428
Enabling protection against Naptha attacks
Naptha attacks are similar to the SYN Flood attacks. Attackers can perform Naptha attacks by using
the six TCP connection states (CLOSING, ESTABLISHED, FIN_WAIT_1, FIN_WAIT_2, LAST_ACK,
and SYN_RECEIVED), and SYN Flood attacks by using only SYN_RECEIVED state.
Naptha attackers control a huge amount of hosts to establish TCP connections with the server, keep
these connections in same state (any of the six), and request for no data so as to exhaust the
memory resource of the server. As a result, the server cannot process normal services.
Protection against Naptha attacks mitigates such attacks by accelerating the aging of TCP
connections in a state. After the feature is enabled, the device (serving as a TCP server) periodically
checks the number of TCP connections in each state. If the device detects that the number of TCP
connections in a state exceeds the maximum number, it considers that a Naptha attack occurs and
accelerates the aging of TCP connections in this state. The device stops accelerating the aging of
TCP connections when the number of TCP connections in the state is less than 80% of the maximum
number (1 at least).
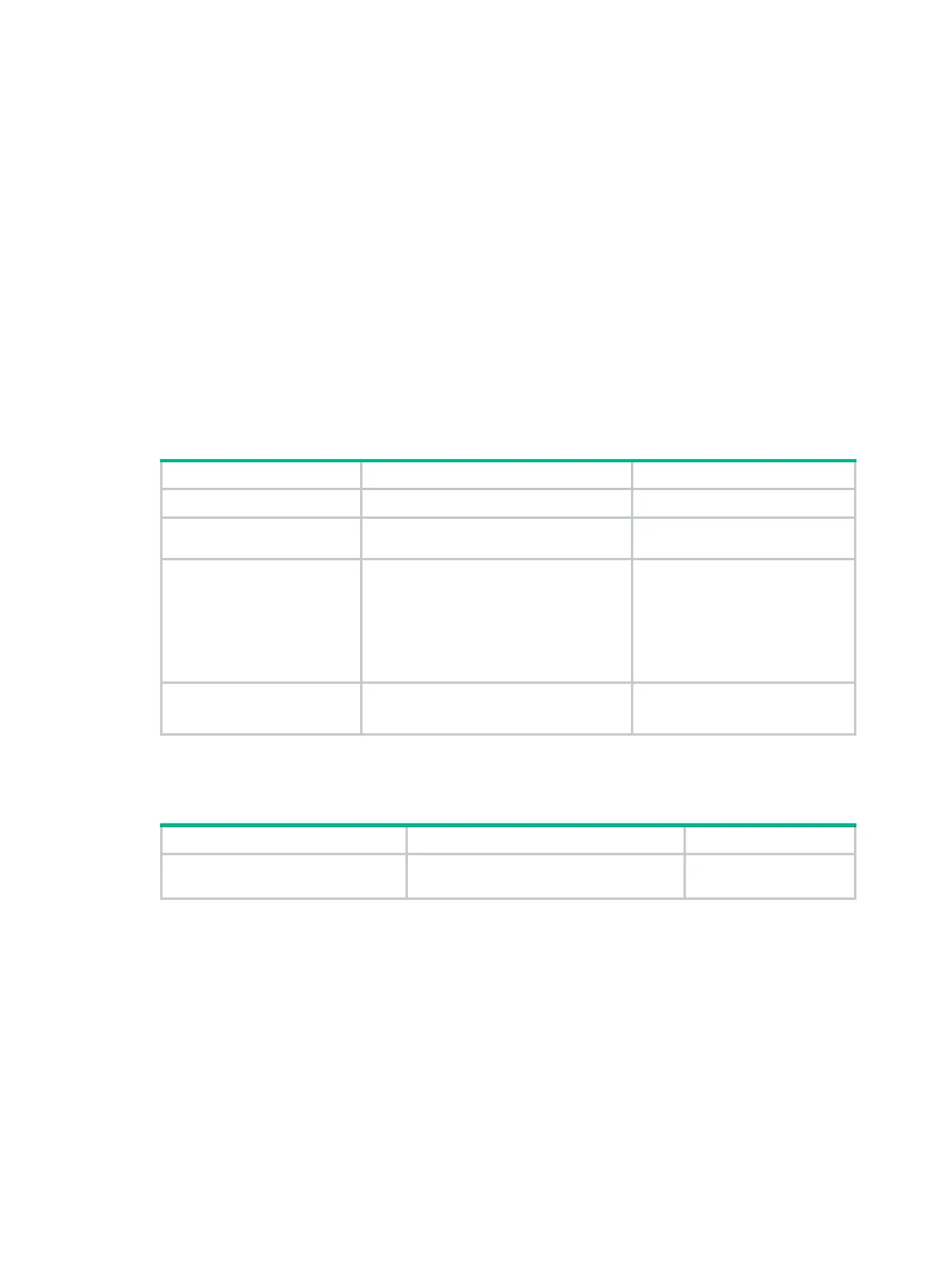
To enable the protection against Naptha attack:
Step Command Remarks
1. Enter system view.
system-view
N/A
2. Enable the protection
against Naptha attack.
tcp anti-naptha enable
Disabled by default.
3. Configure the maximum
number of TCP
connections in a state.
tcp state
{
closing
|
established
|
fin-wait-1
|
fin-wait-2
|
last-ack
|
syn-received
}
connection-number
number
Optional.
5 by default.
If the maximum number of TCP
connections in a state is 0, the
aging of TCP connections in this
state is not accelerated.
4. Configure the TCP
state check interval.
tcp timer check-state
timer-value
Optional.
30 seconds by default.
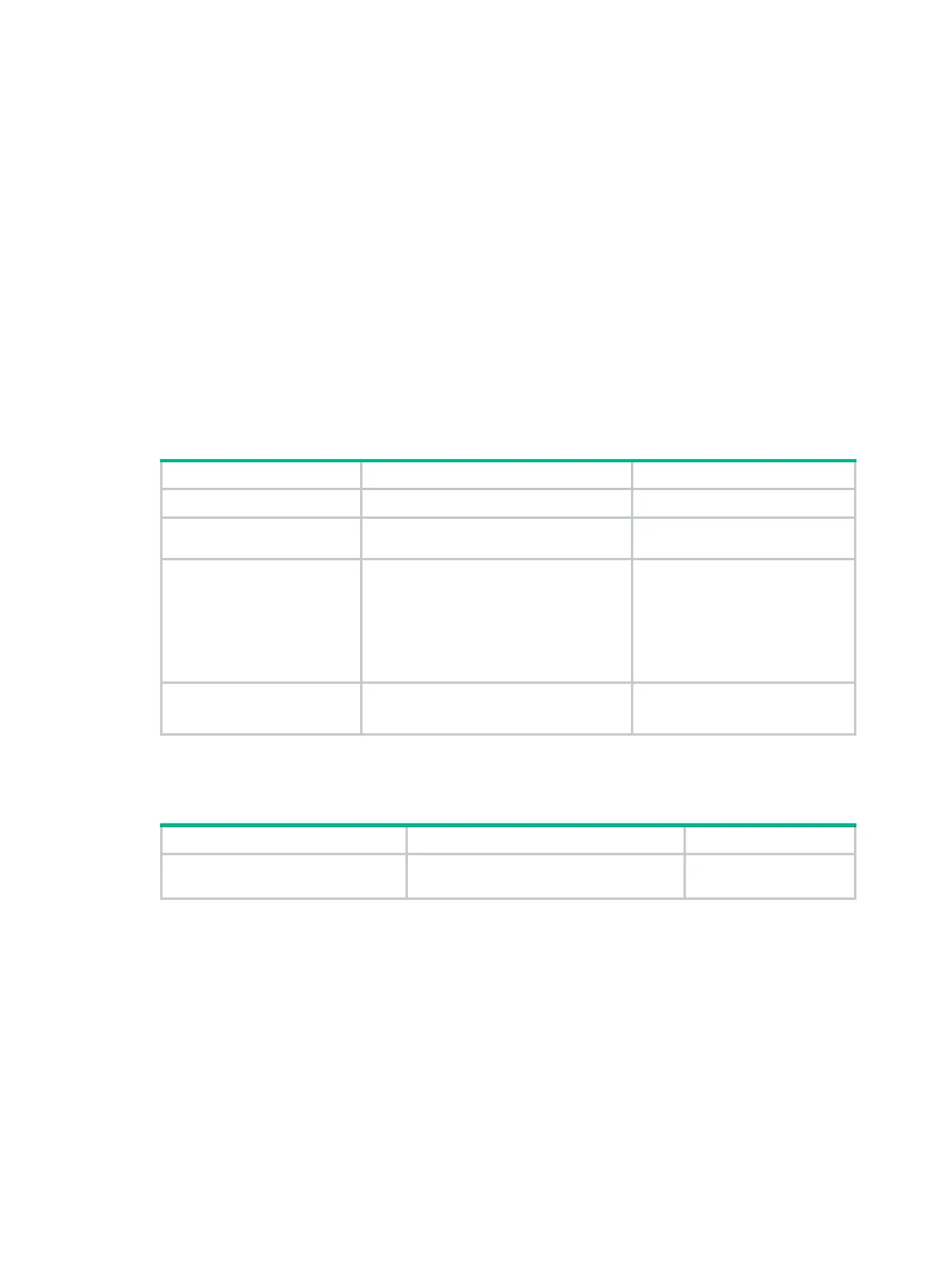
Displaying and maintaining TCP attack protection
Task Command Remarks
Display current TCP connection
state.
display tcp status
[
|
{
begin
|
exclude
|
include
} regular-expression ]
Available in any view.

 Loading...
Loading...