181
Configuring Switch-Based Authentication
How to Configure Switch-Based Authentication
Configuring Secure HTTP Servers and Clients
Configuring a CA Trustpoint
Configuring the Secure HTTP Server
Before You Begin
If you are using a certificate authority for certification, you should use the previous procedure to configure the CA
trustpoint on the switch before enabling the HTTP server. If you have not configured a CA trustpoint, a self-signed
certificate is generated the first time that you enable the secure HTTP server. After you have configured the server, you
can configure options (path, access list to apply, maximum number of connections, or timeout policy) that apply to both
standard and secure HTTP servers.
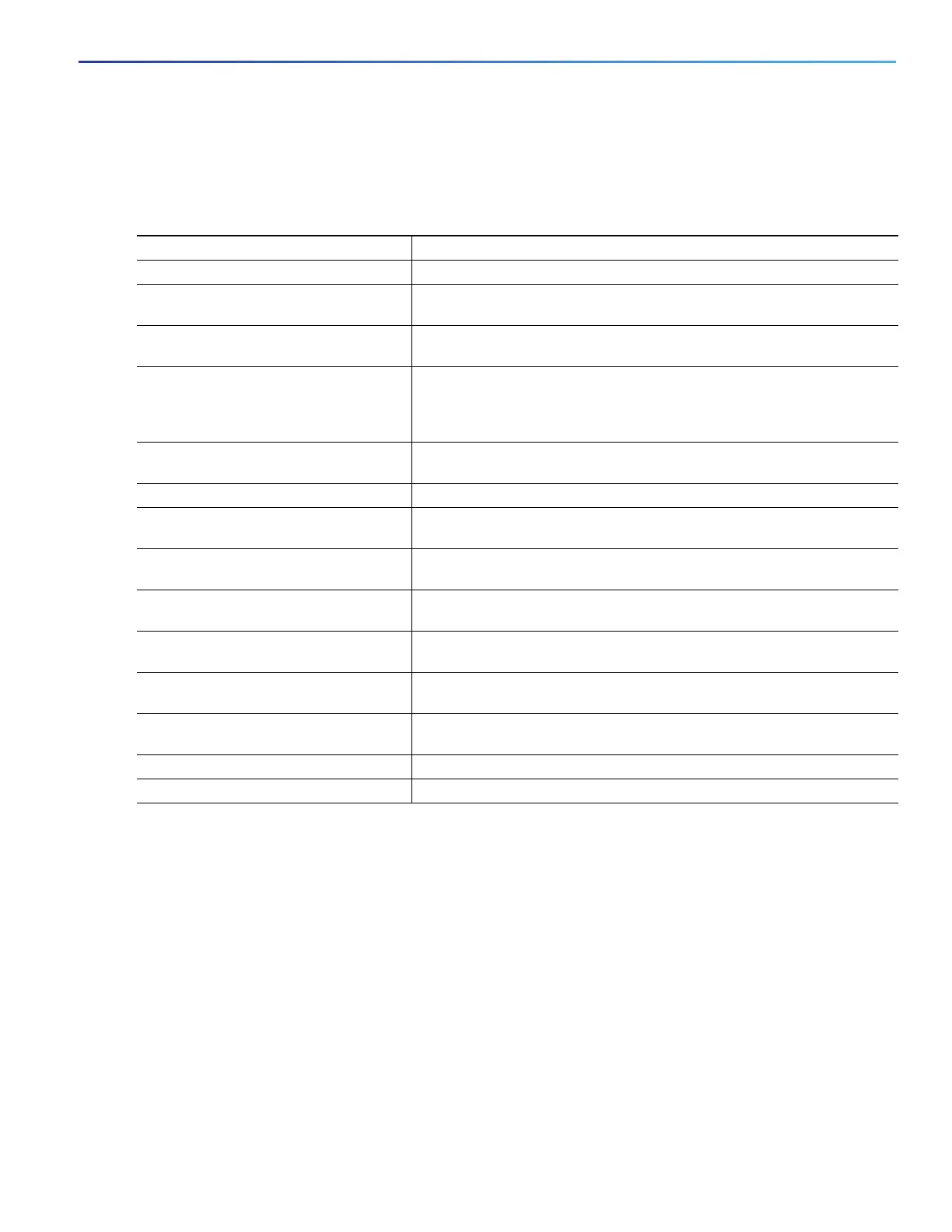
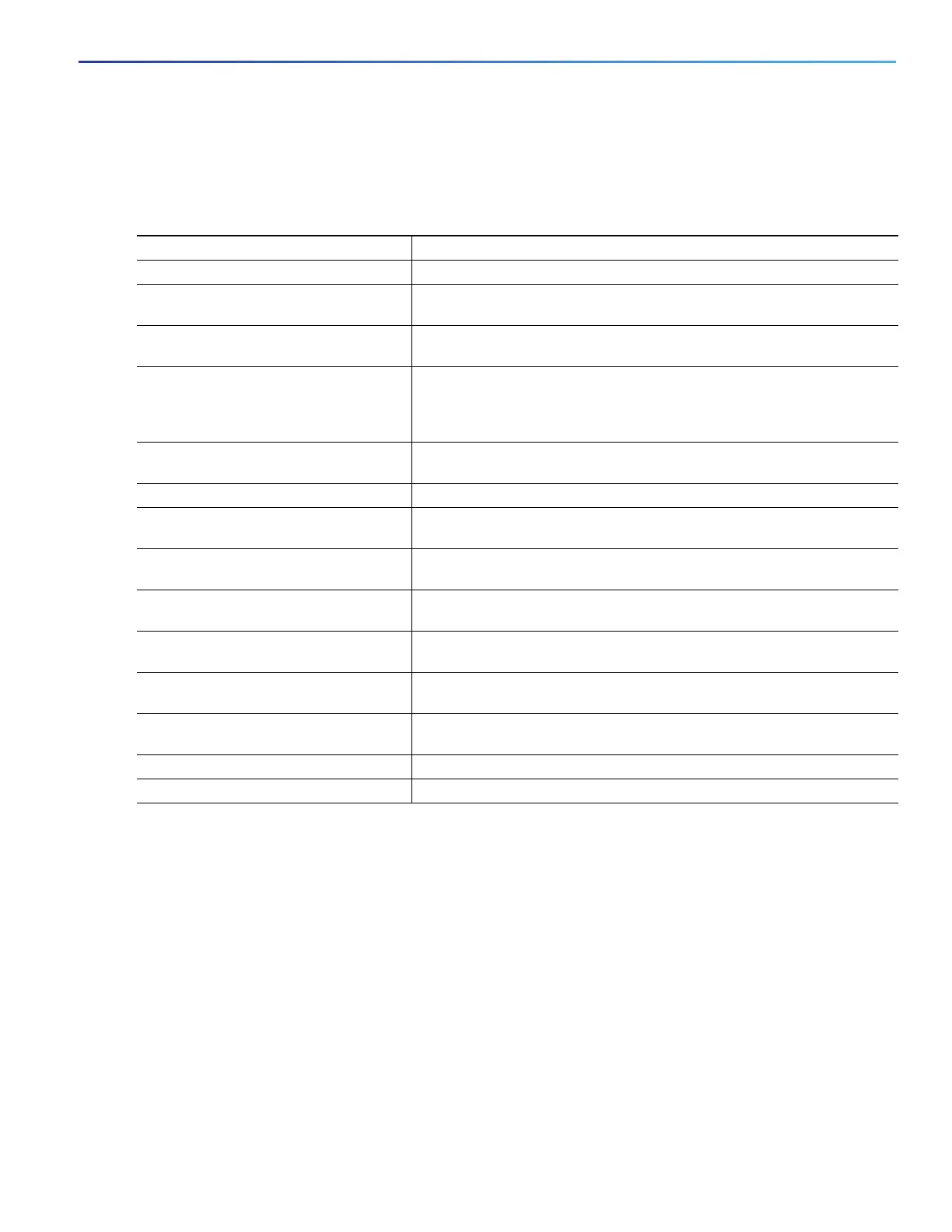
Command Purpose
1. configure terminal Enters global configuration mode.
2. hostname hostname Specifies the hostname of the switch (required only if you have not
previously configured a hostname).
3. ip domain-name domain-name Specifies the IP domain name of the switch (required only if you have not
previously configured an IP domain name).
4. crypto key generate rsa (Optional) Generates an RSA key pair. RSA key pairs are required before
you can obtain a certificate for the switch. RSA key pairs are generated
automatically. You can use this command to regenerate the keys, if
needed.
5. crypto ca trustpoint name Specifies a local configuration name for the CA trustpoint and enter CA
trustpoint configuration mode.
6. enrollment url url Specifies the URL to which the switch should send certificate requests.
7. enrollment http-proxy host-name
port-number
(Optional) Configures the switch to obtain certificates from the CA
through an HTTP proxy server.
8. crl query url Configures the switch to request a certificate revocation list (CRL) to
ensure that the certificate of the peer has not been revoked.
9. primary (Optional) Specifies that the trustpoint should be used as the primary
(default) trustpoint for CA requests.
10. exit Exits CA trustpoint configuration mode and returns to global configuration
mode.
11. crypto ca authentication name Authenticates the CA by getting the public key of the CA. Uses the same
name used in Step 5.
12. crypto ca enroll name Obtains the certificate from the specified CA trustpoint. This command
requests a signed certificate for each RSA key pair.
13. end Returns to privileged EXEC mode.
14. show crypto ca trustpoints Verifies the configuration.
 Loading...
Loading...