1-18
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring the Identity Firewall
Task Flow for Configuring the Identity Firewall
What to Do Next
Configure the Active Directory domain and server groups. See Configuring the Active Directory
Domain, page 1-10.
Configure AD Agents. See Configuring Active Directory Agents, page 1-12.
Configuring Identity-Based Security Policy
You can incorporate identity-based policy in many ASA features. Any feature that uses extended ACLs
(other than those listed as unsupported in the “Guidelines and Limitations” section on page 1-7) can take
advantage of identity firewall. You can now add user identity arguments to extended ACLs, as well as
network-based parameters.
• To configure an extended ACL, see Chapter 1, “Adding an Extended Access Control List.”
• To configure local user groups, which can be used in the ACL, see the “Configuring Local User
Groups” section on page 1-11.
Features that can use identity include the following:
• Access rules—An access rule permits or denies traffic on an interface using network information.
With identity firewall, you can now control access based on user identity. See Chapter 1,
“Configuring Access Rules.”
• AAA rules—An authentication rule (also known as “cut-through proxy”) controls network access
based on user. Because this function is very similar to an access rule + identity firewall, AAA rules
can now be used as a backup method of authentication if a user’s AD login expires. For example,
for any user without a valid login, you can trigger a AAA rule. To ensure that the AAA rule is only
triggered for users that do not have valid logins, you can specify special usernames in the extended
ACL used for the access rule and for the AAA rule: None (users without a valid login) and Any
(users with a valid login). In the access rule, configure your policy as usual for users and groups, but
then include a rule that permits all None users; you must permit these users so they can later trigger
a AAA rule. Then, configure a AAA rule that denies Any users (these users are not subject to the
AAA rule, and were handled already by the access rule), but permits all None users:
access-list 100 ex permit ip user CISCO\xyz any any
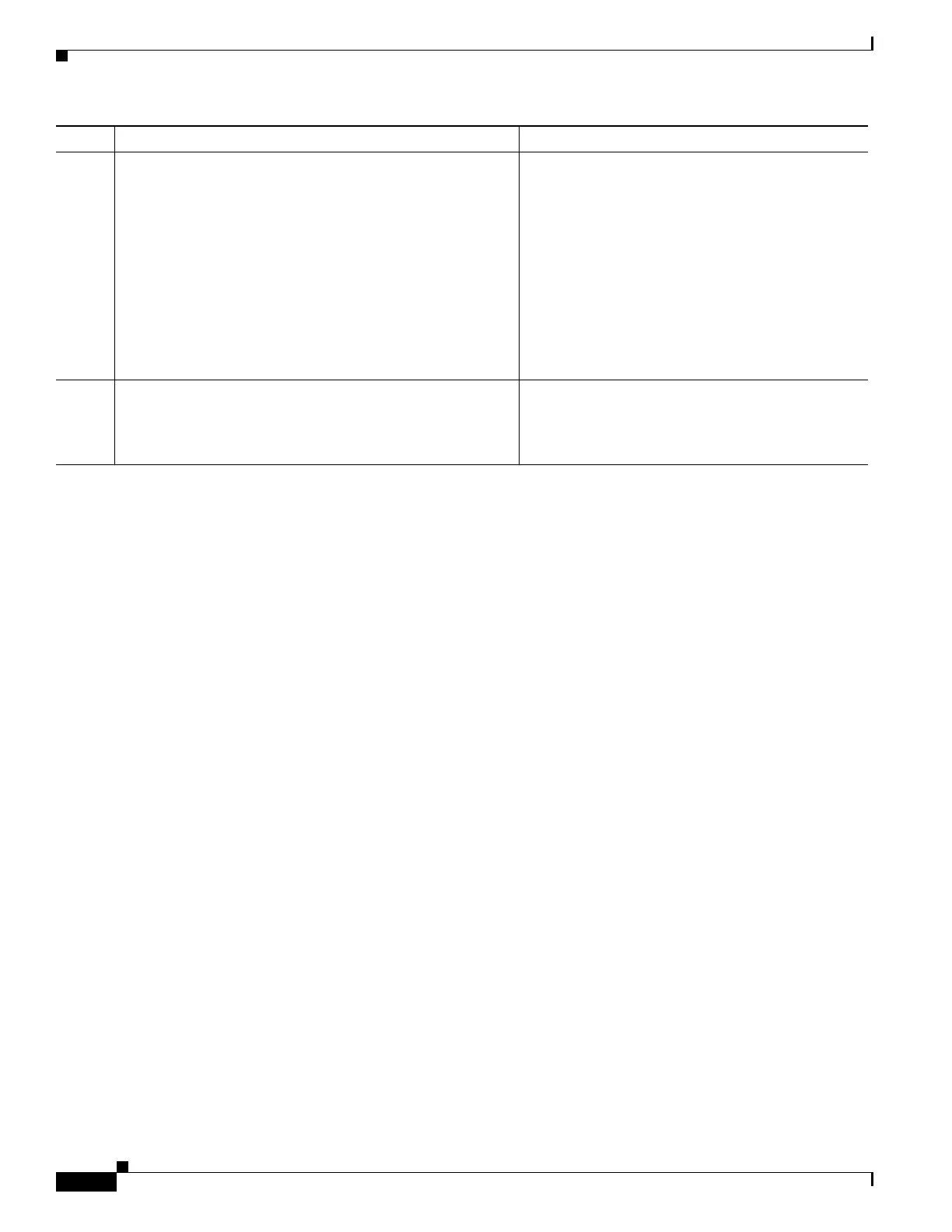
Step 13
hostname(config)# user-identity ad-agent hello-timer
seconds seconds retry-times number
Example:
hostname(config)# user-identity ad-agent hello-timer
seconds 20 retry-times 3
Defines the hello timer between the ASA and the AD
Agent.
The hello timer between the ASA and the AD Agent
defines how frequently the ASA exchanges hello
packets. The ASA uses the hello packet to obtain
ASA replication status (in-sync or out-of-sync) and
domain status (up or down). If the ASA does not
receive a response from the AD Agent, it resends a
hello packet after the specified interval.
By default, the hello timer is set to 30 seconds and 5
retries.
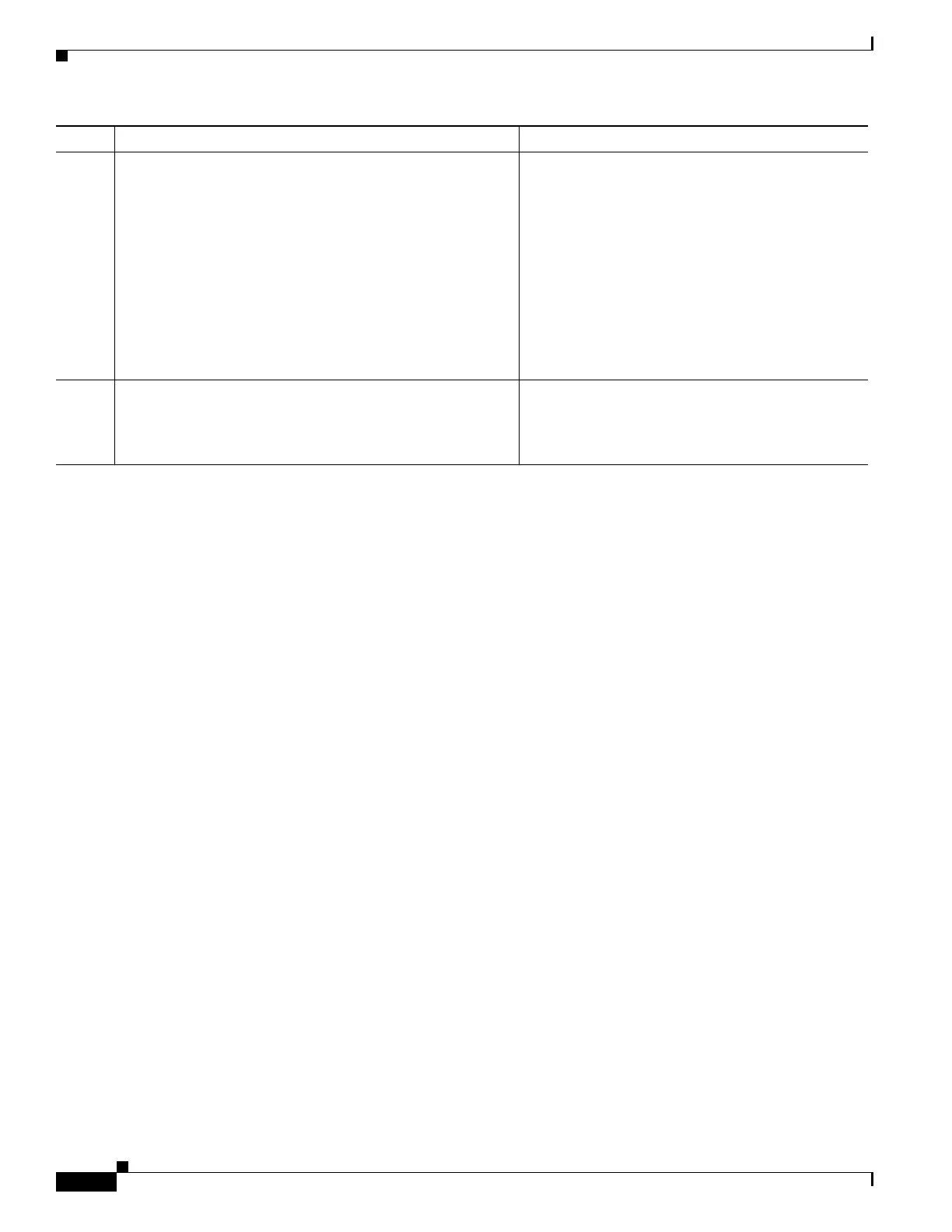
Step 14
hostname(config)# user-identity ad-agent aaa-server
aaa_server_group_tag
Example:
hostname(config)# user-identity ad-agent aaa-server
adagent
Defines the server group of the AD Agent.
For aaa_server_group_tag, enter the value defined
by the aaa-server command.
Command Purpose

 Loading...
Loading...