1-10
Cisco Unified Wireless IP Phone 7925G Administration Guide for Cisco Unified Communications Manager 7.0(1)
OL-15984-01
Chapter 1 Overview of the Cisco Unified Wireless IP Phone 7925G
Understanding Security Features for Cisco Unified IP Phones
Overview of Supported Security Features
Table 1-3 provides an overview of the security features that the Cisco Unified Wireless IP Phone 7925G
supports. For more information about these features and about Cisco Unified Communications Manager
and Cisco
Unified IP Phone security, refer to Cisco Unified Communications Manager Security Guide.
For information about current security settings on a phone, choose SETTINGS > System
Configuration > Security. For more information, see the
“Viewing Security Information” section on
page 8-1.
Note Most security features are available only if a certificate trust list (CTL) is installed on the phone. For
more information about the CTL, refer to “Configuring the Cisco CTL Client” chapter in the Cisco
Unified Communications Manager Security Guide.
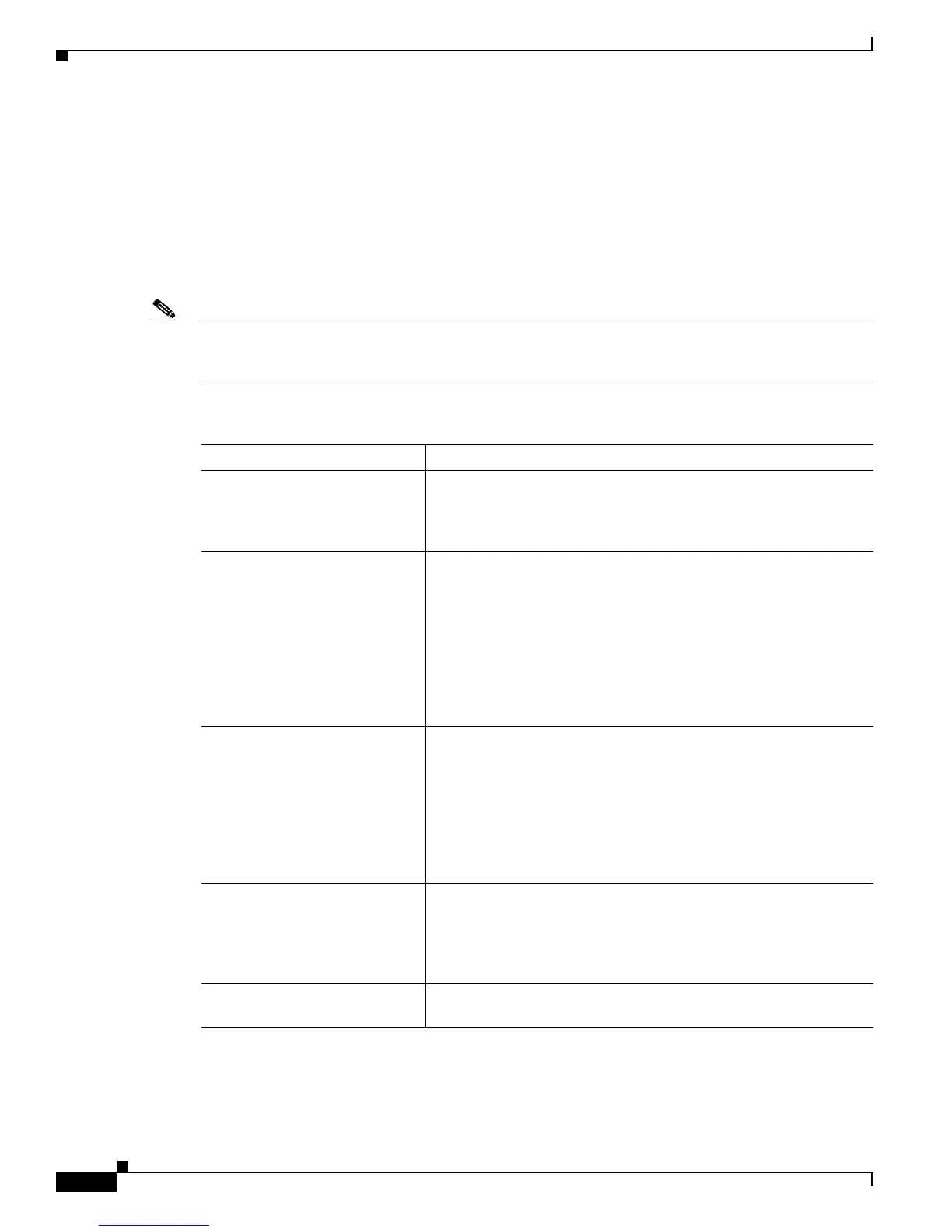
Ta b l e 1-3 Description of Security Features
Feature Description
Image authentication Prevents tampering with the firmware image before it is loaded on
a phone by using signed binary files (with the extension.sbn).
Tampering with the image causes a phone to fail the authentication
process and reject the new image.
Customer-site certificate
installation
Authenticates each Cisco Unified IP Phone by using a unique
certificate. Phones include a manufacturing installed certificate
(MIC), but for additional security, you can specify in Cisco
Unified
Communications Manager Administration that a certificate
be installed by using the Certificate Authority Proxy Function
(CAPF). Alternatively, you can install a locally significant
certificate (LSC) from the Security Configuration menu on the
phone. See the
“Configuring the Security Certificate on the Phone”
section on page 5-12 for more information.
Device authentication Occurs between the Cisco Unified Communications Manager server
and the phone when each entity accepts the certificate of the other
entity. Determines whether a secure connection between the phone
and a Cisco
Unified Communications Manager should occur, and, if
necessary, creates a secure signaling path between the entities using
TLS protocol. Cisco
Unified Communications Manager will not
register phones unless authenticated by the Cisco Unified
Communications Manager.
File authentication Validates digitally-signed files that the phone downloads. The
phone validates the signature to make sure that file tampering did
not occur after the file creation. Files that fail authentication are not
written to Flash memory on the phone. The phone rejects such files
without further processing.
Signaling Authentication Uses the TLS protocol to validate that no tampering has occurred to
signaling packets during transmission.
 Loading...
Loading...