Robustel GoRugged R3000 Quad User Guide
RT_UG_R3000 Quad_v.1.2.0 02.07.2015 72 / 136
Confidential
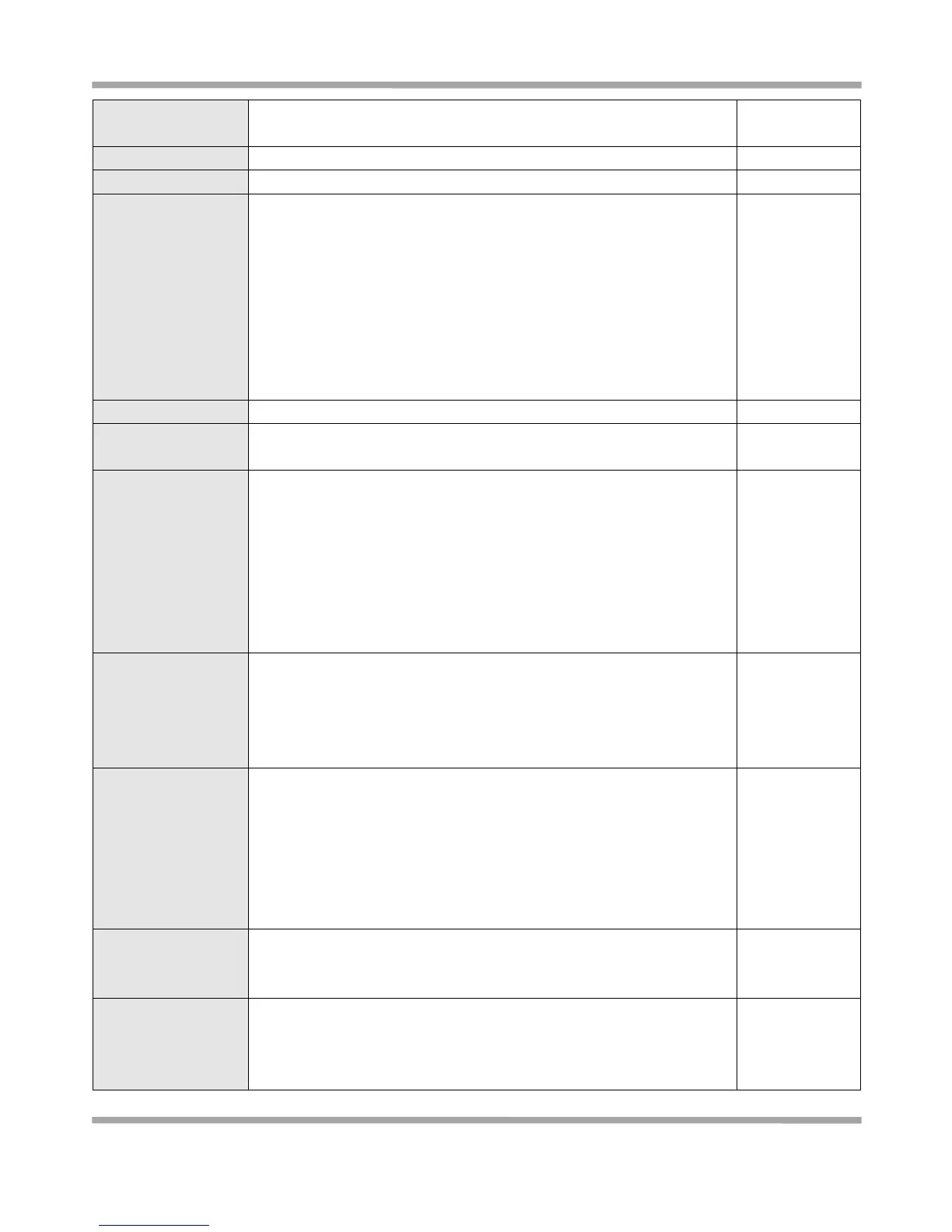
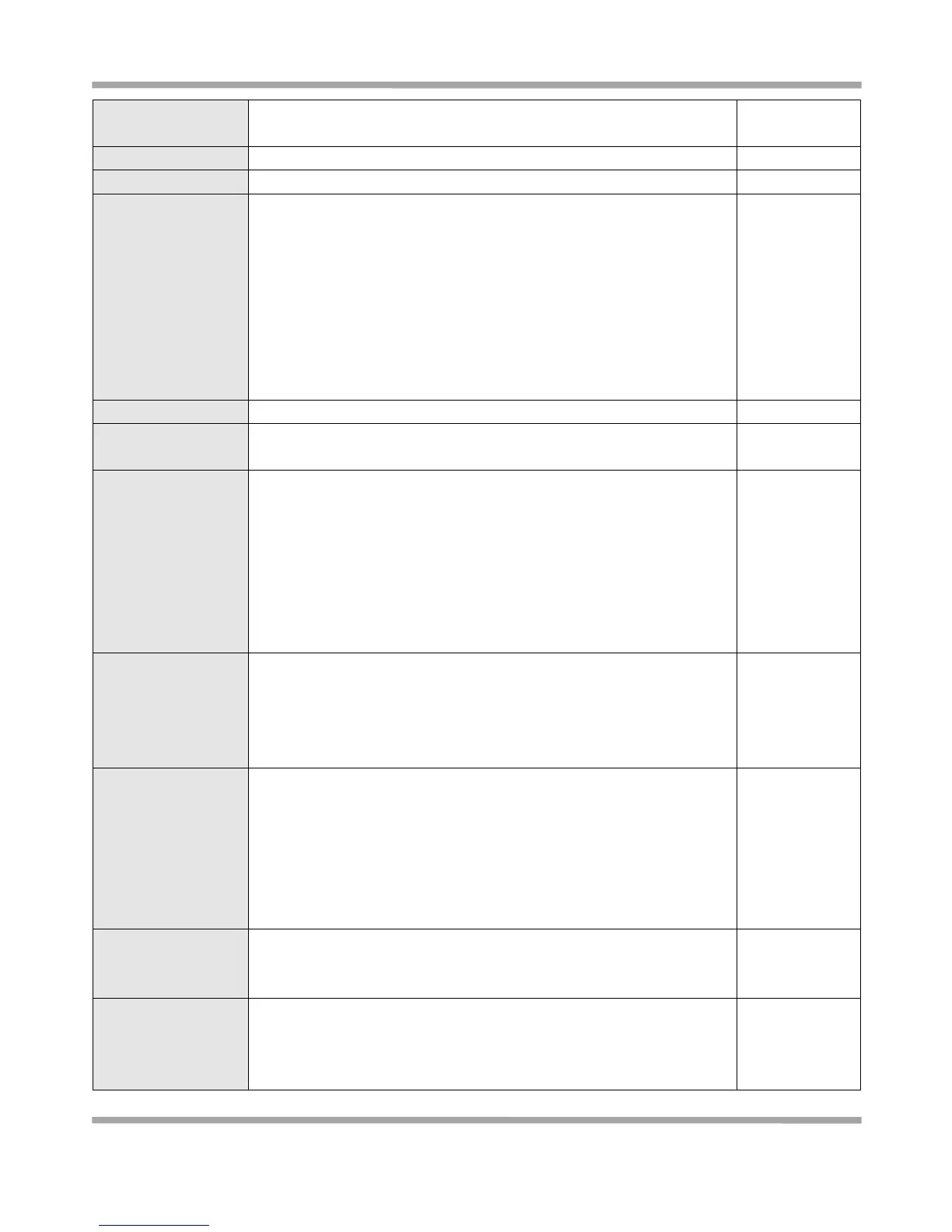
ESP: Uses the ESP protocol.
AH: Uses the AH protocol.
Enter IPSec Local Protected subnet’s address.
Enter IPSec Local Protected subnet’s mask.
Select from “IP Address”, “FQDN” and “User FQDN” for IKE negotiation.
“Default” stands for “IP Address”.
IP Address: Uses an IP address as the ID in IKE negotiation.
FQDN: Uses an FQDN type as the ID in IKE negotiation. If this option is
selected, type a name without any at sign (@) for the local security
gateway, e.g., test.robustel.com.
User FQDN: Uses a user FQDN type as the ID in IKE negotiation. If this
option is selected, type a name string with an sign “@” for the local
security gateway, e.g., test@robustel.com.
Enter IPSec Remote Protected subnet’s address.
Enter IPSec Remote Protected subnet’s mask.
Select from “IP Address”, “FQDN” and “User FQDN” for IKE negotiation.
IP Address: Uses an IP address as the ID in IKE negotiation.
FQDN: Uses an FQDN type as the ID in IKE negotiation. If this option is
selected, type a name without any at sign (@) for the local security
gateway, e.g., test.robustel.com.
User FQDN: Uses a user FQDN type as the ID in IKE negotiation. If this
option is selected, type a name string with a sign “@” for the local
security gateway, e.g., test@robustel.com.
Select from “Main” and “aggressive” for the IKE negotiation mode in
phase 1. If the IP address of one end of an IPSec tunnel is obtained
dynamically, the IKE negotiation mode must be aggressive. In this case,
SAs can be established as long as the username and password are
correct.
Select from “DES”, “3DES”, “AES128”, “AES192” and “AES256”to be
used in IKE negotiation.
DES: Uses the DES algorithm in CBC mode and 56-bit key.
3DES: Uses the 3DES algorithm in CBC mode and 168-bit key.
AES128: Uses the AES algorithm in CBC mode and 128-bit key.
AES192: Uses the AES algorithm in CBC mode and 192-bit key.
AES256: Uses the AES algorithm in CBC mode and 256-bit key.
Select from “MD5” and “SHA1”to be used in IKE negotiation.
MD5: Uses HMAC-SHA1.
SHA1: Uses HMAC-MD5.
Select from “MODP768_1”, “MODP1024_2” and “MODP1536_5”to be
used in key negotiation phase 1.
MODP768_1: Uses the 768-bit Diffie-Hellman group.
MODP1024_2: Uses the 1024-bit Diffie-Hellman group.
 Loading...
Loading...