Chapter 13 - Configuring The Firewall
Rate-Limit A specification which allows the rate at which connections are
made to be limited.
User-Group A method of limiting outbound traffic from the firewall to a
specific user, group of users and a specific application.
Some examples will illustrate the power of the rules file:
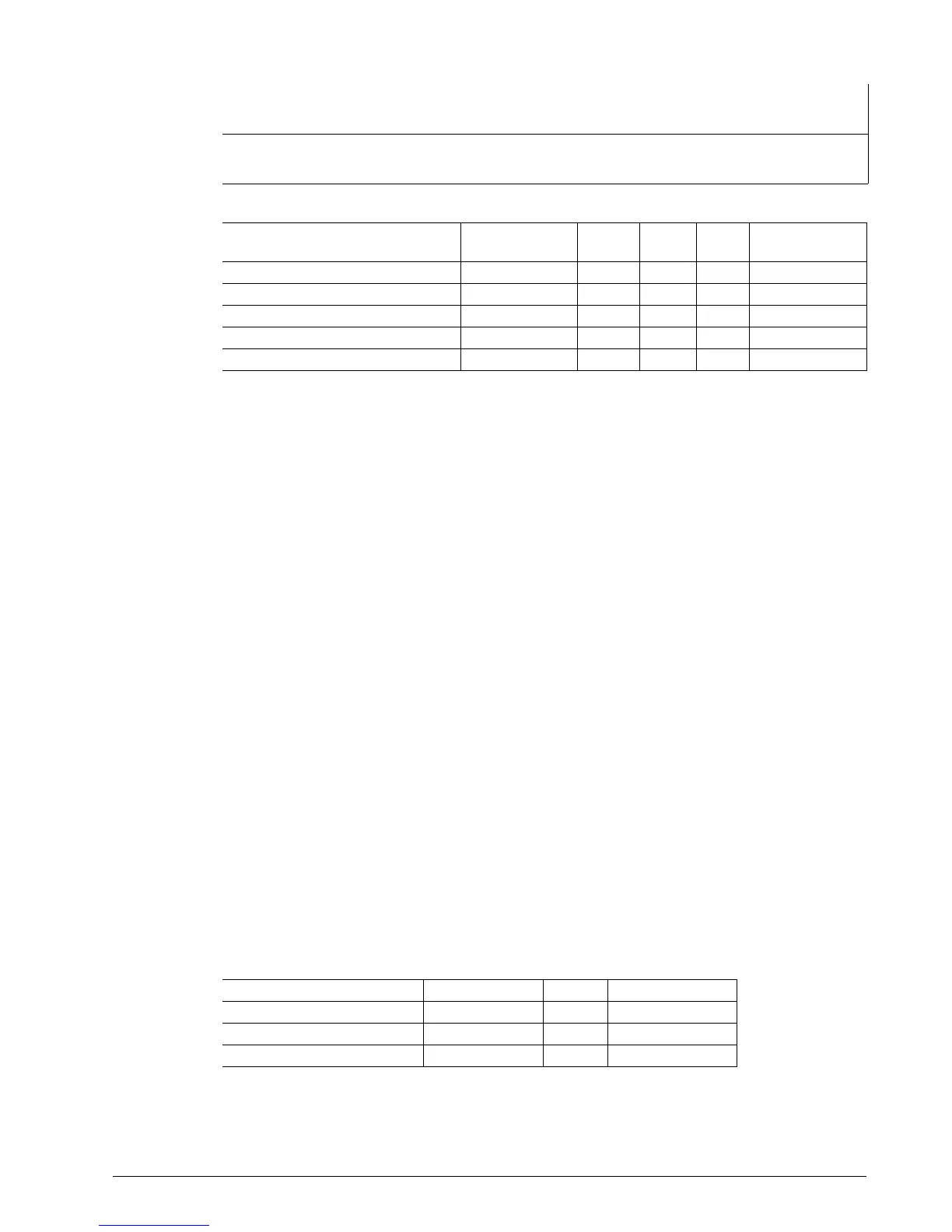
Rule Action Source-Zone Destination-Zone Protocol Dest-
Port
Source
-Port
Original-
Destination-IP
1 ACCEPT net:204.18.45.0/24 fw
2 DNAT net loc:192.168.1.3 tcp ssh, http
3 DNAT net:204.18.45.0/24 loc:192.168.1.3 tcp http - 130.252.100.69
4 ACCEPT fw net icmp
5 ACCEPT net:204.18.45.0/24 fw icmp 8
1) This rule accepts traffic to the firewall itself from the 204.18.45.0/24 subnet. If the
default policy is to drop all requests from net to the firewall, this rule will only
traffic from the authorized subnet.
2) This rule forwards all ssh and http connection requests from the Internet to local
system 192.168.1.3.
3) This rule forwards http traffic from 204.18.45.0/24 (which was originally directed
to the firewall at 130.252.100.69) to the host at 192.168.1.3 in the local zone. If
the firewall supports another public IP address (e.g. 130.252.100.70), a similar rule
could map requests to another host.
4) and 5) These rules allow the firewall to issue icmp requests to the Internet and to
respond to icmp echo requests from the authorized subnet.
Rules are defined in the file /etc/shorewall/rules and are modified from the Firewall
Rules menu.
Configuring The Firewall And VPN
Route Based Virtual Private Networking
Begin configuration by creating local, network and vpn zones (all as zone type IPV4).
The openswan daemon will have created ipsecX interfaces which should be added to
the vpn zone in the interfaces menu.
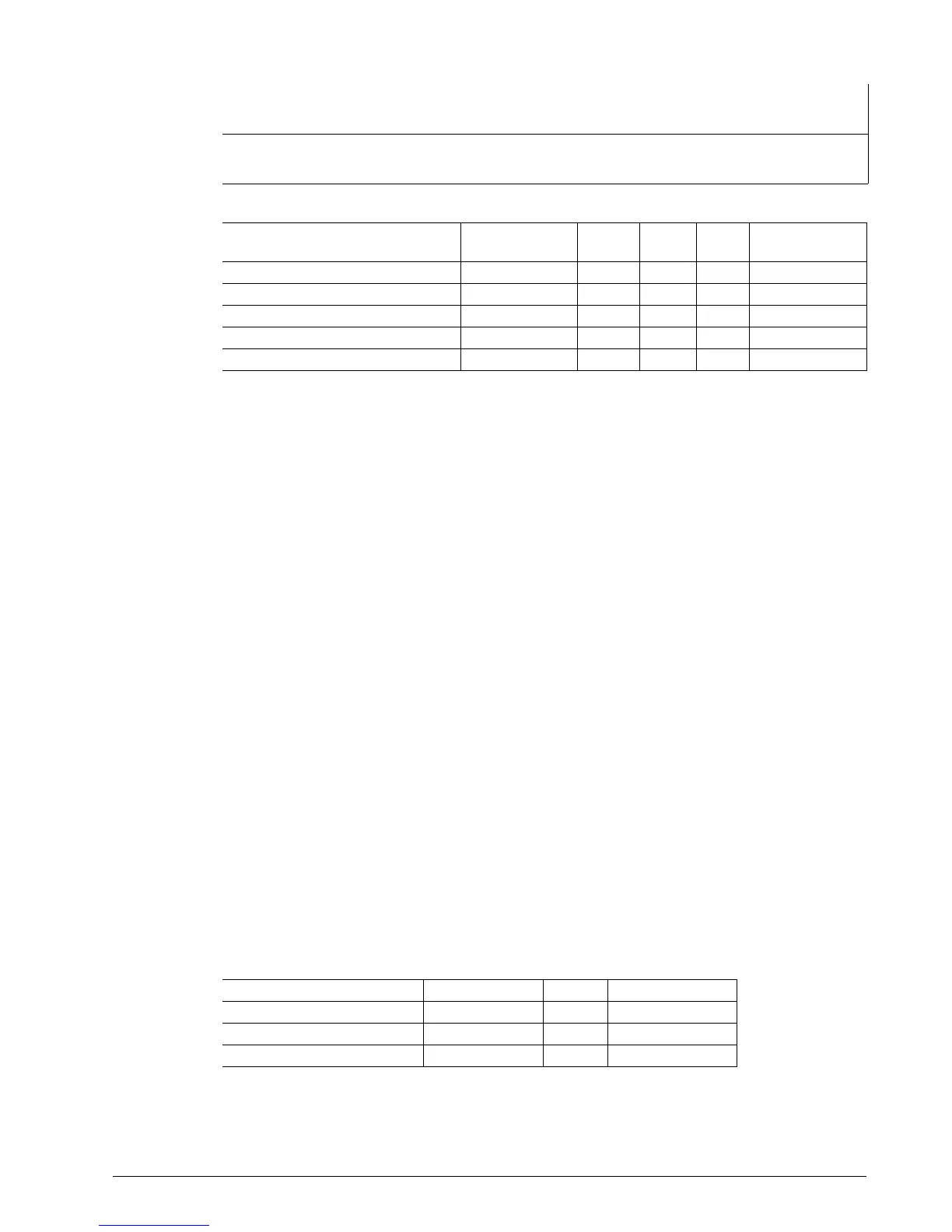
The IPsec protocol operates on UDP port 500 and using protocols ah (Authentication
Header) and Encapsulating Security Payload (ESP) protocols. The firewall must
accept this traffic in order to allow IPsec. If the firewall serves as the VPN gateway,
add the following rules:
Action Source-Zone Destination-Zone Protocol Dest-Port
ACCEPT all fw ah
ACCEPT all fw esp
ACCEPT all fw udp 500
RuggedCom 117

 Loading...
Loading...