CL64WLAN User Manual V001
29 of 44
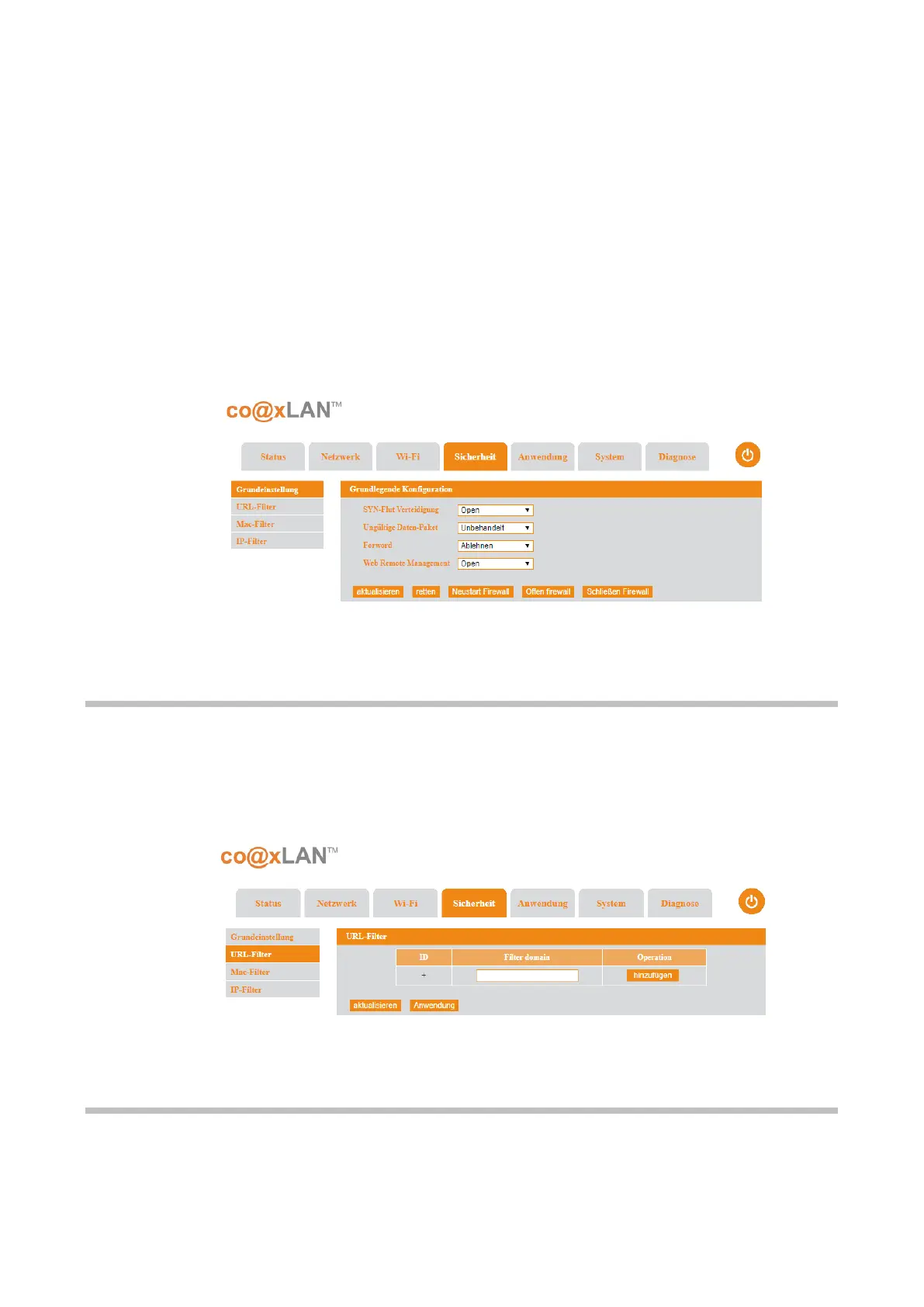
(acknowledged) packet to confirm that the server's SYN/ACK packet was received, and
communications would then commence. However, in a SYN flood, the ACK packet is never
sent back by the hostile client. Instead, the client program sends repeated SYN requests to
all the server's ports. A hostile client always knows a port is open when the server responds
with a SYN/ACK packet.
The hostile client makes the SYN requests all appear valid, but because the IP addresses are
fake ones, it is impossible for the server to close down the connection by sending RST
packets back to the client. Instead, the connection stays open. Before time-out can occur,
another SYN packet arrives from the hostile client. A connection of this type is called a half-
open connection. Under these conditions, the server becomes completely or almost
completely busy with the hostile client and communications with legitimate clients is difficult
or impossible. For this reason, SYN floods are also known as half-open attacks.
The transmission by a hostile client of SYN packets for the purpose of finding open ports and
hacking into one or more of them, is called SYN scanning.
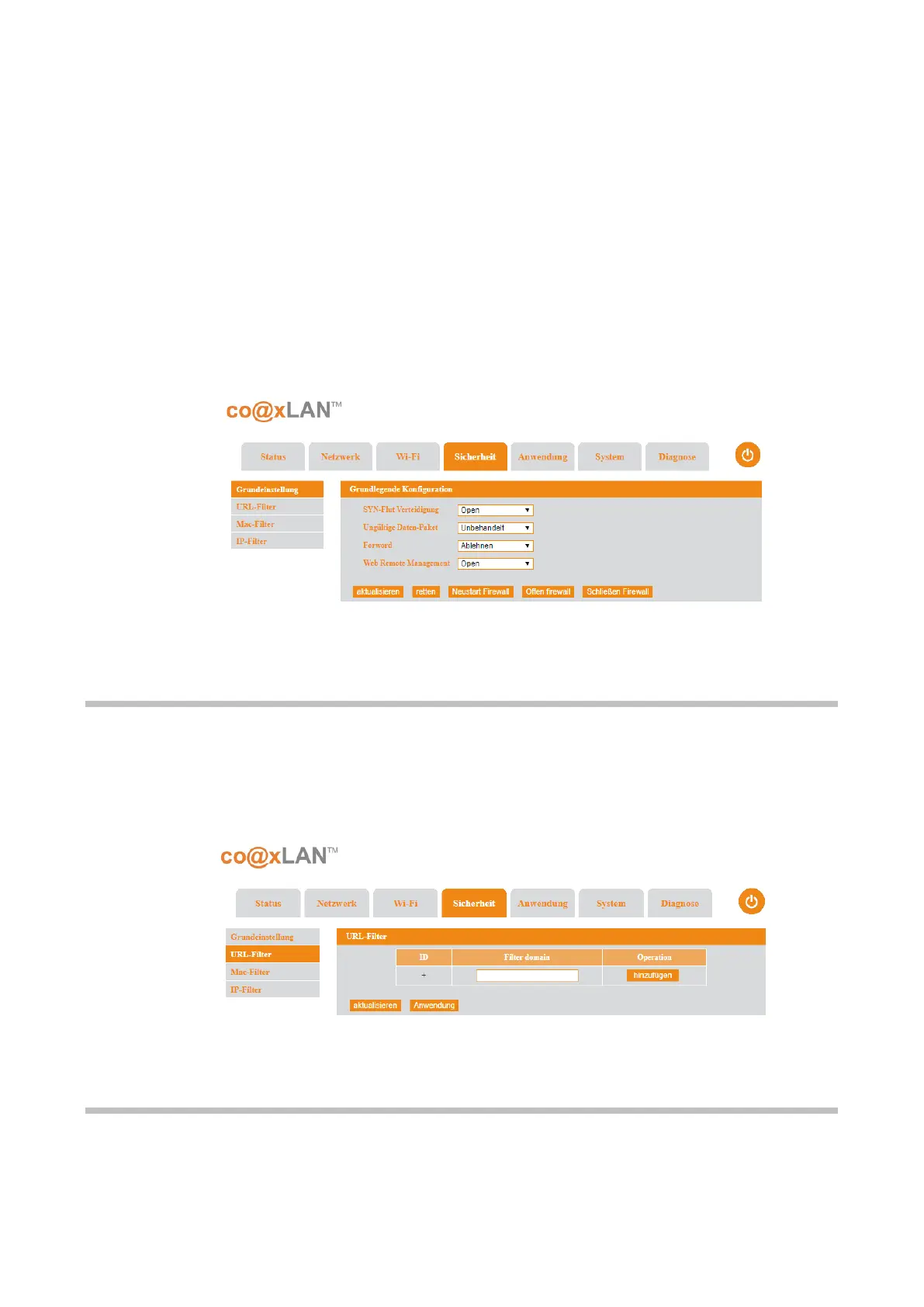
8.2. URL Filter
If the URL Filter sub-menu is selected the screen shown in Picture is displayed. If you enter
the domain name to filter in the Filter domain box, click the Add button to add this new
filtering rule to the firewall.
8.3. MAC Filter
If the MAC Filter sub-menu is selected the screen shown in Picture is displayed. The following
table explains the items shown in this page:
Picture 17
Picture 18
 Loading...
Loading...