D-Link DSR-Series User Manual 199
Section 8 - Security
Attack Checks
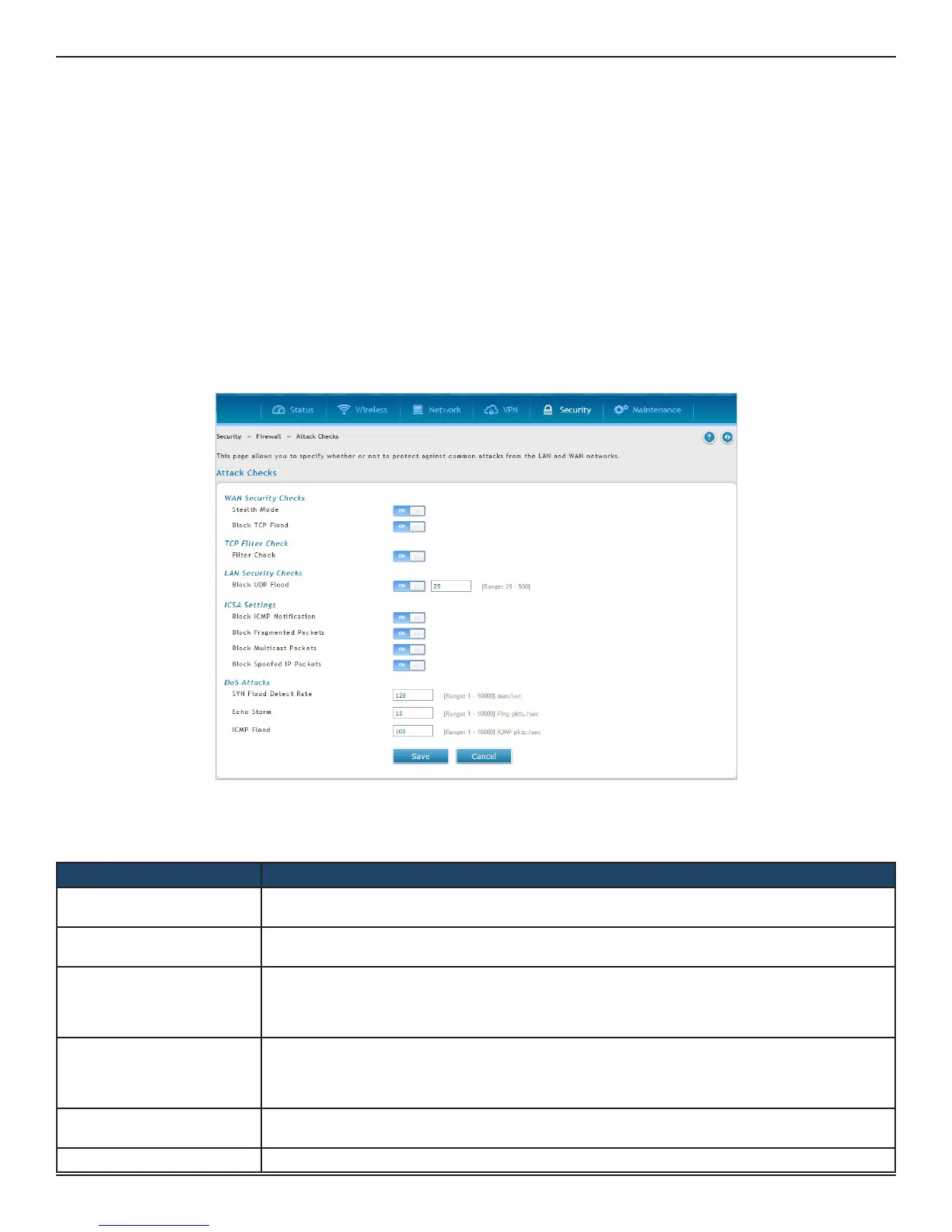
Path: Security > Firewall > Attack Checks
Attacks can be malicious security breaches or unintentional network issues that render the router unusable
Attack checks allow you to manage WAN security threats such as continual ping requests and discovery via ARP
scans. TCP and UDP ood attack checks can be enabled to manage extreme usage of WAN resources.
Additionally certain Denial-of-Service (DoS) attacks can be blocked. These attacks, if uninhibited, can use up
processing power and bandwidth and prevent regular network services from running normally. ICMP packet
ooding, SYN trac ooding, and Echo storm thresholds can be congured to temporarily suspect trac from
the oending source.
1. Click Security > Firewall > Attack Checks.
2. Complete the elds from the table below and click Save.
Field Description
Stealth Mode
If this option is toggled to ON, the router will not respond to port scans from the WAN. This makes it
less susceptible to discovery and attacks.
Block TCP Flood
If this option is toggled to ON, the router will drop all invalid TCP packets and be protected from a
SYN ood attack.
Filter Check
If this option is enabled, then router will drop invalid TCP packets(FIN,RST and ACK) going with
SNAT while the connection is closed. Some of the other packets like TCP OUT-OF-WINDOW are also
considered to be invalid. Disable this option while taking performance in Ixia setup as enabling this
option will eect the throughput.
Block UDP Flood
If this option is toggled to ON, the router will not accept more than the congured value in ‘UDP
Connection Limit’ which indicates simultaneous, active UDP connections from a single computer
on the LAN. You can set the number of simultaneous active UDP connections to be accepted from a
single computer on the LAN; the default is 25 and the range is 25 to 500.
Block ICMP Notication
Toggle to ON to prevent ICMP packets from being identied as such. ICMP packets, if identied, can
be captured and used in a Ping (ICMP) ood DoS attack.
Block Fragmented Packets Toggle to ON to drop any fragmented packets through or to the gateway

 Loading...
Loading...