97
Step Command Remarks
If no DHCP snooping entry
changes, the backup file is not
updated.
Enabling DHCP starvation attack protection
A DHCP starvation attack occurs when an attacker constantly sends forged DHCP requests that
contain identical or different sender MAC addresses in the chaddr field to a DHCP server. This
attack exhausts the IP address resources of the DHCP server so legitimate DHCP clients cannot
obtain IP addresses. The DHCP server might also fail to work because of exhaustion of system
resources. For information about the fields of DHCP packet, see "DHCP message format."
Y
ou can prevent DHCP starvation attacks in the following ways:
• If the forged DHCP requests contain different sender MAC addresses, use the mac-address
max-mac-count command to limit the number of MAC addresses that a Layer 2 port can learn.
For more information about the command, see Layer 2—LAN Switching Command Reference.
• If the forged DHCP requests contain the same sender MAC address, perform this task to
enable MAC address check for DHCP snooping. This feature compares the chaddr field of a
received DHCP request with the source MAC address field in the frame header. If they are the
same, the request is considered valid and forwarded to the DHCP server. If not, the request is
discarded.
To enable MAC address check:
Step Command Remarks
1. Enter system view.
system-view
N/A
2. Enter interface view.
interface
interface-type
interface-number
N/A
3. Enable MAC address check.
dhcp snooping check mac-address
By default, MAC address
check is disabled.
Enabling DHCP-REQUEST attack protection
The following matrix shows the feature and hardware compatibility:
Hardware
DHCP-REQUEST attack protection
compatibility
MSR954(JH296A/JH297A/JH298A/JH299A/JH373A) No
MSR958(JH300A/JH301A) No
MSR1002-4/1003-8S Yes
MSR2003 Yes
MSR2004-24/2004-48 Yes
MSR3012/3024/3044/3064 Yes
MSR4060/4080 Yes

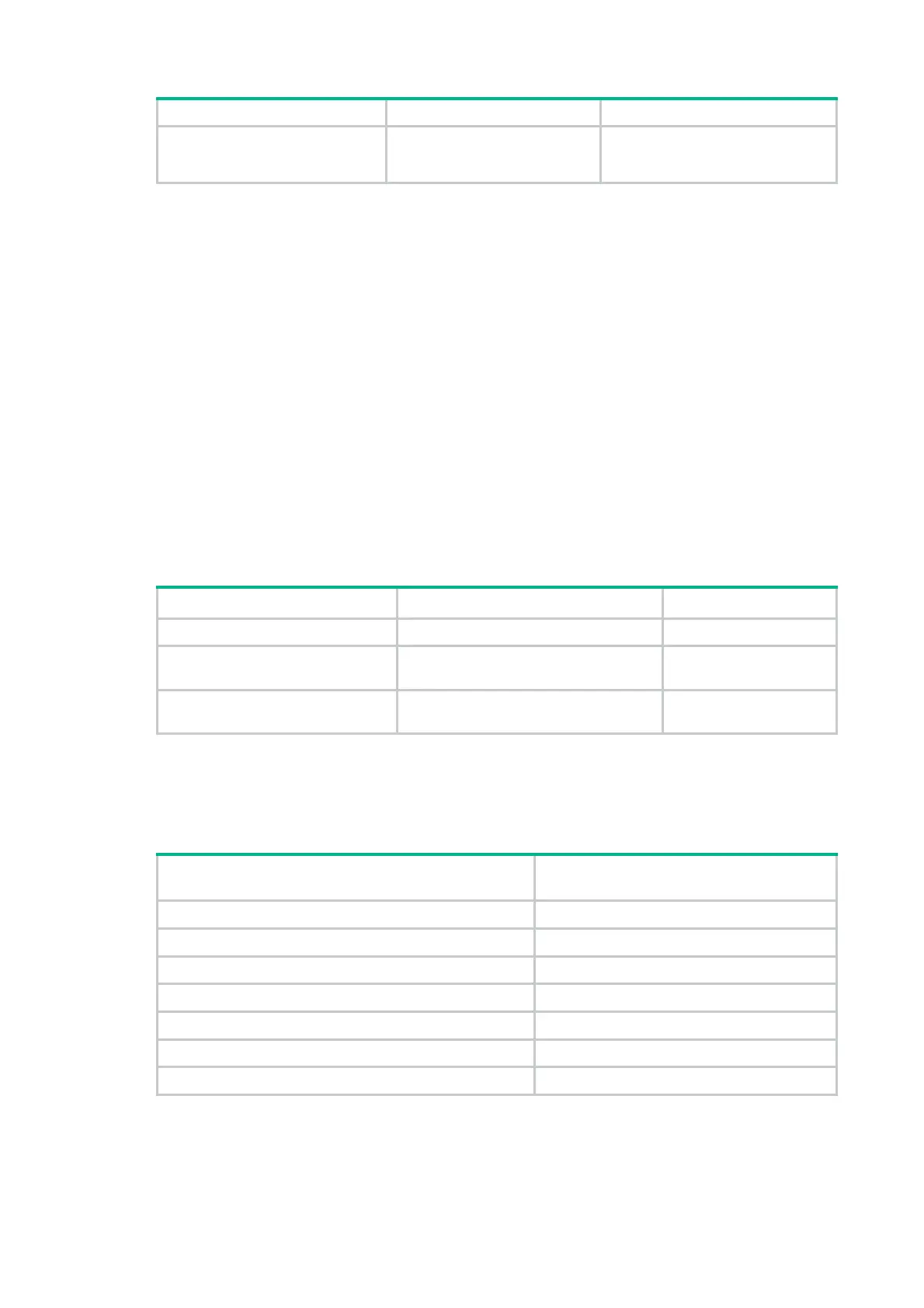 Loading...
Loading...