8
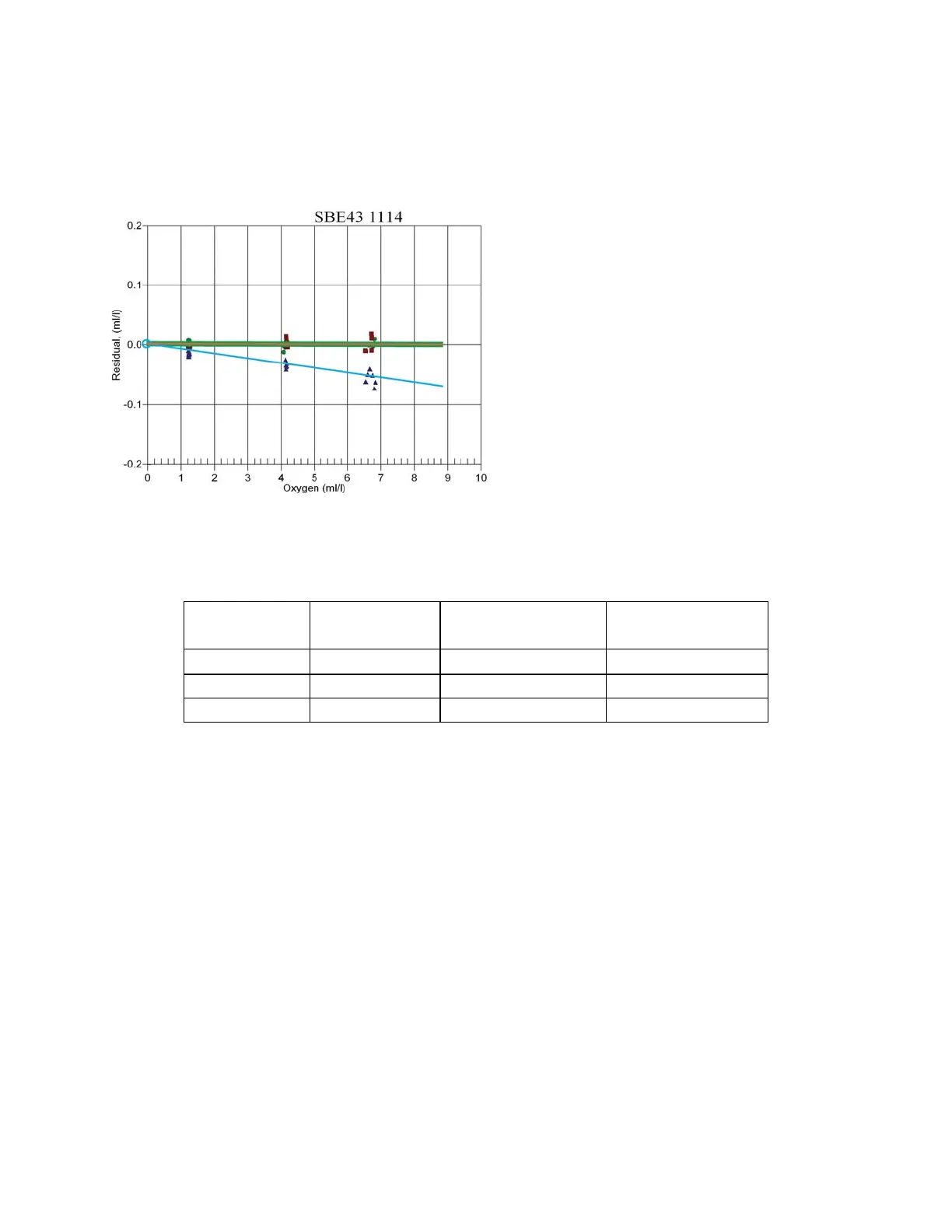
The loss of sensitivity attributed to fouling of the sensor membrane is observed as a linear change in the sensor
output when compared to a set of reference samples (Figure 7 and Table 2). The ratio of the reference sample values
to the SBE 43 measured DO concentrations remains constant over the range of the sensor (for multiple values of
DO). This allows for the adjustment in the slope term SOC using just one quality reference sample, because any of
the reference values would provide the same correction in an otherwise healthy sensor.
Figure 7. Original factory calibration of SBE 43
sensor SN 1114 (green dots); post-recovery
calibration prior to sensor cleaning (blue triangles);
re-calibration after sensor cleaning (red squares).
Notice the loss of sensitivity in the post-recovery
calibration (blue triangles) is strictly linear.
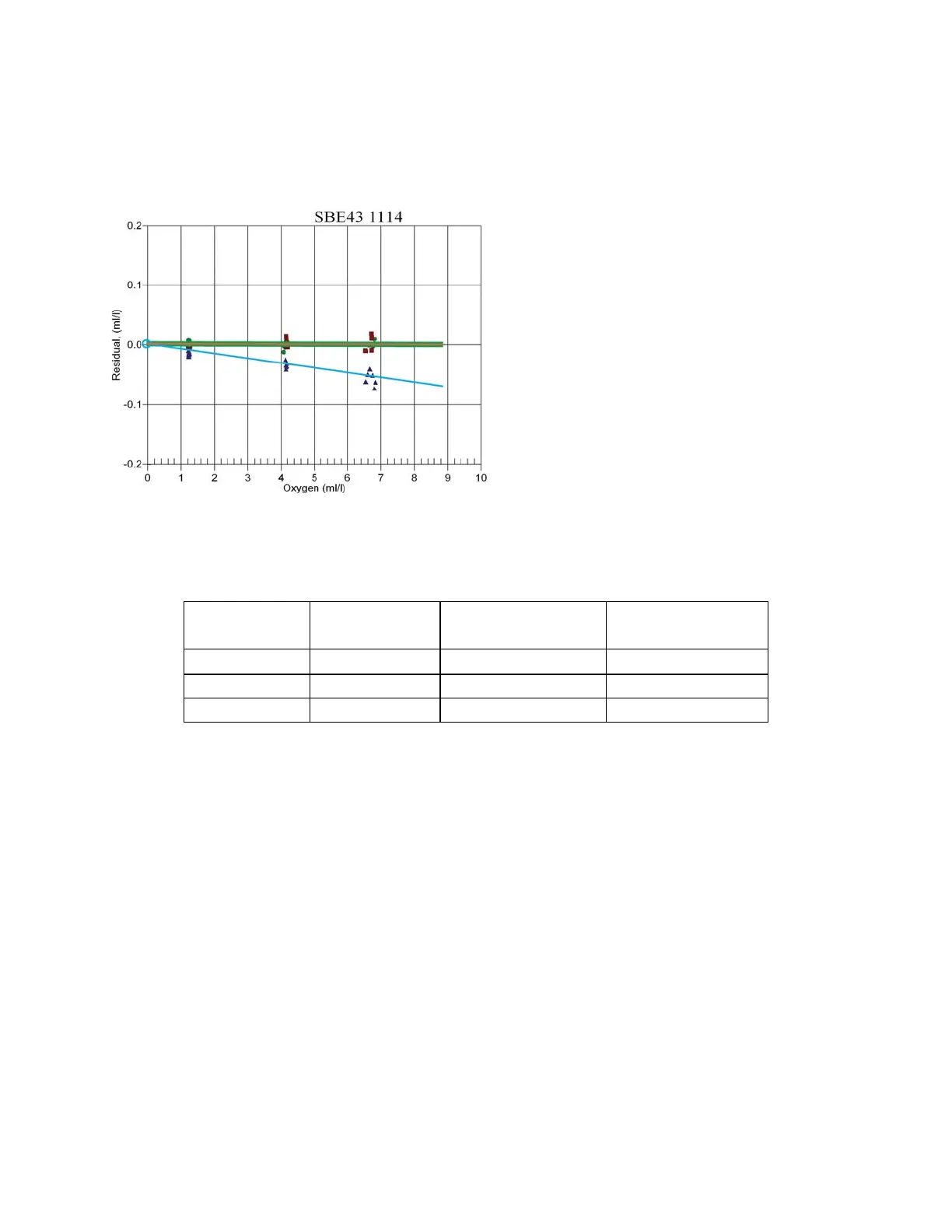
Table 2. Reference Winkler water samples and sensor readings at 3 dissolved oxygen concentrations during post-
recovery calibration of SBE 43 sensor SN 1114 (Figure 7). The ratio between the Winkler values and corresponding
SBE 43 output can be used to calculate the SOC correction factor. Note the SOC correction factor remains constant
at each validation point over the range of oxygen values shown, illustrating that any single validation point alone
could be used to correct the slope.
Winkler DO
of Bath, ml/l
SBE 43 Output,
ml/l
Residual
(SBE 43 – Winkler)
Correction factor
(Winkler/SBE 43)
6.80 6.75 -0.05 6.80/6.75=1.007
4.20 4.17 -0.03 4.20/4.17=1.007
1.20 1.19 -0.01 1.20/1.19=1.007
Simply multiplying the pre-deployment SOC value by the correction factor, given by the ratio
(Winkler DO Value / SBE 43 DO Value)
provides a correction to the linear slope term (SOC) in the calibration equation and offers a powerful and
scientifically defensible way to make residual corrections to data from unattended long-term deployments.
243
 Loading...
Loading...