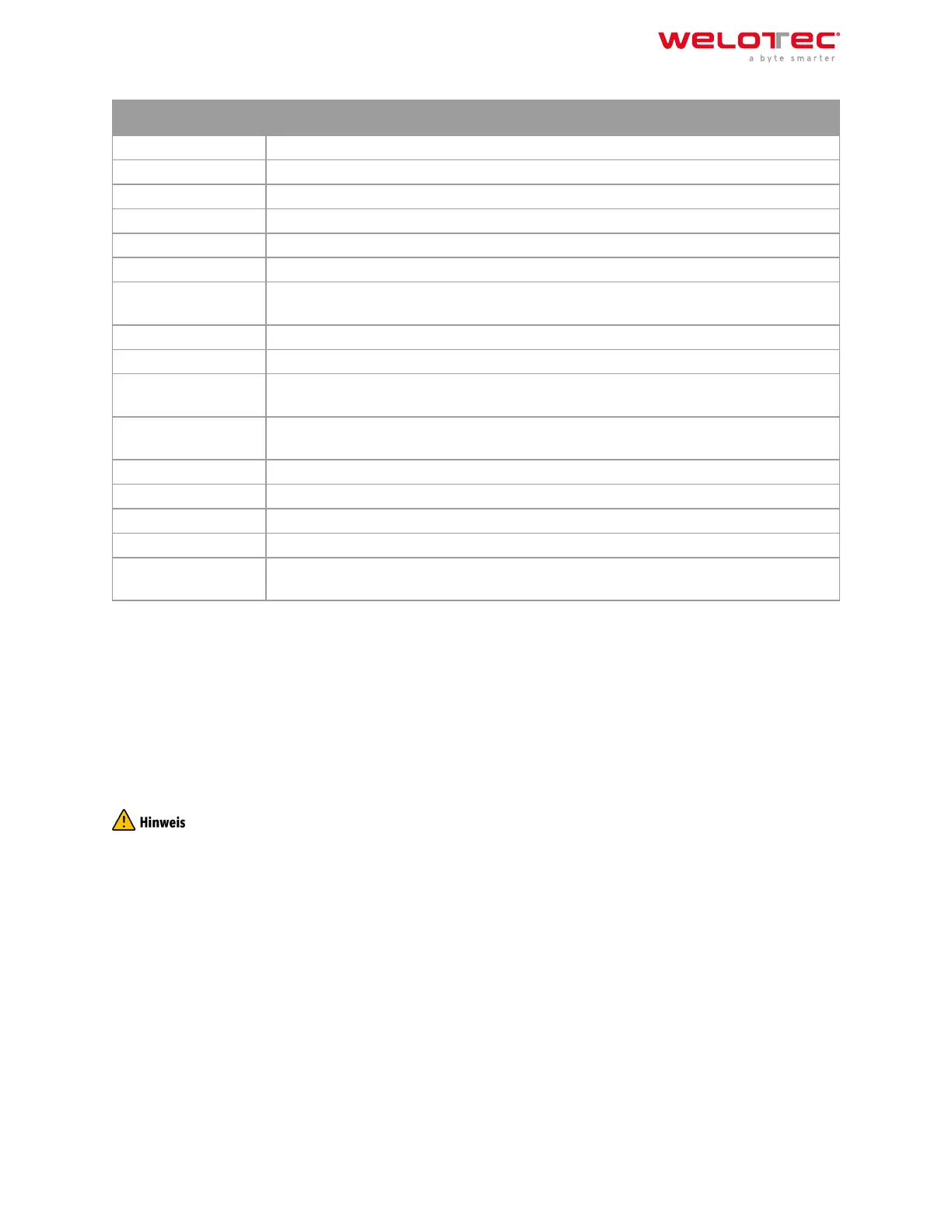
Parameter
Description
Source Interface The interface over which the OpenVPN tunnel is to be established
Interface Type tun or tap (recommended tun)
Network Type Connection type (recommended net30)
Protocol Type UDP or TCP
Port Port on which the OpenVPN server will run
Cipher Encryption method
HMAC Message Authentication Code(MAC) whose construction is based on a cryptographic
hash function
Client‑to‑Client Enable or disable client‑to‑client connection
Compression LZO Enable or disable compression of data
Link Detection Inter‑
val
Interval at which the tunnel connection is checked
Link Detection Time‑
out
Timeout for a tunnel connection check packet
MTU Maximum packet size
TCPMSS Sets the maximum size for TCP packets
Fragment Maximum packet size for UDP packets
Enable Debug Switches the debug mode on or o
Expert Configuration OpenVPN tunnel options that are not available via the web interface can be directly en‑
tered here.
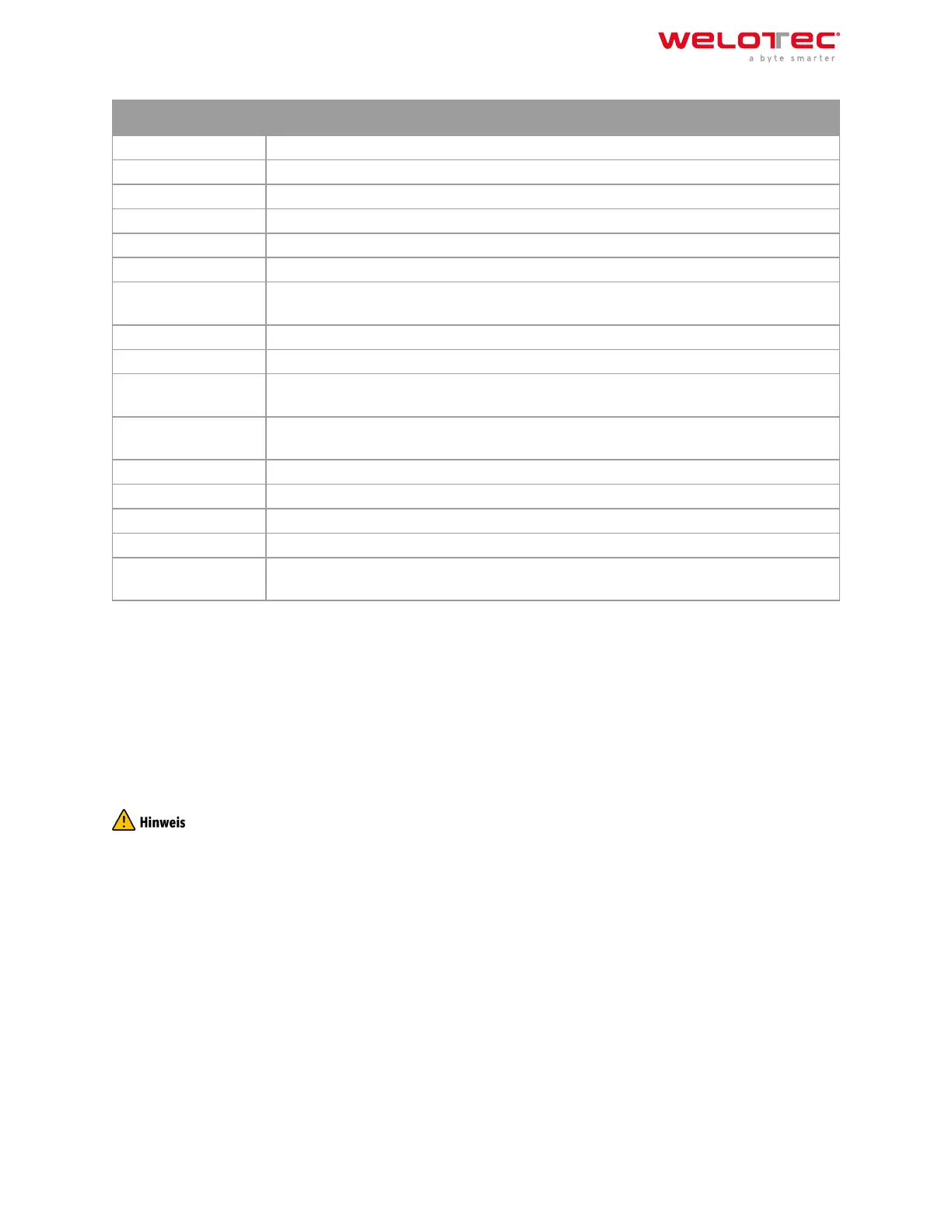
User Password:
Clients can be added here, which can then log in with the user name and password.
Local Subnet:
Here the local subnets of the router are entered, which will be accessible for the clients.
Client Subnet:
The client subnets that are to be accessible from the server side are entered here. The Client ID is the username of
the client for the authentication method Username/Password and the Common Name for certificates.
The OpenVPN server always requires a CA certificate, as well as a public key and a private key. These are uploaded
via VPN > Certificate Management. If these certificates are not available, the server will not start!
3.7.5 3.7.5. Certificate Management
The certificates for an IPSec tunnel or an OpenVPN tunnel are stored in Certificate Management, provided that they
are not secured via a Pre Shared Key (PSK).
Welotec GmbH
Zum Hagenbach 7
48366 Laer
www.welotec.com
info@welotec.com
+49 2554 9130 00
Page 120
 Loading...
Loading...