However both the source and destination network must be either IPv4 or IPv6. It is not
permissible to combine IPv4 and IPv6 addresses in a single rule. For this reason, two Drop All
rules will be required when using IPv6, one for IPv4 and one for IPv6 as shown below:
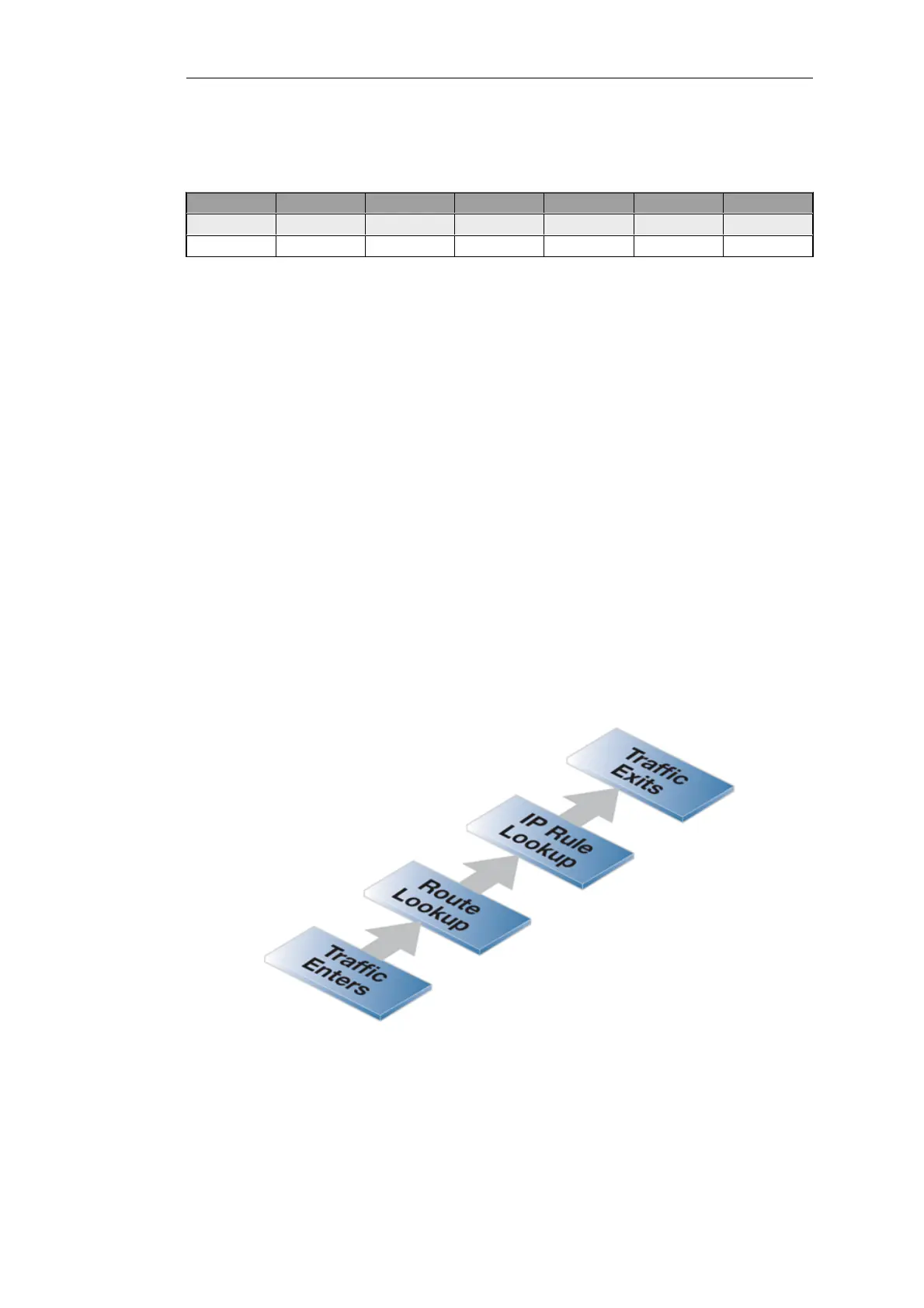
Name Action Source Iface Source Net Dest Iface Dest Net Service
DropAll Drop any all-nets any all-nets all_services
DropAll6 Drop any all-nets6 any all-nets6 all_services
For further discussion of this topic, see Section 3.2, “IPv6 Support”.
Traffic Flow Needs an IP Rule or an IP Policy Plus a Route
As stated above, when NetDefendOS is started for the first time, the default IP rules drop all
traffic so at least one IP rule must be added to allow traffic to flow. In fact, two NetDefendOS
components need to be present:
• A route must exist in a NetDefendOS routing table which specifies on which interface packets
should leave in order to reach their destination.
A second route must also exist that indicates the source of the traffic is found on the interface
where the packets enter.
• An IP rule or IP policy in a NetDefendOS IP rule set which specifies the security policy that
allows the packets from the source interface and network bound for the destination network
to leave the NetDefend Firewall on the interface decided by the route.
If the IP rule used is an Allow rule then this is bidirectional by default.
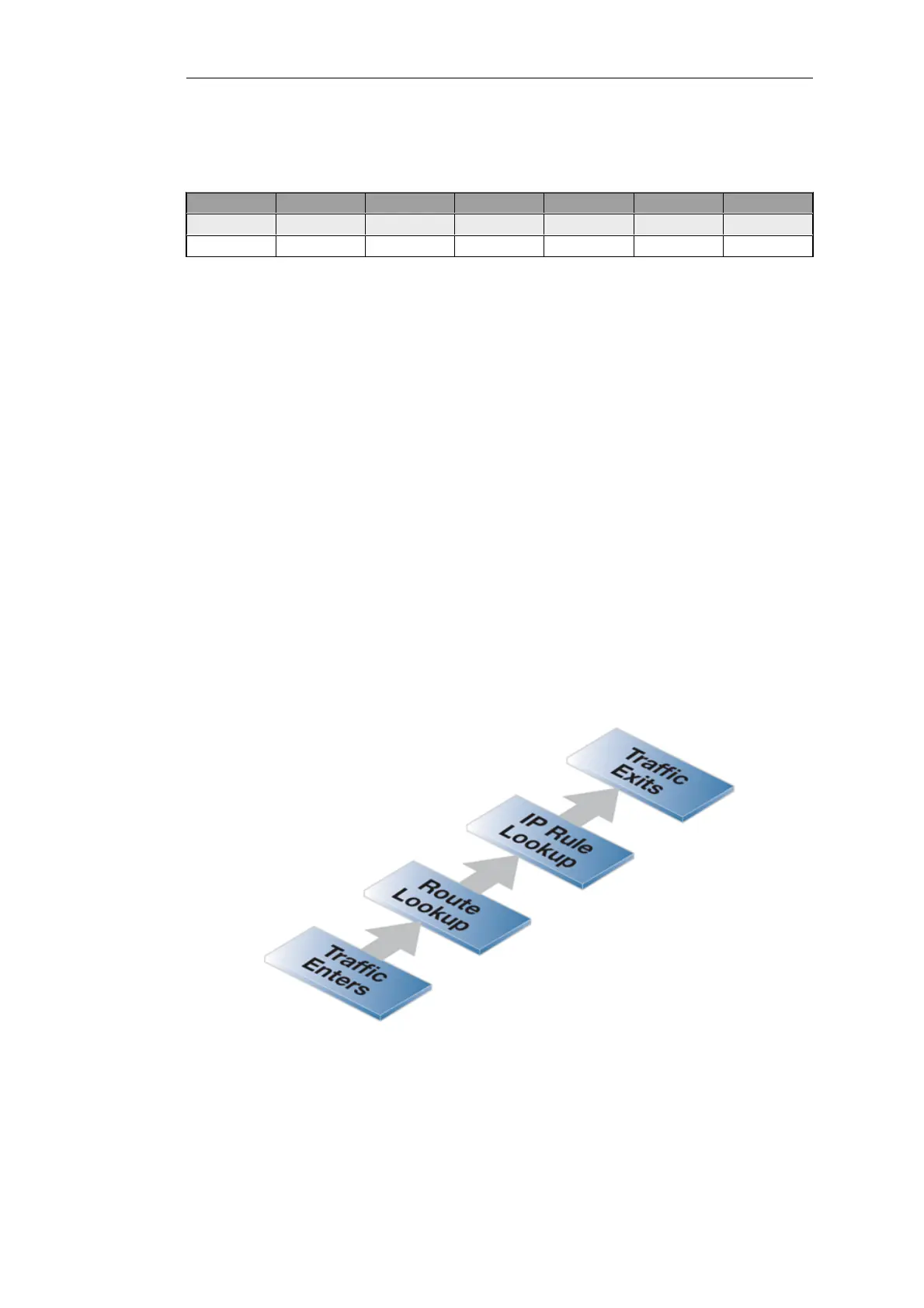
The ordering of these steps is important. The route lookup occurs first to determine the exiting
interface and then NetDefendOS looks for an IP rule or IP policy that allows the traffic to leave on
that interface. If a rule does not exist then the traffic is dropped.
Figure 3.12. Simplified NetDefendOS Traffic Flow
This description of traffic flow is an extremely simplified version of the full flow description found
in Section 1.3, “NetDefendOS State Engine Packet Flow”.
For example, before the route lookup is done, NetDefendOS first checks that traffic from the
Chapter 3: Fundamentals
231
 Loading...
Loading...