69
Benefits Limitations
• The processing is complex on the
access device.
EAP relay
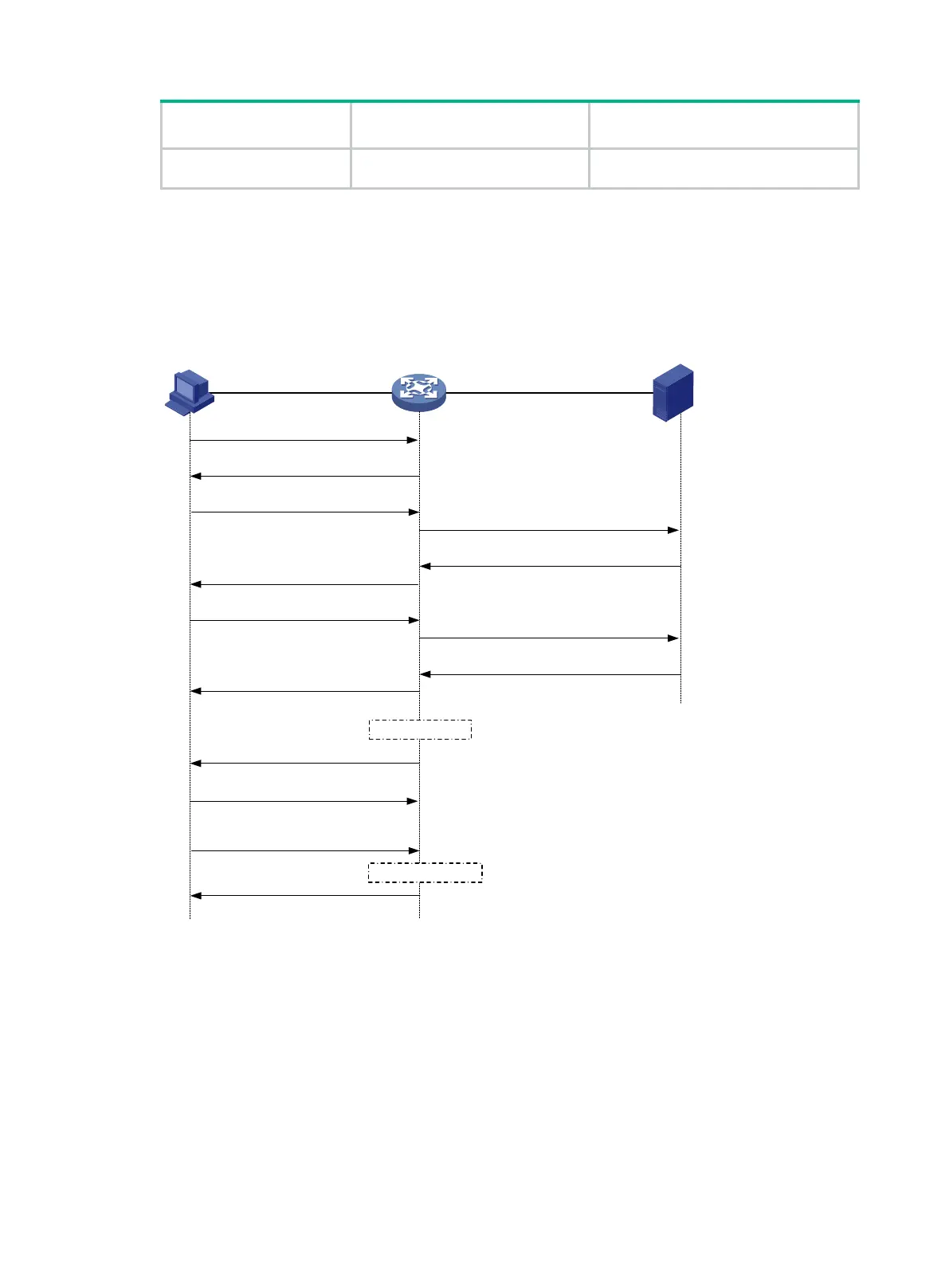
Figure 29 shows the basic 802.1X authentication procedure in EAP relay mode, assuming that
EAP-MD5 is used.
Figure 29 802.1X authentication procedure in EAP relay mode
The following steps describe the 802.1X authentication procedure:
1. When a user launches the 802.1X client and enters a registered username and password, the
802.1X client sends an EAPOL-Start packet to the access device.
2. The access device responds with an Identity EAP-Request packet to ask for the client
username.
3. In response to the Identity EAP-Request packet, the client sends the username in an Identity
EAP-Response packet to the access device.
4. The access device relays the Identity EAP-Response packet in a RADIUS Access-Request
packet to the authentication server.
5. The authentication server uses the identity information in the RADIUS Access-Request to
search its user database. If a matching entry is found, the server uses a randomly generated
EAPOL
EAPOR
(1) EAPOL-Start
(2) EAP-Request/Identity
(3) EAP-Response/Identity
(6) EAP-Request/MD5 challenge
(10) EAP-Success
(7) EAP-Response/
MD
5 challenge
(4) RADIUS Access-Request
(EAP-Response/Identity)
(5) RADIUS Access-
Challenge
(EAP-Request
/MD5 challenge)
(9
) RADIUS Access-Accept
(EAP-Success)
(8) RADIUS Access-
Request
(EAP-Response/MD5 challenge
)
(11) EAP-Request/Identity
(12) EAP-Response/Identity
(13) EAPOL-Logoff
...
Client Device Authentication server
Port authorized
Port unauthorized
(14) EAP-Failure

 Loading...
Loading...