8-2
Configuring Secure Shell (SSH)
Overview
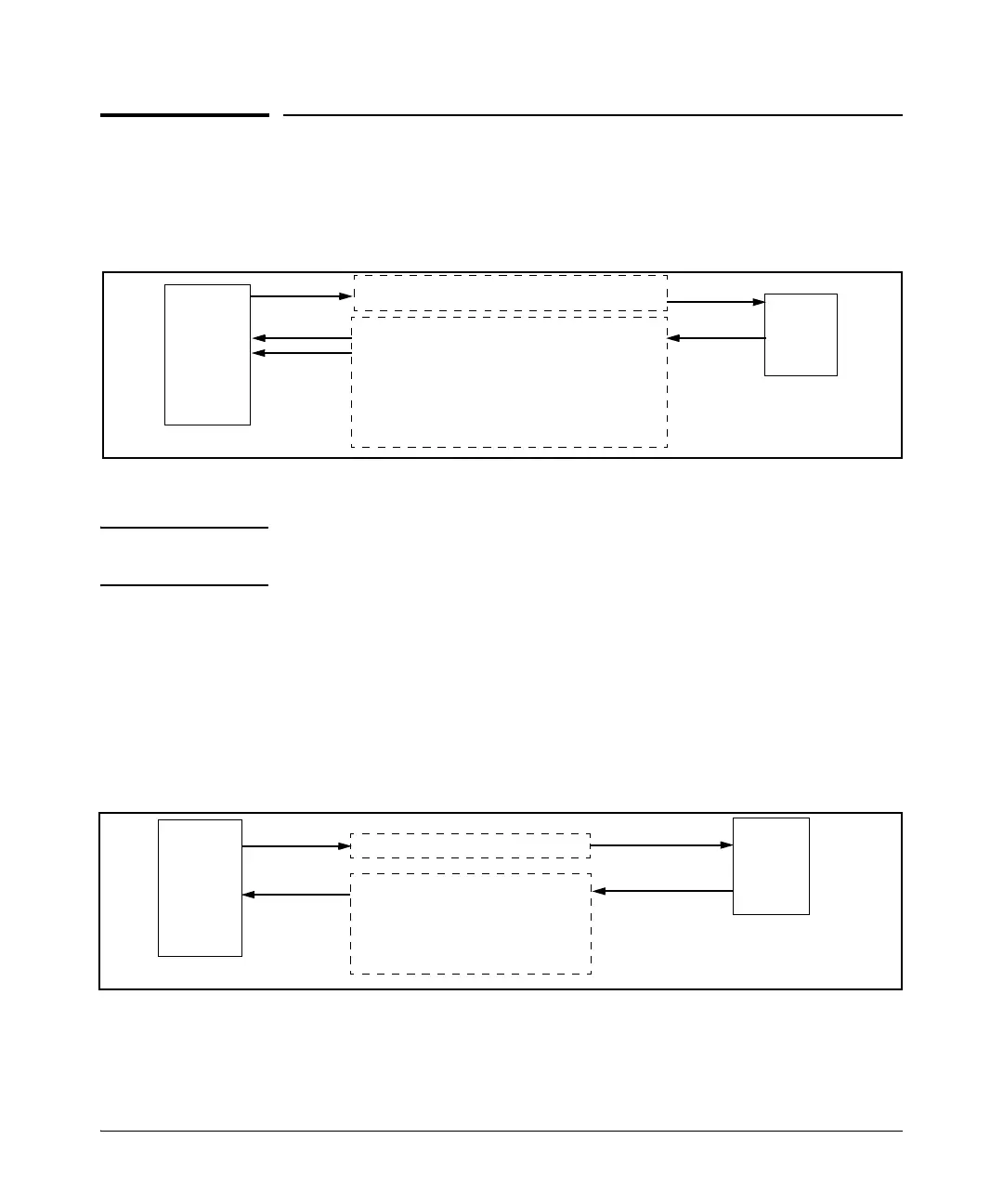
Client Public Key Authentication (Login/Operator Level) with User
Password Authentication (Enable/Manager Level). This option uses
one or more public keys (from clients) that must be stored on the switch. Only
a client with a private key that matches a stored public key can gain access
to the switch. (The same private key can be stored on one or more clients.)
Figure 8-1. Client Public Key Authentication Model
Note SSH in HP switches is based on the OpenSSH software toolkit. For more
information on OpenSSH, visit
www.openssh.com.
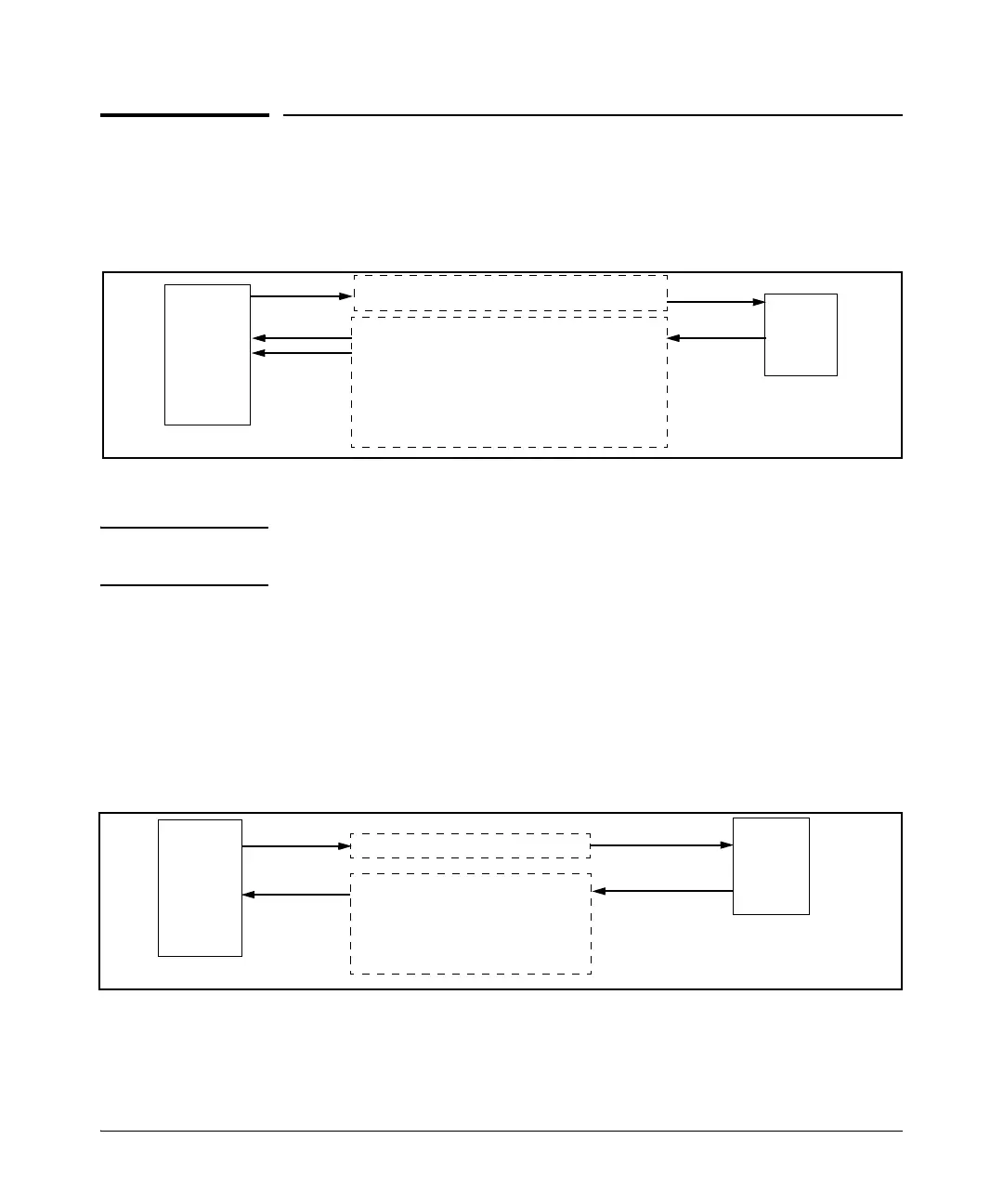
Switch SSH and User Password Authentication . This option is a subset
of the client public-key authentication shown in figure 8-1. It occurs if the
switch has SSH enabled but does not have login access (login public-key)
configured to authenticate the client’s key. As in figure 8-1, the switch authen-
ticates itself to SSH clients. Users on SSH clients then authenticate themselves
to the switch (login and/or enable levels) by providing passwords stored
locally on the switch or on a TACACS+ or RADIUS server. However, the client
does not use a key to authenticate itself to the switch.
Figure 8-2. Switch/User Authentication
HP
Switch
(SSH
Server)
1. Switch-to-Client SSH authentication.
2.Client-to-Switch (login rsa) authentication
3.User-to-Switch (enable password) authentication
options:
– Local
–TACACS+
–RADIUS
–None
SSH
Client
Work-
Station
HP
Switch
(SSH
Server)
SSH
Client
Work-
Station
1. Switch-to-Client SSH
2. User-to-Switch (login password and
enable password authentication)
options:
– Local
– TACACS+
 Loading...
Loading...