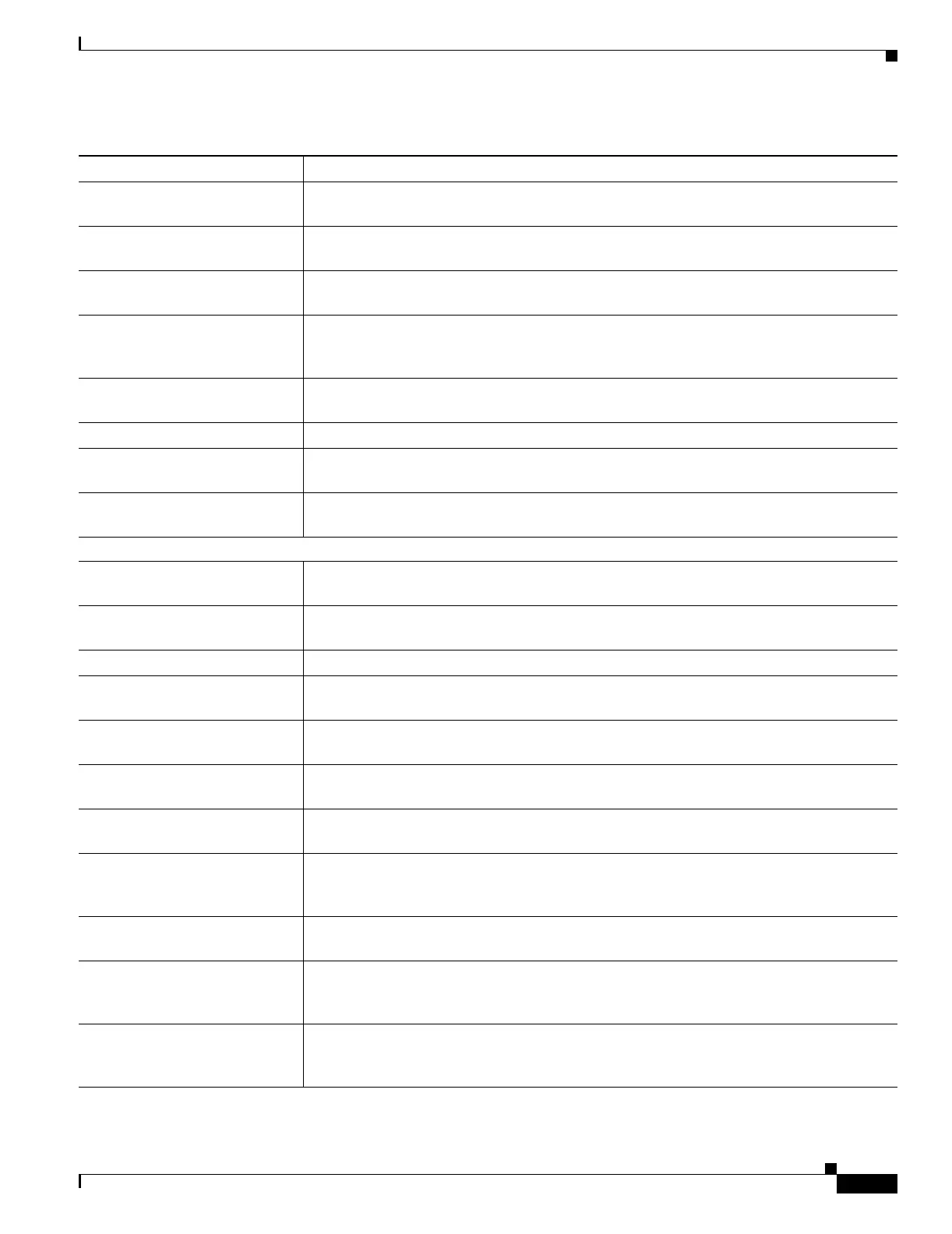
About This Guide
Document Organization
Chapter 7, “Configuring
Interface Parameters”
Describes how to configure each interface and subinterface for a name, security, level, and
IP address.
Chapter 8, “Configuring Basic
Settings”
Describes how to configure basic settings that are typically required for a functioning
configuration.
Chapter 9, “Configuring IP
Routing”
Describes how to configure IP routing.
Chapter 10, “Configuring
DHCP, DDNS, and WCCP
Services”
Describes how to configure the DHCP server and DHCP relay.
Chapter 11, “Configuring
Multicast Routing”
Describes how to configure multicast routing.
Chapter 12, “Configuring IPv6” Describes how to enable and configure IPv6.
Chapter 13, “Configuring AAA
Servers and the Local Database”
Describes how to configure AAA servers and the local database.
Chapter 14, “Configuring
Failover”
Describes the failover feature, which lets you configure two security appliances so that one
will take over operation if the other one fails.
Part 2: Configuring the Firewall
Chapter 15, “Firewall Mode
Overview”
Describes in detail the two operation modes of the security appliance, routed and
transparent mode, and how data is handled differently with each mode.
Chapter 16, “Identifying Traffic
with Access Lists”
Describes how to identify traffic with access lists.
Chapter 17, “Applying NAT” Describes how address translation is performed.
Chapter 18, “Permitting or
Denying Network Access”
Describes how to control network access through the security appliance using access lists.
Chapter 19, “Applying AAA for
Network Access”
Describes how to enable AAA for network access.
Chapter 20, “Applying Filtering
Services”
Describes ways to filter web traffic to reduce security risks or prevent inappropriate use.
Chapter 21, “Using Modular
Policy Framework”
Describes how to use the Modular Policy Framework to create security policies for TCP,
general connection settings, inspection, and QoS.
Chapter 22, “Managing AIP
SSM and CSC SSM”
Describes how to configure the security appliance to send traffic to an AIP SSM or a CSC
SSM, how to check the status of an SSM, and how to update the software image on an
intelligent SSM.
Chapter 23, “Preventing
Network Attacks”
Describes how to configure protection features to intercept and respond to network attacks.
Chapter 24, “Applying QoS
Policies”
Describes how to configure the network to provide better service to selected network
traffic over various technologies, including Frame Relay, Asynchronous Transfer Mode
(ATM), Ethernet and 802.1 networks, SONET, and IP routed networks.
Chapter 25, “Configuring
Application Layer Protocol
Inspection”
Describes how to use and configure application inspection.
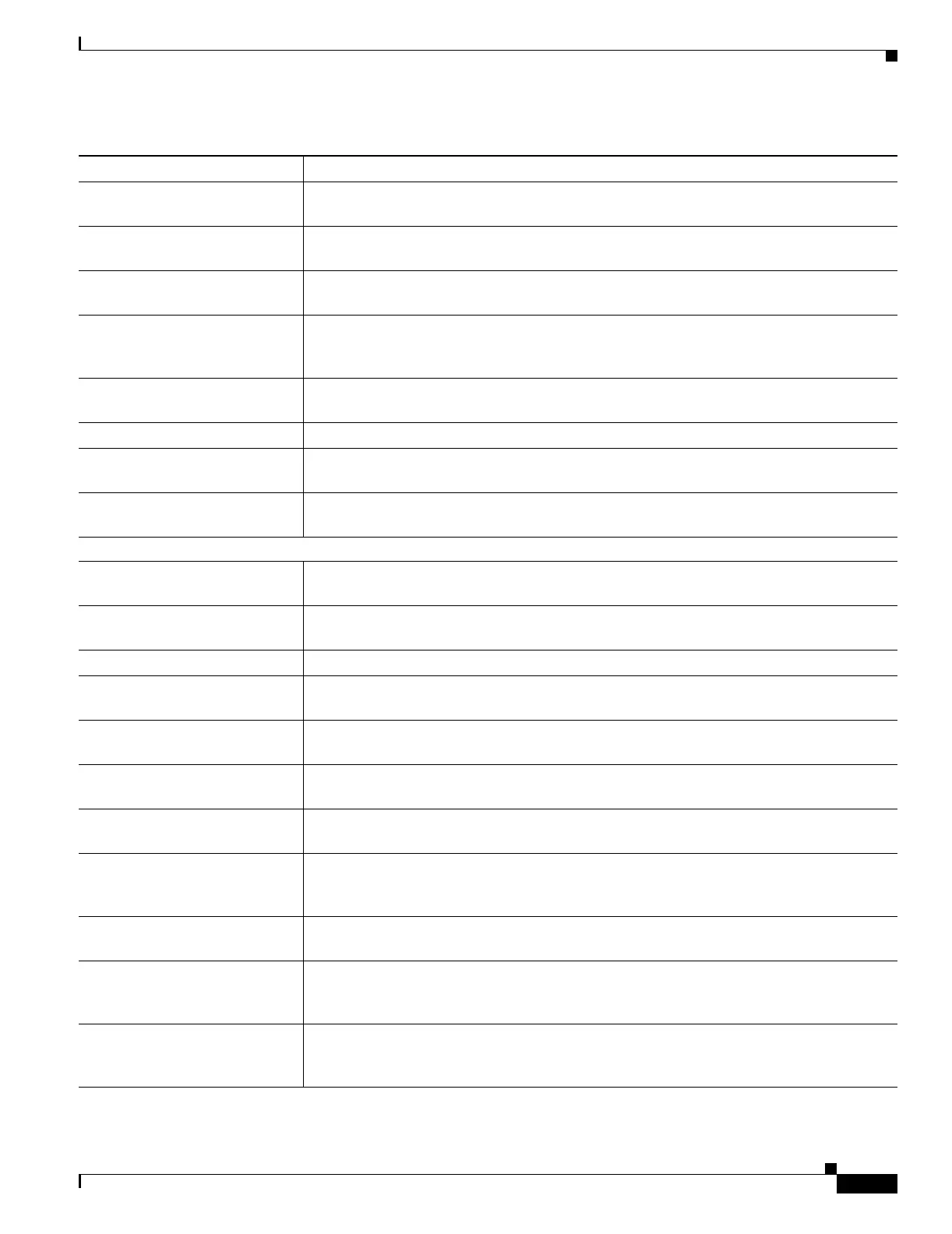
Table 1 Document Organization (continued)
Chapter/Appendix Definition

 Loading...
Loading...