270
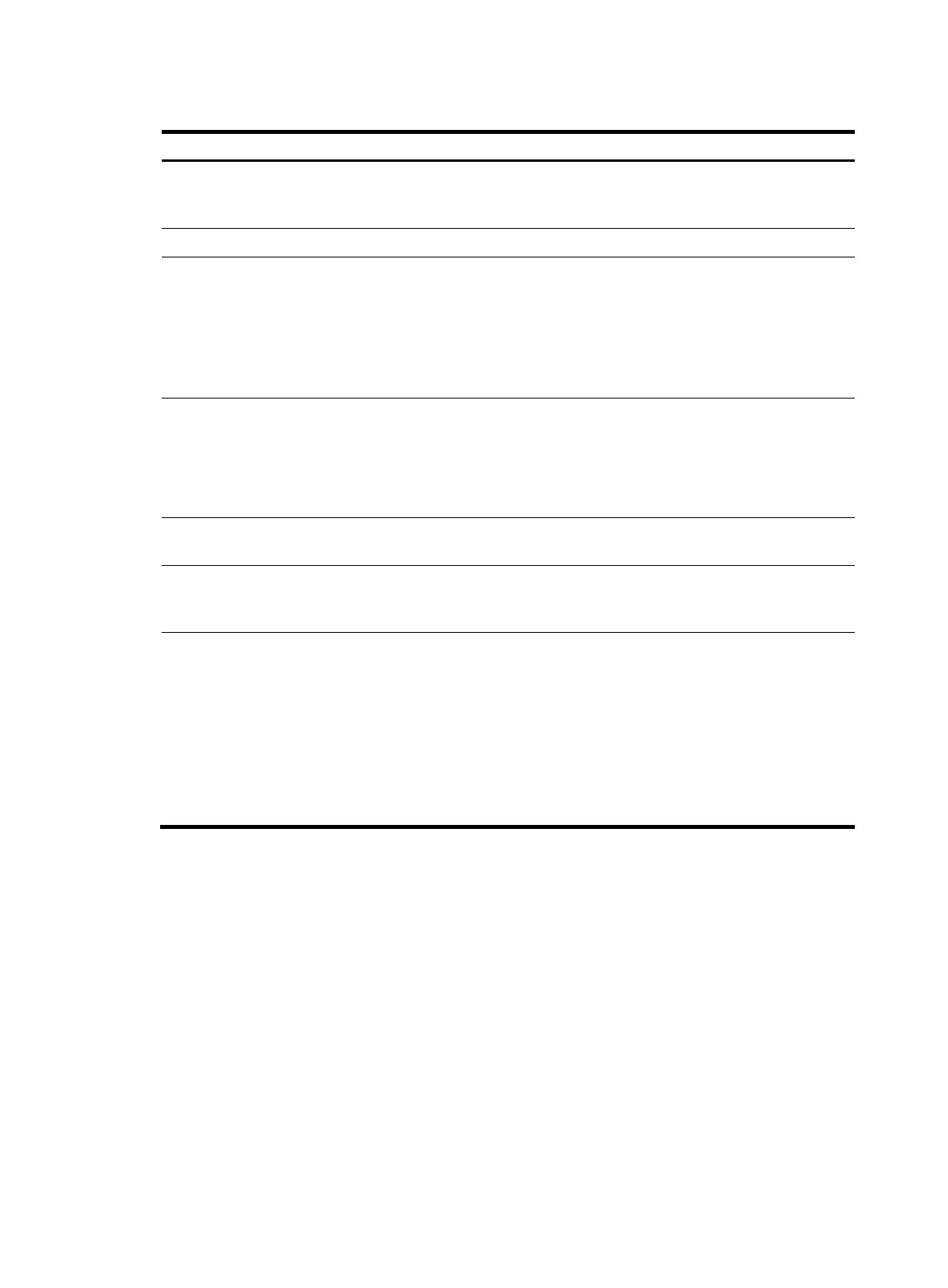
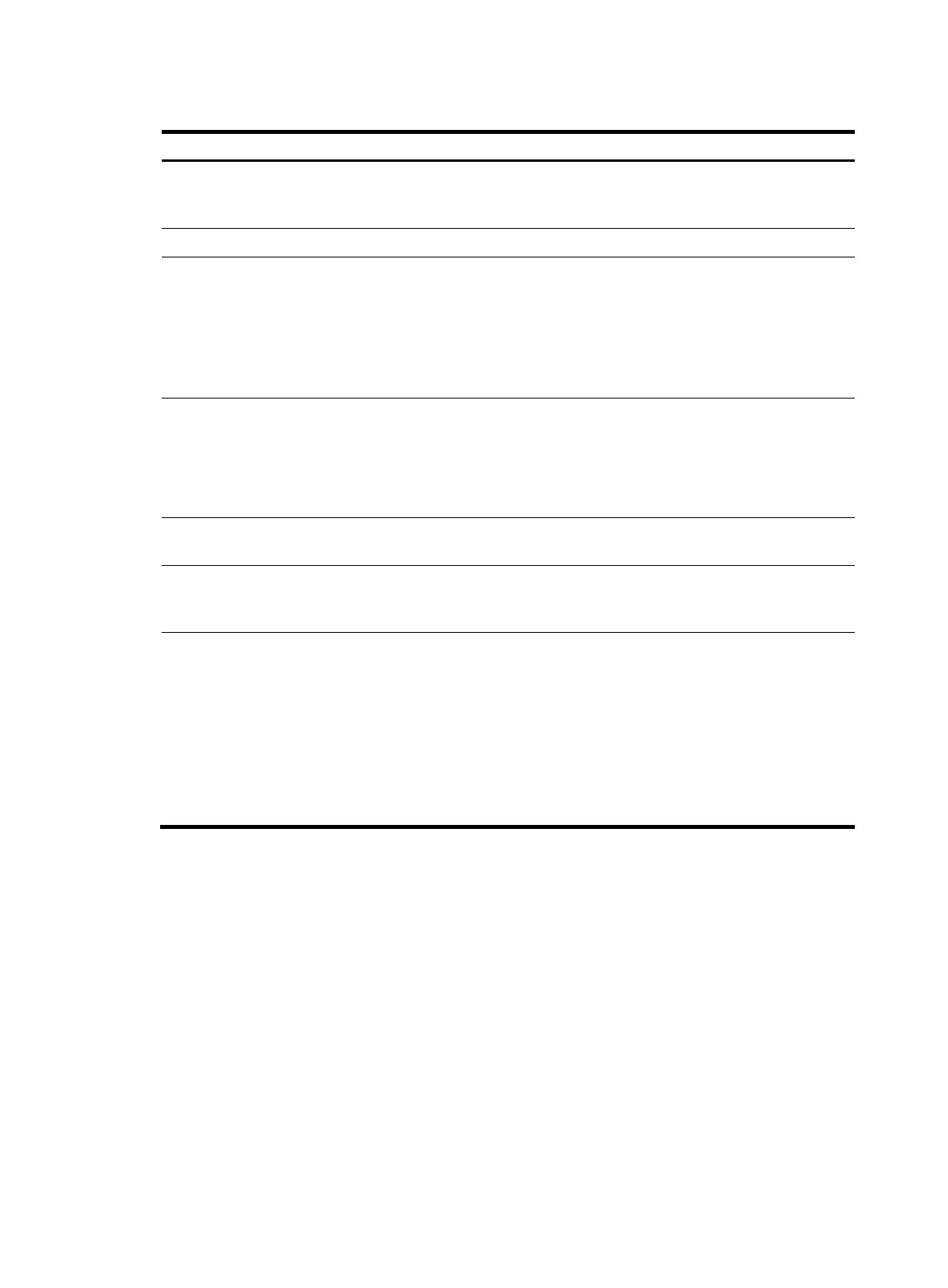
Table 10 Stages involved in secure session establishment
Sta
es Descri
tion
Connection establishment
The SSH server listens to the connection requests on port 22. After a
client initiates a connection request, the server and the client establish a
TCP connection.
Version negotiation The two parties determine a version to use after negotiation.
Algorithm negotiation
SSH supports multiple algorithms. Based on the local algorithms, the two
parties negotiate the following algorithms:
• Key exchange algorithm for generating session keys.
• Encryption algorithm for encrypting data.
• Public key algorithm for digital signature and authentication.
• HMAC algorithm for protecting data integrity.
Key exchange
The two parties use the DH exchange algorithm to dynamically generate
the session keys and session ID.
• The session keys are used for protecting data transfer.
• The session ID is used for identifying the SSH connection.
In this stage, the client authenticates the server as well.
Authentication
The SSH server authenticates the client in response to the client's
authentication request.
Session request
After passing the authentication, the client sends a session request to the
server to request the establishment of a session (or request the Stelnet,
SFTP, SCP, or NETCONF service).
Interaction
After the server grants the request, the client and the server start to
communicate with each other in the session.
In this stage, you can paste commands in text format and execute them
at the CLI. The text pasted at one time must be no more than 2000 bytes.
HP recommends that you paste commands in the same view. Otherwise,
the server might not be able to correctly execute the commands.
To execute commands of more than 2000 bytes, save the commands in
a configuration file, upload it to the server through SFTP, and use it to
restart the server.
SSH authentication methods
This section describes authentication methods that are supported by the device when it acts as an SSH
server.
Password authentication
The SSH server authenticates a client through the AAA mechanism. The password authentication process
is as follows:
1. The client sends the server an authentication request that includes the encrypted username and
password.
2. The server performs the following operations:
a. Decrypts the request to get the username and password in plain text.
b. Verifies the username and password locally or through remote AAA authentication.

 Loading...
Loading...