32
3. Enable accounting-on.
accounting-on enable
[
interval
seconds |
send-times ] *
By default, the accounting-on
feature is disabled.
Configuring the IP addresses of the security policy servers
The NAS verifies the validity of received control packets and accepts only control packets from
known servers. To use a security policy server that is independent of the AAA servers, configure the
IP address of the security policy server on the NAS.
The security policy server is the management and control center of the HPE EAD solution. To
implement all EAD functions, configure both the IP address of the security policy server and that of
the IMC Platform on the NAS.
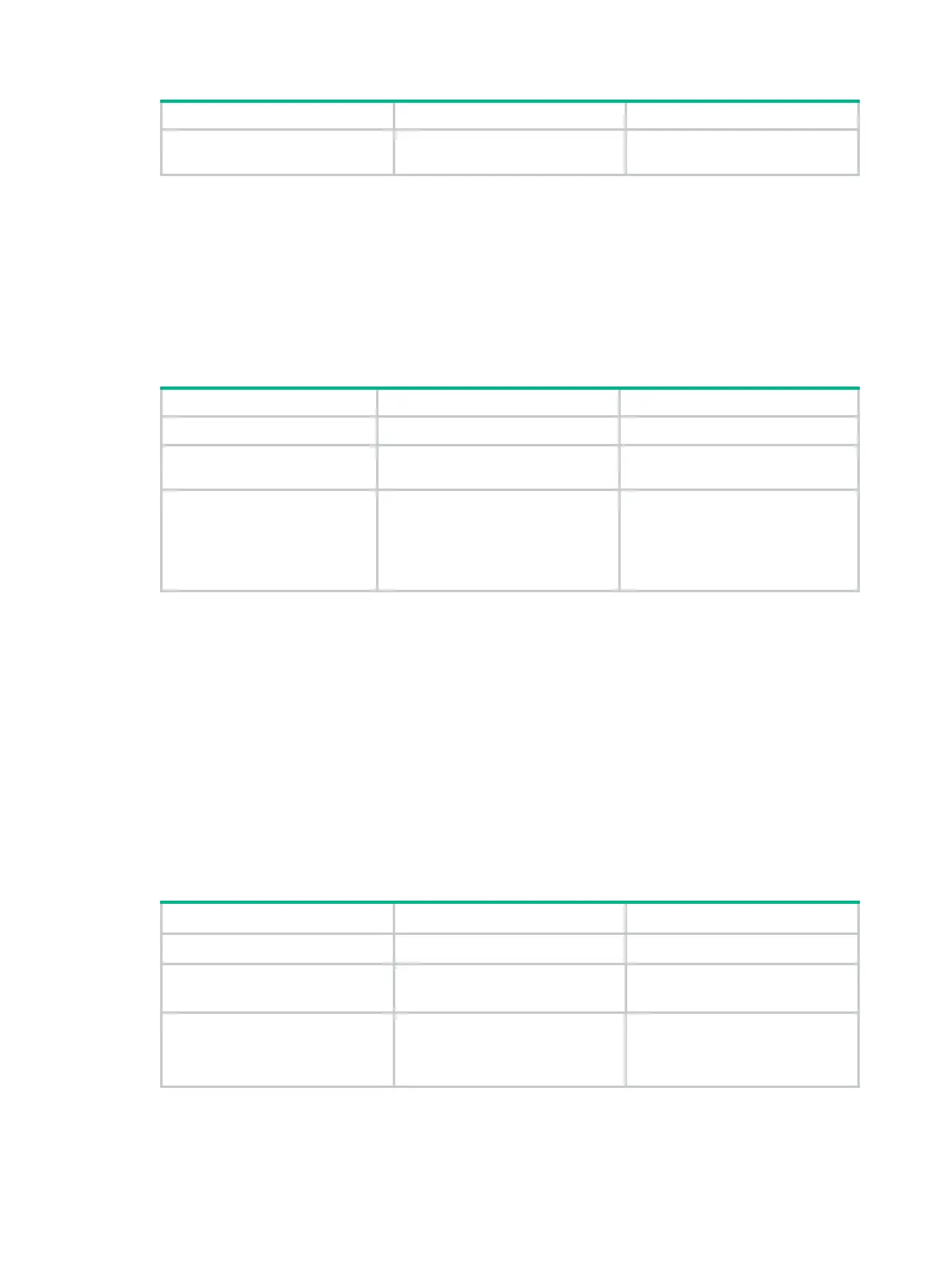
To configure the IP address of a security policy server for a scheme:
1. Enter system view.
system-view
N/A
2. Enter RADIUS scheme
view.
radius scheme
radius-scheme-name
N/A
3.
Specify a security policy
server.
security-policy-server
{ ipv4-address |
ipv6
ipv6-address }
[
vpn-instance
vpn-instance-name ]
By default, no security policy server
is specified for a scheme.
You can specify a maximum of
eight security policy servers for a
RADIUS scheme.
Configuring the Login-Service attribute check method for SSH, FTP, and terminal users
The device supports the following check methods for the Login-Service attribute (RADIUS attribute
15) of SSH, FTP, and terminal users:
• Strict—Matches Login-Service attribute values 50, 51, and 52 for SSH, FTP, and terminal
services, respectively.
• Loose—Matches the standard Login-Service attribute value 0 for SSH, FTP, and terminal
services.
An Access-Accept packet received for a user must contain the matching attribute value. Otherwise,
the user cannot log in to the device.
Use the loose check method only when the server does not issue Login-Service attribute values 50,
51, and 52 for SSH, FTP, and terminal users.
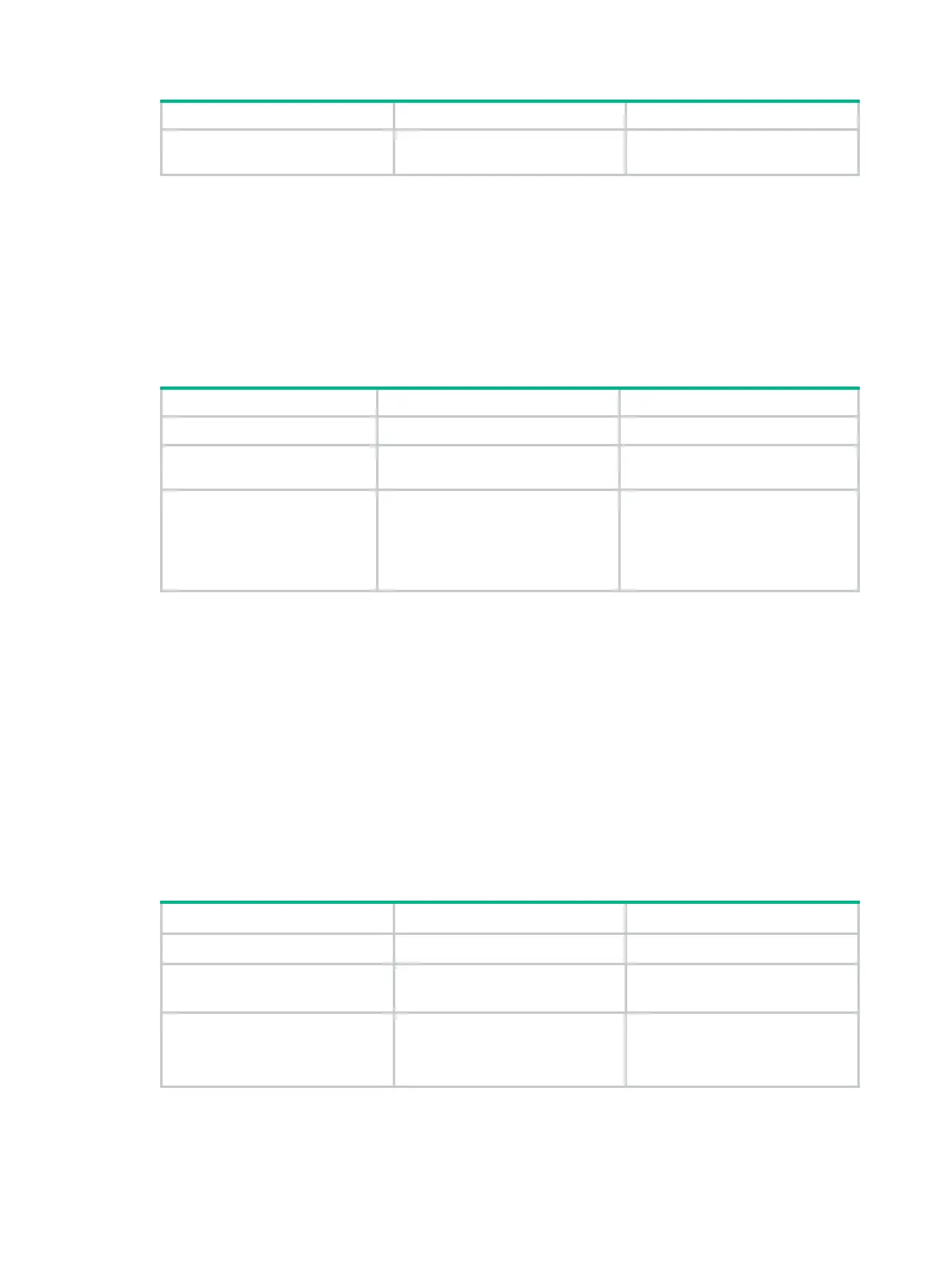
To configure the Login-Service attribute check method for SSH, FTP, and terminal users:
1. Enter system view.
system-view
N/A
2. Enter RADIUS scheme view.
radius scheme
radius-scheme-name
N/A
3. Configure the Login-Service
attribute check method for
SSH, FTP, and terminal
users.
attribute 15 check-mode
{
loose
|
strict
}
The default check method is
strict
.
Enabling SNMP notifications for RADIUS
When SNMP notifications are enabled for RADIUS, the SNMP agent supports the following
notifications generated by RADIUS:

 Loading...
Loading...