User Interface
R&S
®
GP-E/GP-S
109User Manual v16.2.1 ─ 01
●
legacy – uses IKEv1 settings to provide access to devices that do not support
IKEv2
●
secure – uses the Elliptic Curve key exchange algorithm (Diffie-Hellman group
21)
●
windows – dedicated IKEv2 profile to meet the requirements of Windows
For more detailed information on IPsec profiles, see the following sections.
IPsec Profiles Overview
Navigate to "VPN > IPsec > Profiles" to display the list of IPsec profiles that are cur-
rently defined on the system in the item list bar.
In the expanded view, the columns of the table display the "Name" of the IPsec profile,
the type of Internet "Key Exchange" method used, how long the session key is valid
for, and how many times keying and rekeying processes are started to generate an ini-
tial or a new session key. The buttons in the last column allow you to view and adjust
the settings for an existing IPsec profile, create a profile based on a copy of an existing
IPsec profile, or delete a profile from the system.
For further information, see Chapter 3.2, "Icons and Buttons", on page 21.
IPsec Profiles Settings
Under "VPN > IPsec > Profiles", you can add a new or edit an existing IPsec profile.
The IPsec "Profile" settings allow you to configure the following elements:
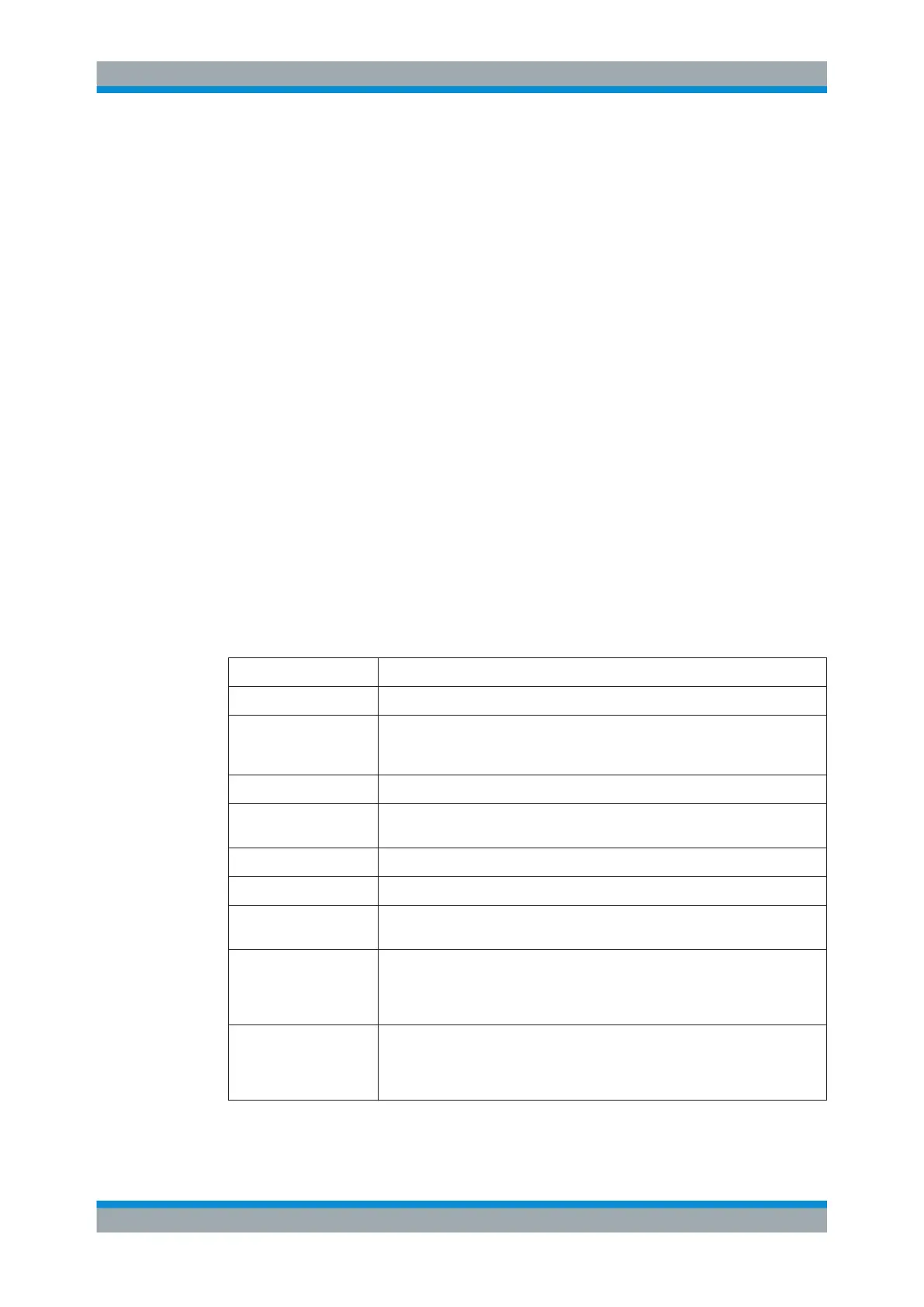
Field Description
"Name" Enter a unique name for the IPsec profile.
"Aggressive Mode" Select this checkbox for the IKEv1 protocol if your client supports only this
mode for the IKE negotiation. Otherwise, the more secure Main Mode is used
by default.
"Key Exchange" Select the desired Internet key exchange method from the drop-down list.
"IKE lifetime" Specify the timeout (in minutes) after which the IKE connection expires and a
new Phase 1 exchange is performed.
"Key lifetime" Define the duration (in minutes) for which a session key remains valid.
"Margin time" Specify how long (in minutes) before the expiry of a session key rekeying starts.
"Keying tries" Set how many times keying and rekeying processes start to generate an initial
or new session key.
"Internet Key Exchange
(IKE)"
Define the Internet Key Exchange settings. Select the desired "Encryption"
algorithm, the cryptographic hash to verify message "Integrity" and the "Diffie-
Hellman Group" for Phase 1 of the IKE negotiation. To add new IKE settings,
select the desired options from the drop-down lists or click "Add" .
"Encapsulating Security
Payload (ESP)"
Define the Encapsulating Security Payload settings. Select the desired "Encryp-
tion" algorithm, the cryptographic hash to verify message "Integrity" and the
"Diffie-Hellman Group" for Phase 2 of the IKE negotiation. To add new ESP set-
tings, select the desired options from the drop-down lists or click "Add" .
Menu Reference
 Loading...
Loading...