{<sec-model [ver1 | ver2c | ver3>]} Configures the security model used for SNMPv3
notification messages sent to the management
station configured with the snmpv3
targetaddress command in Step 5.
If you configure the security model as ver3, you
must also configure the message processing value as
ver3.
{msg-processing {<ver1 | ver2c | ver3>}
[noaut | auth | priv]}
Configures the algorithm used to process messages
sent to the SNMPv3 target address.
If you configure the message processing value as
ver3 and the security model as ver3, you must also
configure a security services level ( noauth, auth, or
priv).
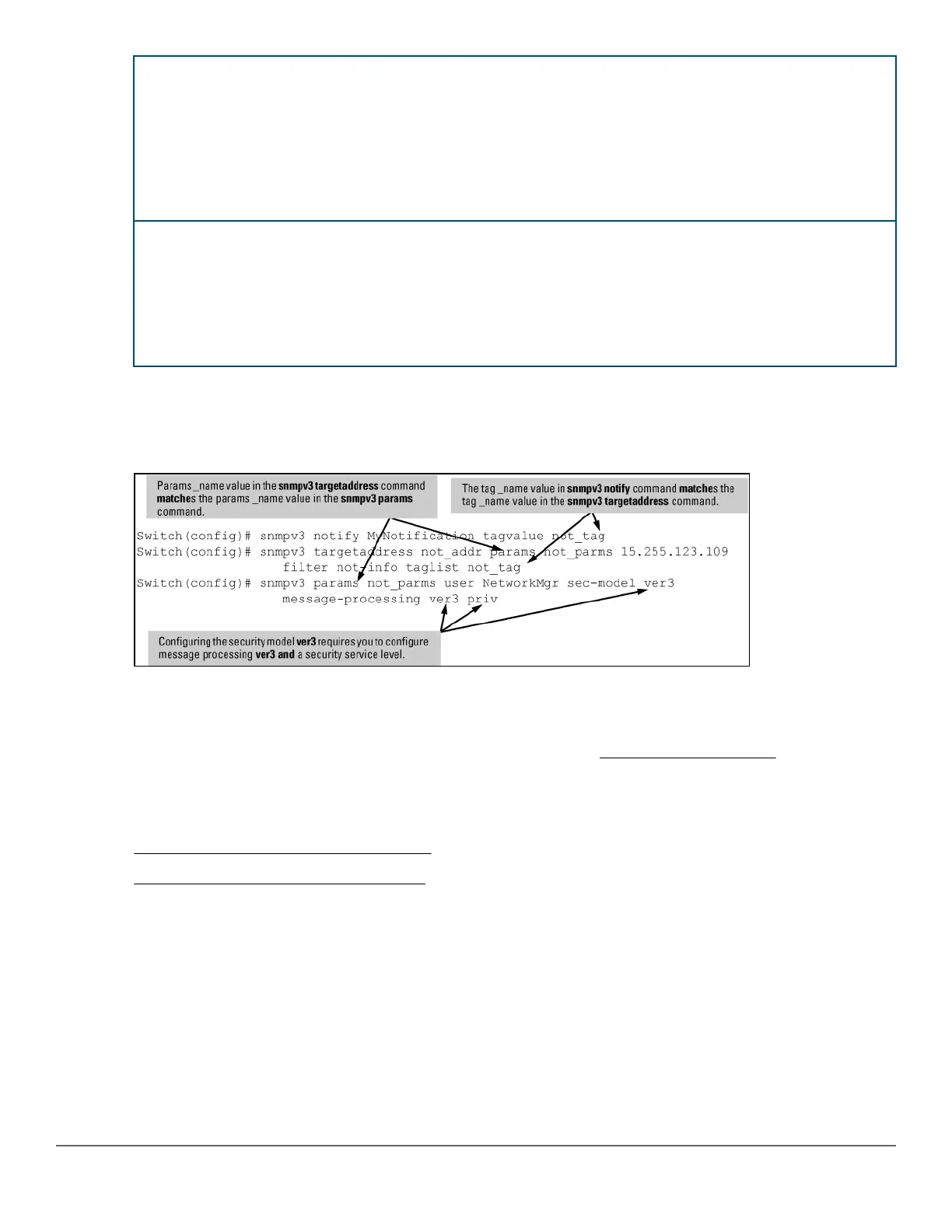
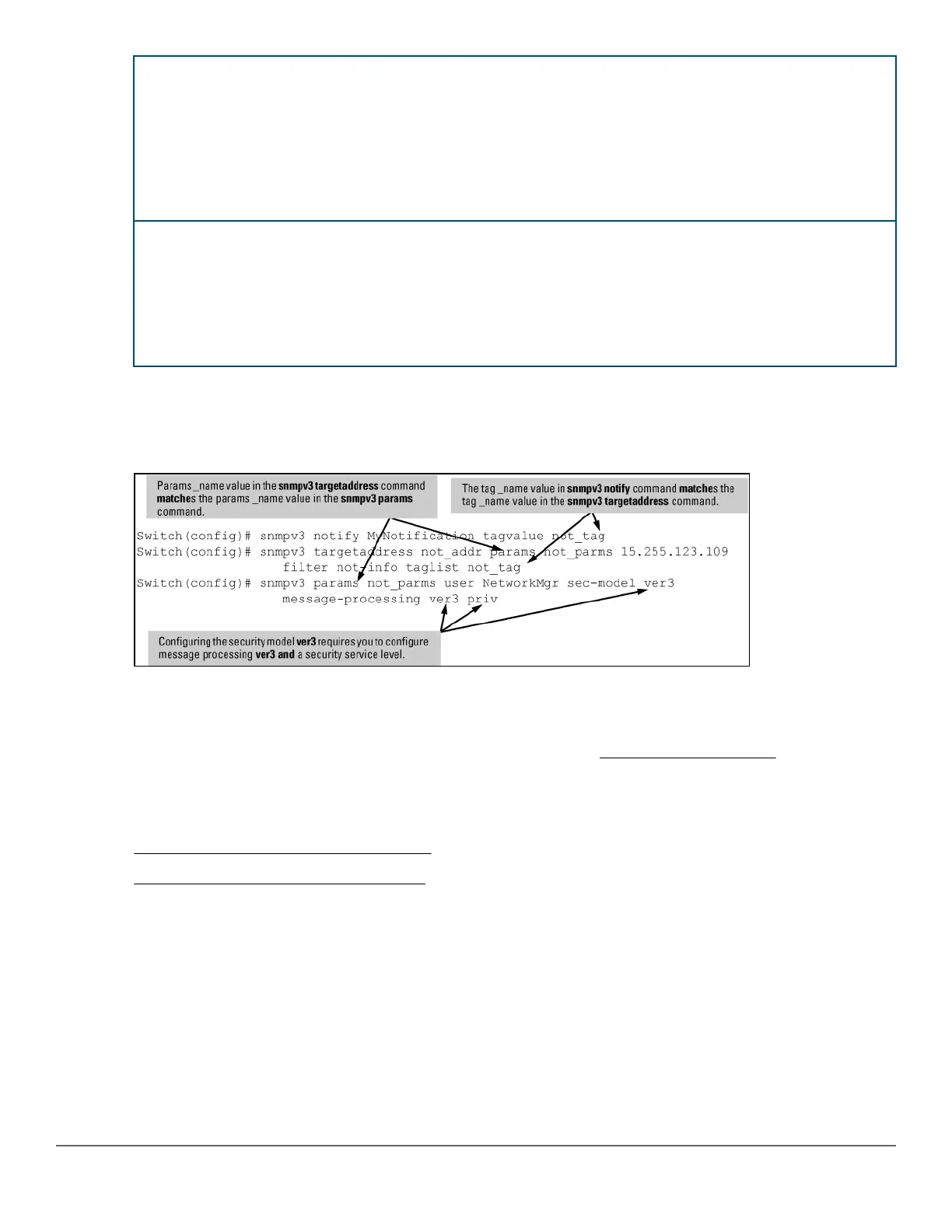
Example:
An Example: of how to configure SNMPv3 notification is shown here:
Figure 31: Example: of an SNMPv3 notification configuration
Network security notifications
By default, a switch is enabled to send the SNMP notifications listed in Supported Notifications on page 155
when a network security event (For example, authentication failure) occurs. However, before security notifications
can be sent, you must first configure one or more trap receivers or SNMPv3 management stations as described
in:
• Configuring an SNMP trap receiver (CLI) on page 156
• Configuring SNMPv3 notifications (CLI) on page 158
You can manage the default configuration of the switch to disable and re-enable notifications to be sent for the
following types of security events:
• ARP protection events
• Inability to establish a connection with the RADIUS or TACACS+ authentication server
• DHCP snooping events
• Dynamic IP Lockdown hardware resources consumed
• Link change notification
Chapter 8 Configuring for Network Management Applications 161
 Loading...
Loading...