7-17
Catalyst 3750 Metro Switch Software Configuration Guide
78-15870-01
Chapter 7 Configuring Switch-Based Authentication
Controlling Switch Access with RADIUS
Beginning in privileged EXEC mode, follow these steps to enable TACACS+ accounting for each Cisco
IOS privilege level and for network services:
To disable accounting, use the no aaa accounting {network | exec} {start-stop} method1... global
configuration command.
Displaying the TACACS+ Configuration
To display TACACS+ server statistics, use the show tacacs privileged EXEC command.
Controlling Switch Access with RADIUS
This section describes how to enable and configure the RADIUS, which provides detailed accounting
information and flexible administrative control over authentication and authorization processes.
RADIUS is facilitated through AAA and can be enabled only through AAA commands.
Note For complete syntax and usage information for the commands used in this section, refer to the Cisco IOS
Security Command Reference for Release 12.1.
This section contains this configuration information:
• Understanding RADIUS, page 7-18
• RADIUS Operation, page 7-19
• Configuring RADIUS, page 7-20
• Displaying the RADIUS Configuration, page 7-31
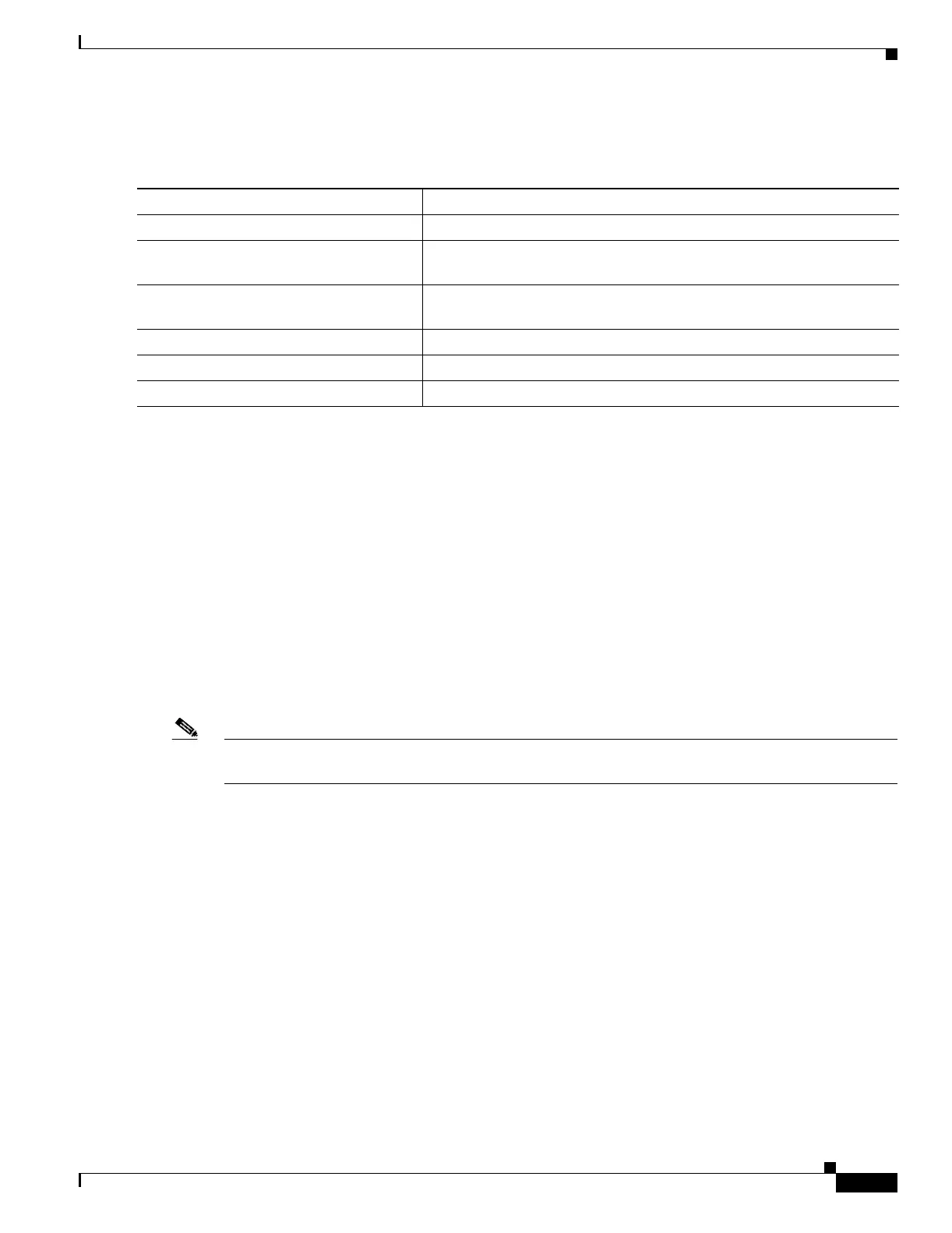
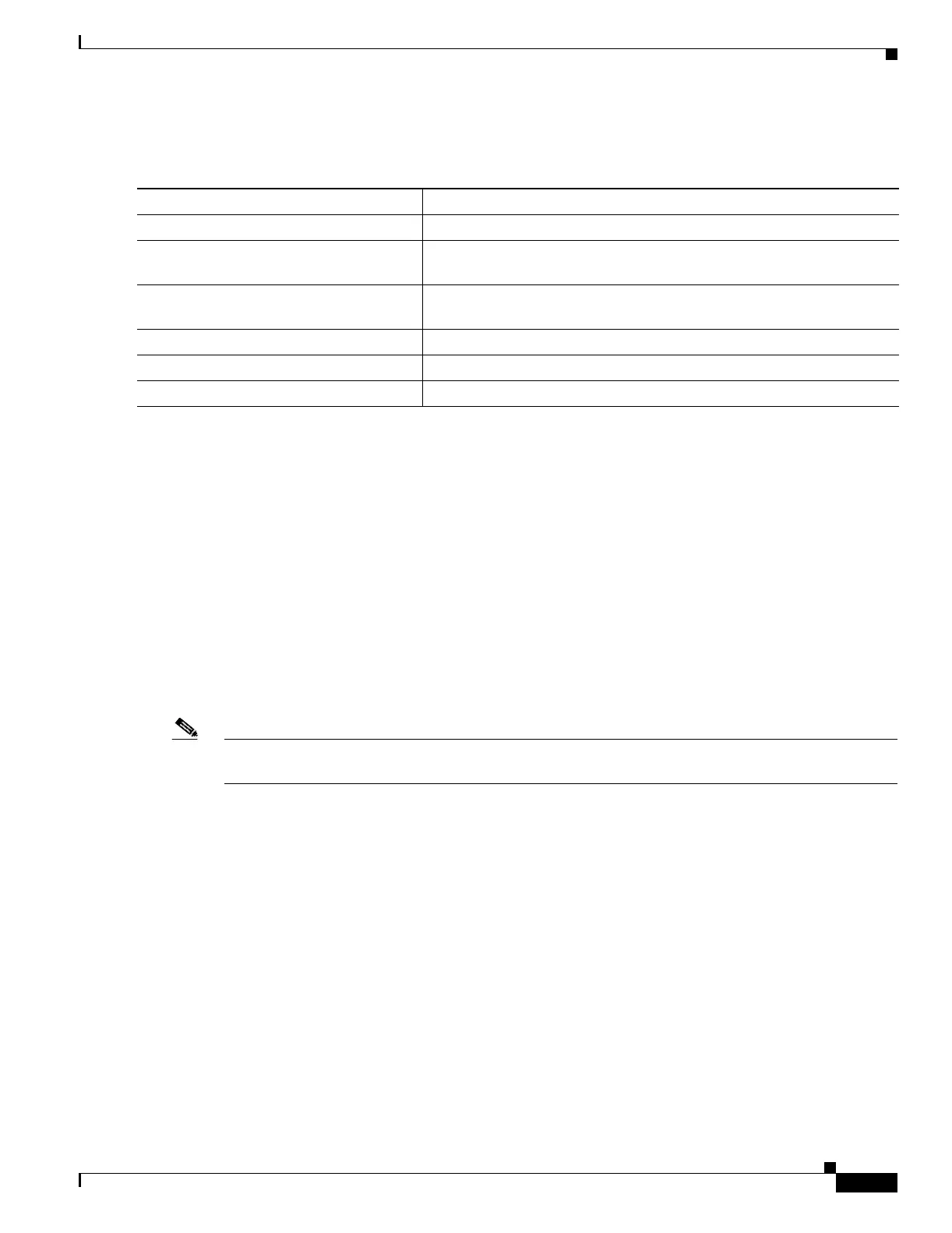
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
aaa accounting network start-stop
tacacs+
Enable TACACS+ accounting for all network-related service requests.
Step 3
aaa accounting exec start-stop tacacs+ Enable TACACS+ accounting to send a start-record accounting notice at
the beginning of a privileged EXEC process and a stop-record at the end.
Step 4
end Return to privileged EXEC mode.
Step 5
show running-config Verify your entries.
Step 6
copy running-config startup-config (Optional) Save your entries in the configuration file.

 Loading...
Loading...