5. Under “Negotiation Mode” you can choose between two options when negotiating the IPsec tunnel. In
Main Mode, the initiator (the one who wants to establish the connection) and the responder negotiate an
ISAKMP‑SA with each other. This negotiation happens in several steps. In Aggressive Mode, all but three
of the above steps are combined, and the hash values of the pre‑shared keys are transmitted in clear text.
However, there may be a reason for using this mode if the initiator’s address is not known to the responder
in advance, and both sides want to use pre‑shared keys for authentication. Aggressive Mode should be
used with caution, however, because in practice strong keys are oen not used for reasons of convenience.
6. Select the type of authentication for “Authentication Type”. You have two options here. Either via Shared
Key, the common key for authentication (to be entered in the following field) or via Certificate, i.e. via
existing certificates, which then have to be imported via “VPN > Certificate Management”.
7. Enter the subnet of the routerunder “Local Subnet”. In the first field enter the IP address and in the second
the subnet mask. You can create up to four entries.
8. Under “Remote Subnet” you can then enter the subnet of the remote station. Here, you also have the
option of creating up to four entries.
• IKE Advance (Phase 1)
Aer activation, the following options are available:
1. Via the “Local ID” you have the option to select dierent entries from the list box and then enter the corre‑
sponding data in the following field, e.g. IP Address and then enter the desired IP address in the following
field.
2. In the “Remote ID” field, you then enter the data for the remote station.
3. “IKE Keepalive” you can switch on or o to maintain the IKE phase one.
4. You can use the XAUTH protocol for the VPN remote terminal separately by activating this function for
XAUTH. You can then specify or use a corresponding username (Xauth User Name) and password (Xauth
Password).
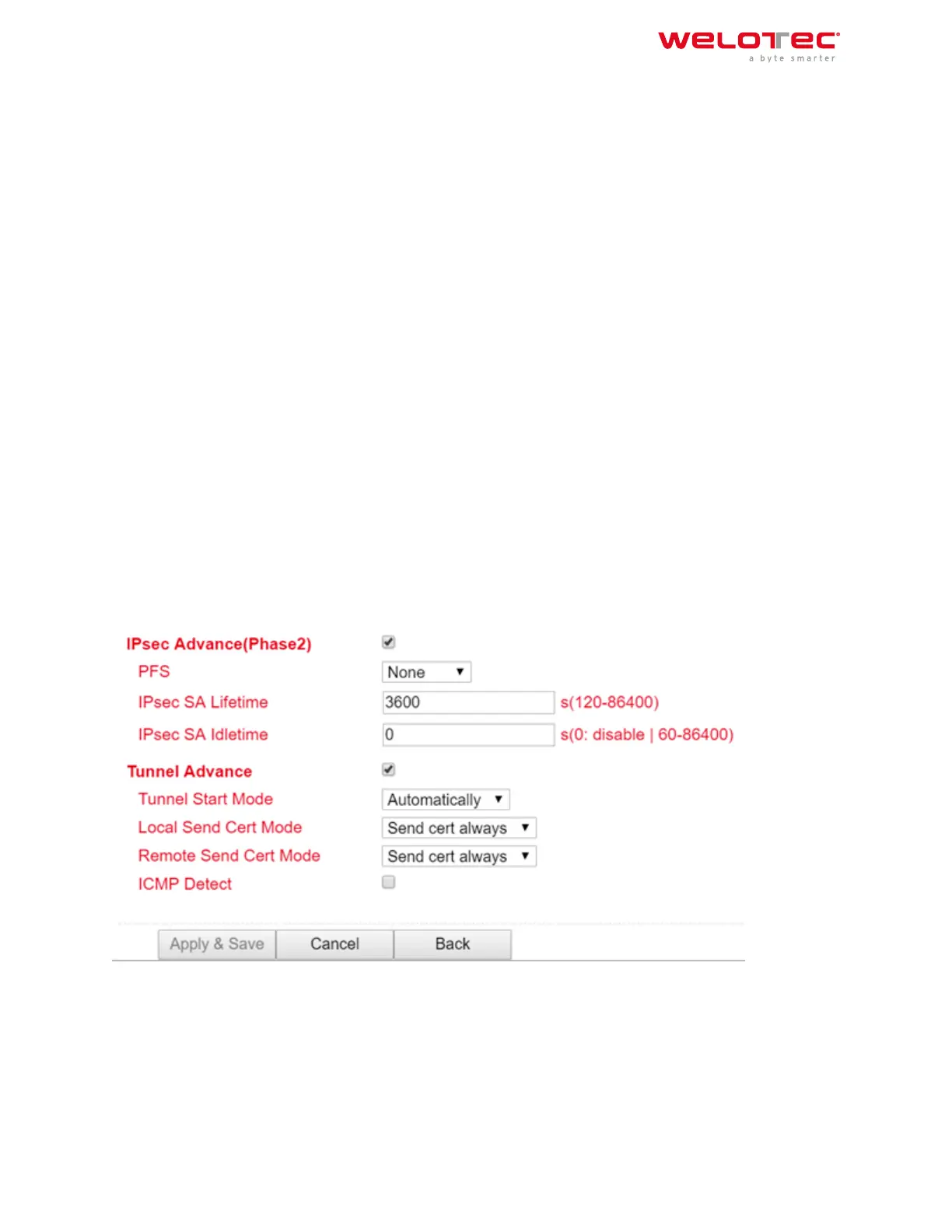
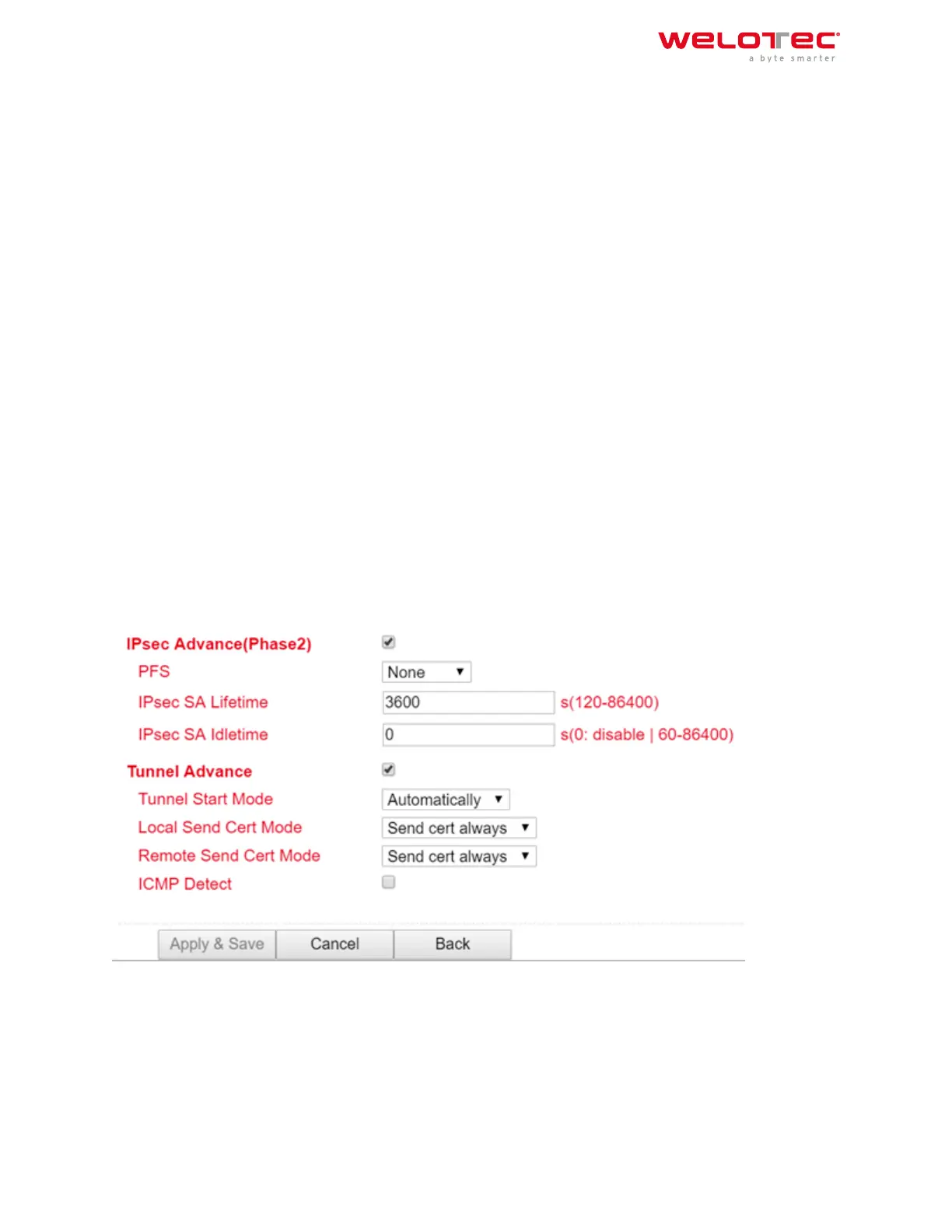
• IPsec Advance (Phase 2)
Aer activation, the following options are available:
1. Perfect Forward Secrecy (PFS) is a characteristic of certain key exchange protocols in cryptography. These
use previously exchanged long‑term keys to arrange a new secret session key for each session that needs
to be encrypted. Perfect Forward Secrecy does not have a log so that the session keys used cannot be
reconstructed from the long‑term secret keys aer the session is closed. This means that a recorded en‑
crypted communication cannot be subsequently decrypted even if the long‑term key is known. Here you
Welotec GmbH
Zum Hagenbach 7
48366 Laer
www.welotec.com
info@welotec.com
+49 2554 9130 00
Page 159
 Loading...
Loading...