302
Dynamic IPv6 source guard using ND snooping configuration
example
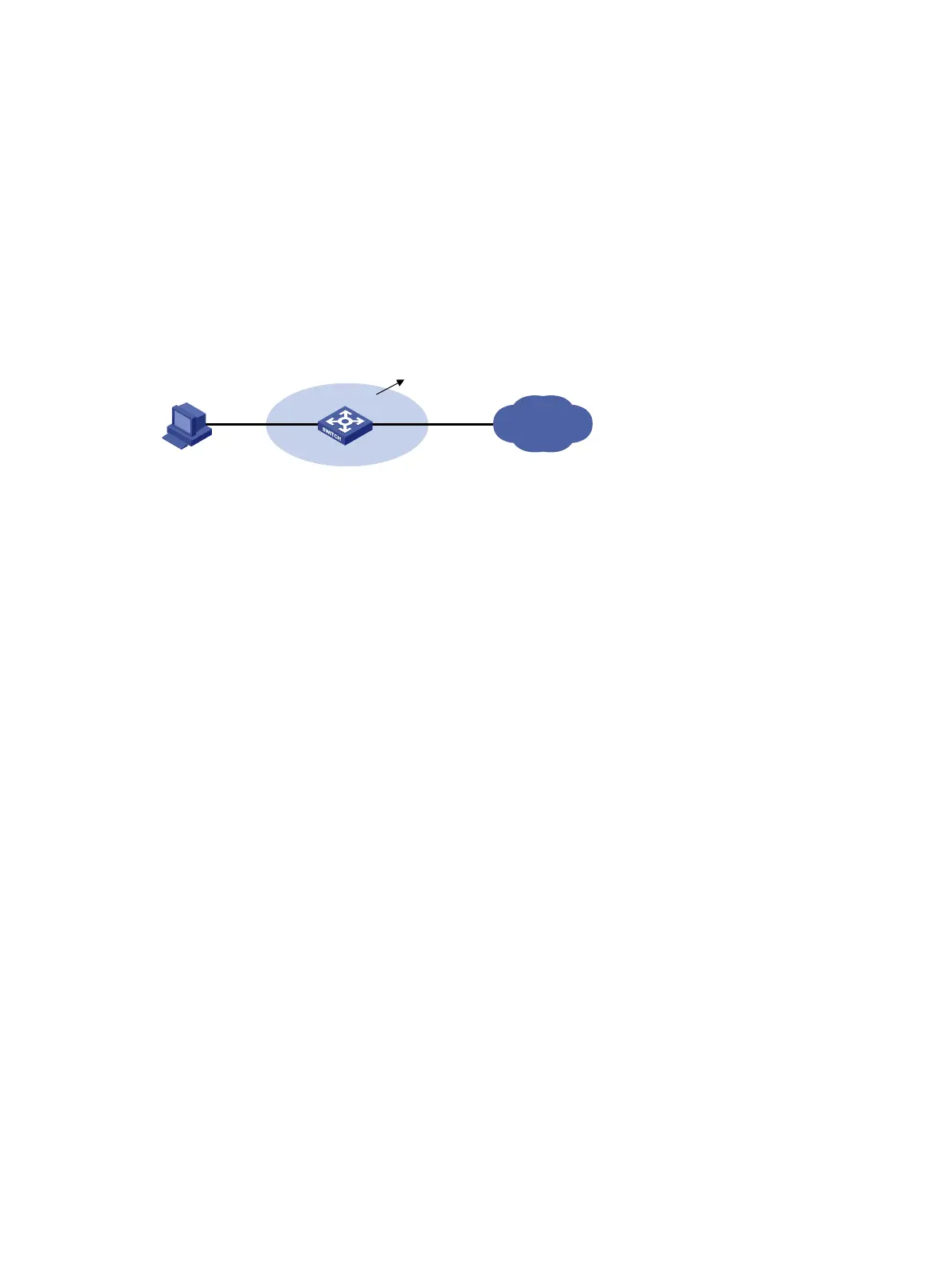
Network requirements
The client is connected to the device through port GigabitEthernet 1/0/1.
Enable ND snooping on the device, establishing ND snooping entries by listening to DAD NS messages.
Enable dynamic IPv6 source guard on port GigabitEthernet 1/0/1 to filter packets based on ND
snooping entries, allowing only packets with a legally obtained IPv6 address to pass.
Figure 105 Network diagram
Configuration procedure
1. Configure ND snooping
# In VLAN 2, enable ND snooping.
<Device> system-view
[Device] vlan 2
[Device-vlan2] ipv6 nd snooping enable
[Device-vlan2] quit
2. Configure dynamic IPv6 source guard.
# Configure dynamic IPv6 source guard on GigabitEthernet 1/0/1 to filter packets based on both the
source IP address and source MAC address of the packets.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] ip check source ipv6 ip-address mac-address
[Device-GigabitEthernet1/0/1] quit
Vefification
# Display IPv6 source guard entries on port GigabitEthernet 1/0/1.
[Device] display ip check source ipv6
Total entries found: 1
MAC Address IP Address VLAN Interface Type
040a-0000-0001 2001::1 2 GE1/0/1 ND-SNP
# Display ND snooping entries on GigabitEthernet 1/0/1.
[Device] display ipv6 nd snooping
IPv6 Address MAC Address VID Interface Aging Status
2001::1 040a-0000-0001 2 GE1/0/1 25 Bound
---- Total entries: 1 ----
The output shows that a dynamic IPv6 source guard entry has generated on port GigabitEthernet 1/0/1
based on the ND snooping entry.
Client
GE1/0/1 GE1/0/2
ND snooping
VLAN 2
IP network
Device

 Loading...
Loading...