Preventing the Leakage of Sensitive Information Through Git (Developer Protection)
R81 Harmony Endpoint Server Administration Guide|384
Preventing the Leakage of Sensitive Information
Through Git (Developer Protection)
Developer Protection prevents developers leaking sensitive information such as RSA keys,
passwords, and access tokens though the Git version control system. It also warns the
developer when vulnerable external dependencies are used in AWS Lambda.
Developer Protection intercepts git commit commands issued by the developer, and scans
all modified files in a Git repository. It prevents the uploading of private information in plain text
from Endpoint Security client computers to public locations.
Developer protection is supported on Endpoint Security Client release E82.50 and higher.
To configure Developer protection:
1. In the SmartEndpoint Policy tab, open the Application Control rule.
2. Click the Developer Protection action and choose an option:
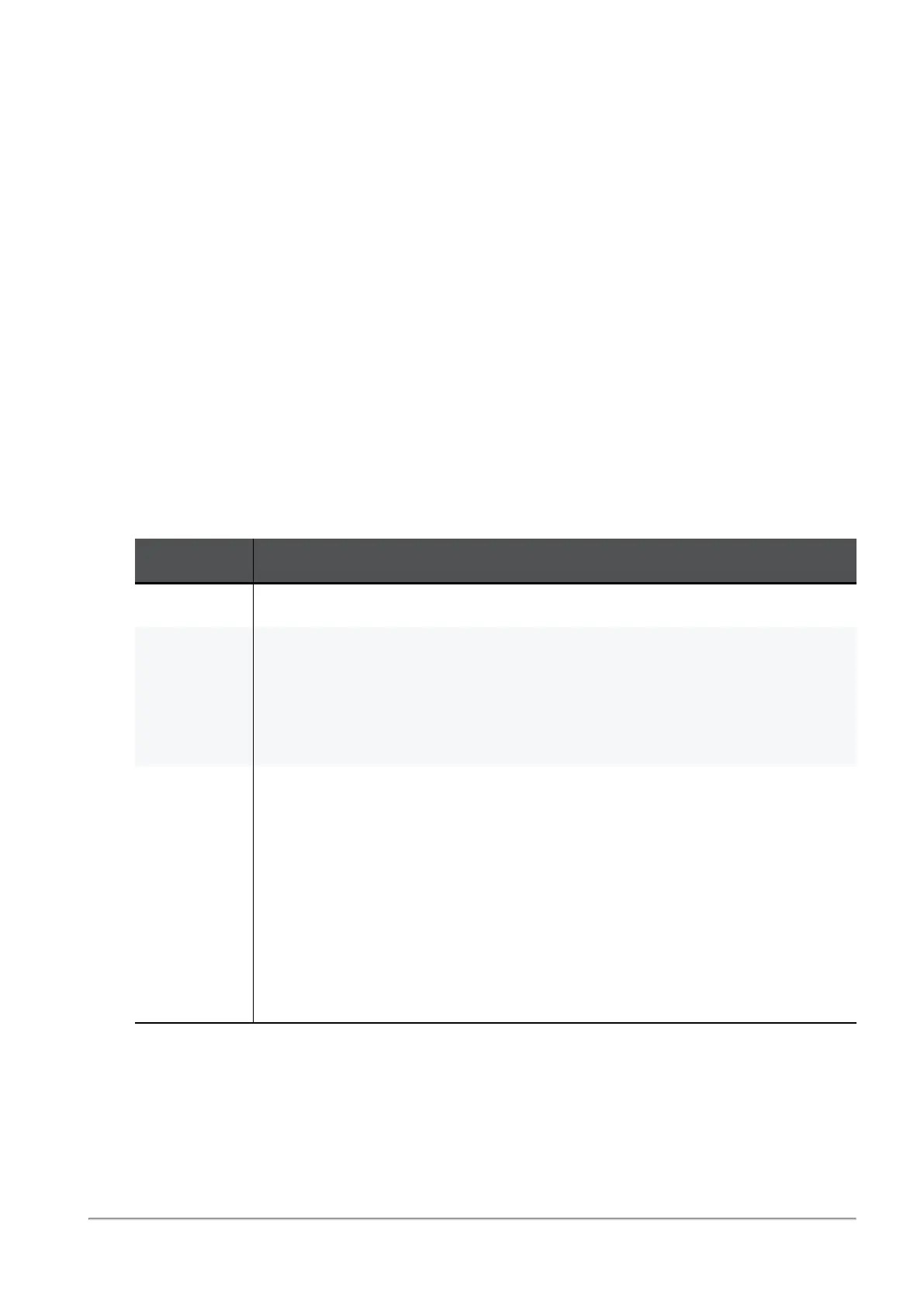
Option Explanation
Disabled Developer Protection is disabled. This is the default.
Detect
mode
n
Information leakage is detected and a log message is generated,
but the Commit is allowed.
n
The administrator can examine the audit log
Detect
messages of
the Application Control component.
n
The developer sees a notification on the client computer.
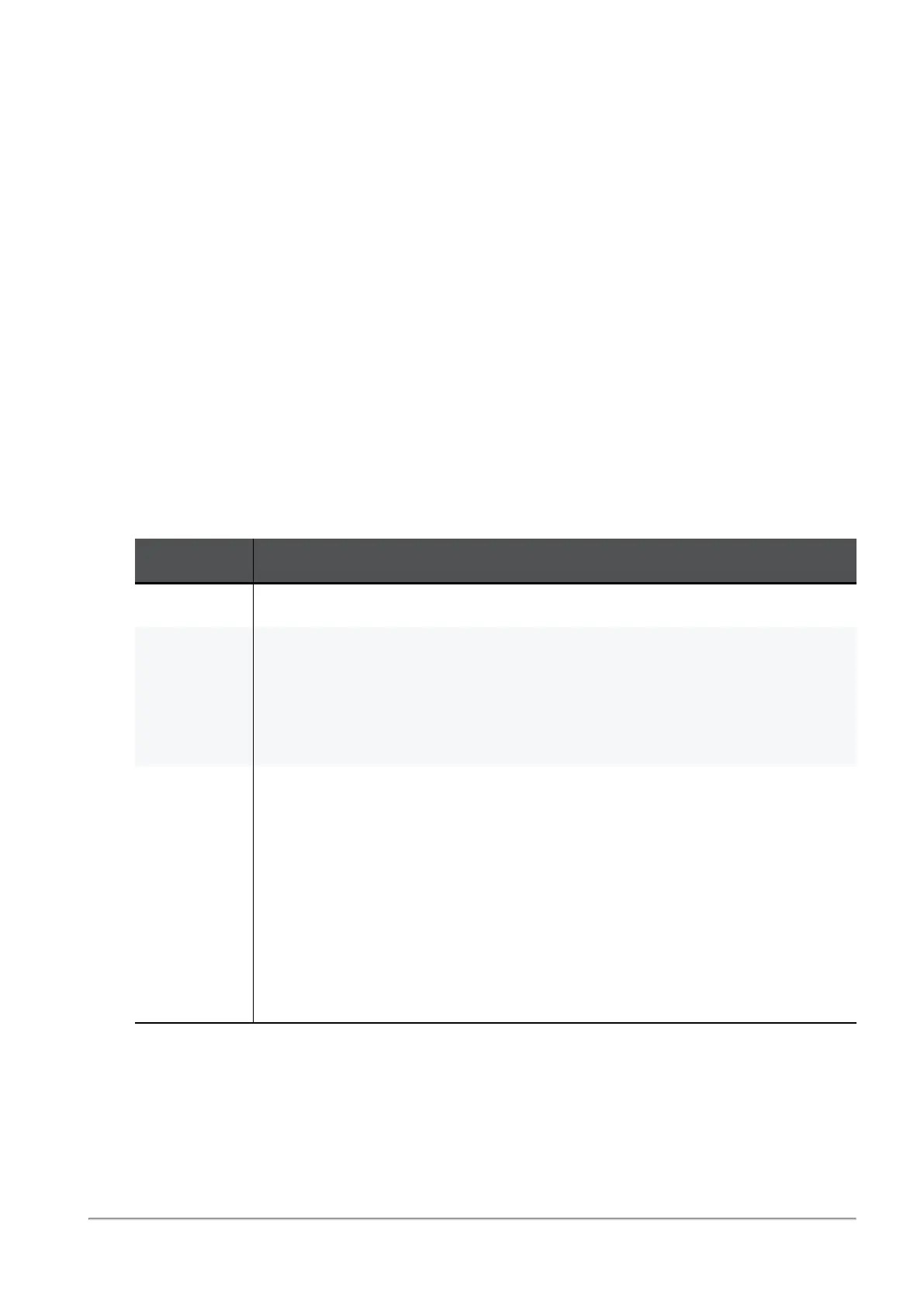
Prevent
mode
n
Information leakage is detected, a log message is generated, and
the Commit is blocked.
n
The administrator can examine the audit log
Prevent
messages of
the Application Control component.
n
The developer sees a warning notification on the client
computer.The developer can decide to override the notification
and allow the traffic (with or without giving a justification).
n
The notification message suggests how to fix the problem. For
example, by adding a file to .gitignore, or updating the version
in package.json
3. Install the Application Control Policy. See
"Installing the Application Control Policy " on
page386
.

 Loading...
Loading...