34-13
Cisco IE 3000 Switch Software Configuration Guide
OL-13018-03
Chapter 34 Configuring Network Security with ACLs
Configuring IPv4 ACLs
To remove a named standard ACL, use the no ip access-list standard name global configuration
command.
Beginning in privileged EXEC mode, follow these steps to create an extended ACL using names:
To remove a named extended ACL, use the no ip access-list extended name global configuration
command.
When you are creating standard extended ACLs, remember that, by default, the end of the ACL contains
an implicit deny statement for everything if it did not find a match before reaching the end. For standard
ACLs, if you omit the mask from an associated IP host address access list specification, 0.0.0.0 is
assumed to be the mask.
After you create an ACL, any additions are placed at the end of the list. You cannot selectively add ACL
entries to a specific ACL. However, you can use no permit and no deny access-list configuration mode
commands to remove entries from a named ACL. This example shows how you can delete individual
ACEs from the named access list border-list:
Switch(config)# ip access-list extended border-list
Switch(config-ext-nacl)# no permit ip host 10.1.1.3 any
Being able to selectively remove lines from a named ACL is one reason you might use named ACLs
instead of numbered ACLs.
After creating a named ACL, you can apply it to interfaces (see the “Applying an IPv4 ACL to an
Interface” section on page 34-16).
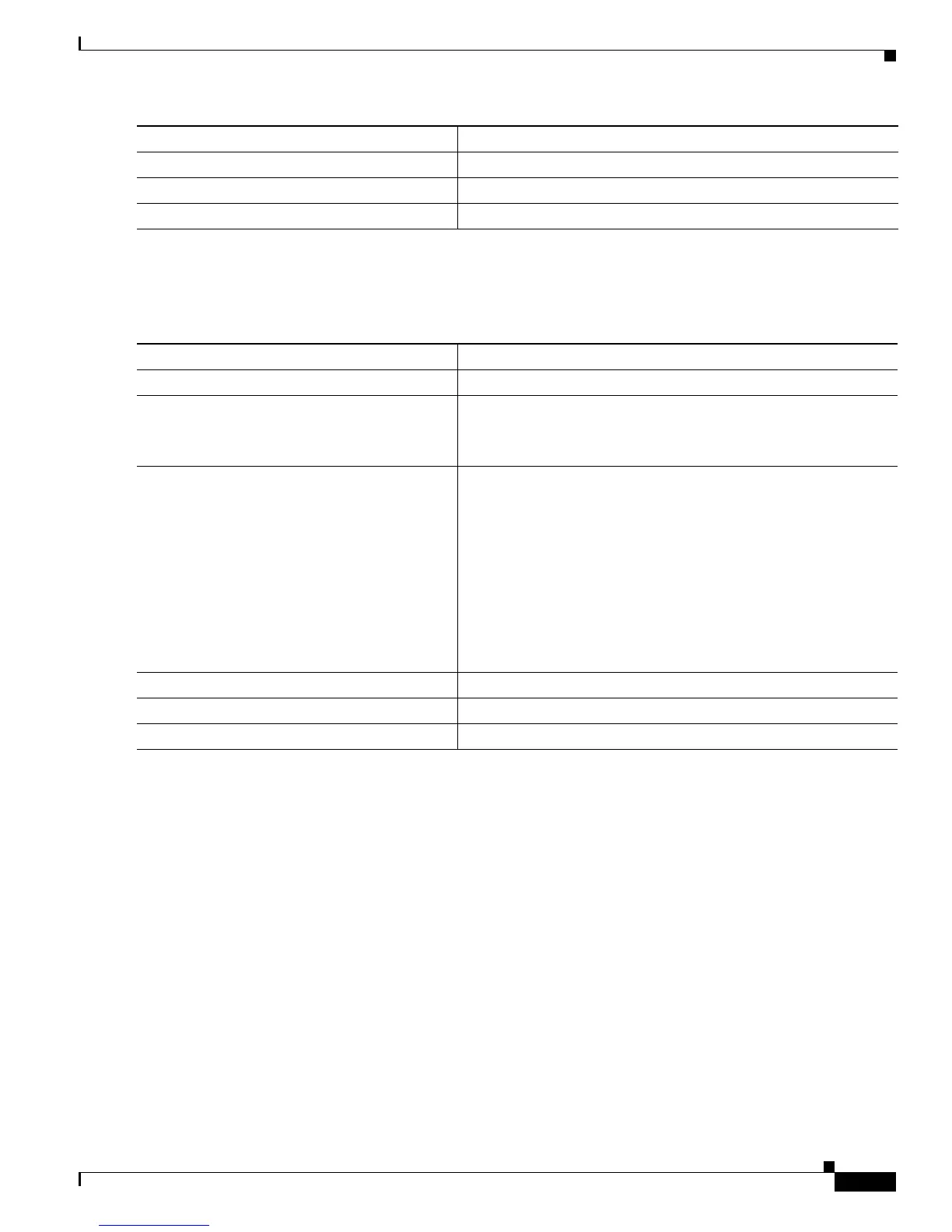
Step 4
end Return to privileged EXEC mode.
Step 5
show access-lists [number | name] Show the access list configuration.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.
Command Purpose
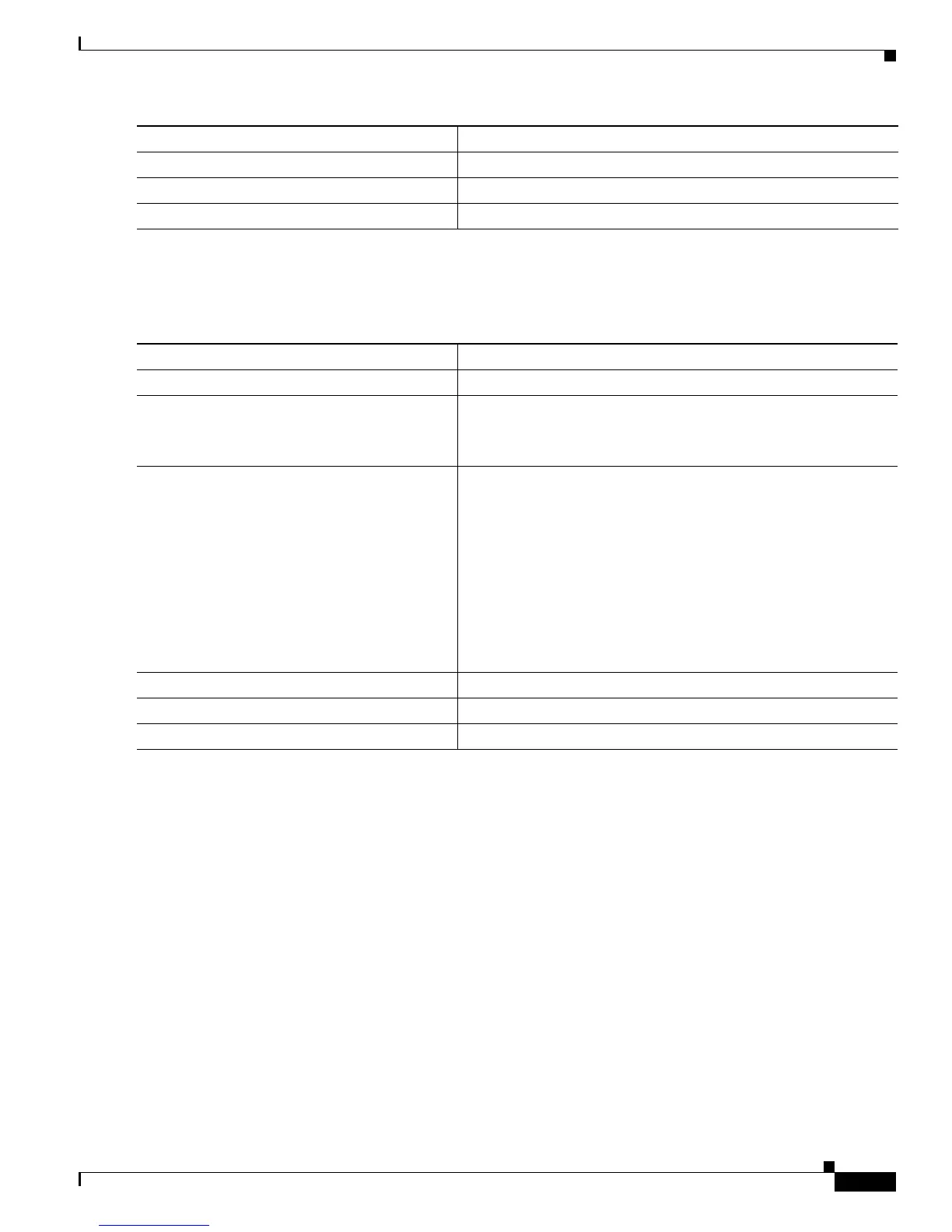
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
ip access-list extended name Define an extended IPv4 access list using a name, and enter
access-list configuration mode.
The name can be a number from 100 to 199.
Step 3
{deny | permit} protocol {source
[source-wildcard] | host source | any}
{destination [destination-wildcard] | host
destination | any} [precedence precedence]
[tos tos] [established] [time-range
time-range-name]
In access-list configuration mode, specify the conditions allowed
or denied.
See the “Creating a Numbered Extended ACL” section on
page 34-8 for definitions of protocols and other keywords.
• host source—A source and source wildcard of source 0.0.0.0.
• host destination—A destination and destination wildcard of
destination 0.0.0.0.
• any—A source and source wildcard or destination and
destination wildcard of 0.0.0.0 255.255.255.255.
Step 4
end Return to privileged EXEC mode.
Step 5
show access-lists [number | name] Show the access list configuration.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.

 Loading...
Loading...