Security | 501
You can assign line authentication on a per-VTY basis; it is a simple password authentication using an
access-class as authorization.
Local authentication is configured globally. You configure access classes on a per-user basis.
FTOS can assign different access classes to different users by username. Until users attempt to log in,
FTOS does not know if they will be assigned a VTY line. This means that incoming users always see a
login prompt even if you have excluded them from the VTY line with a
deny-all access class. After users
identify themselves, FTOS retrieves the access class from the local database and applies it. (FTOS also
subsequently can close the connection if a user is denied access.)
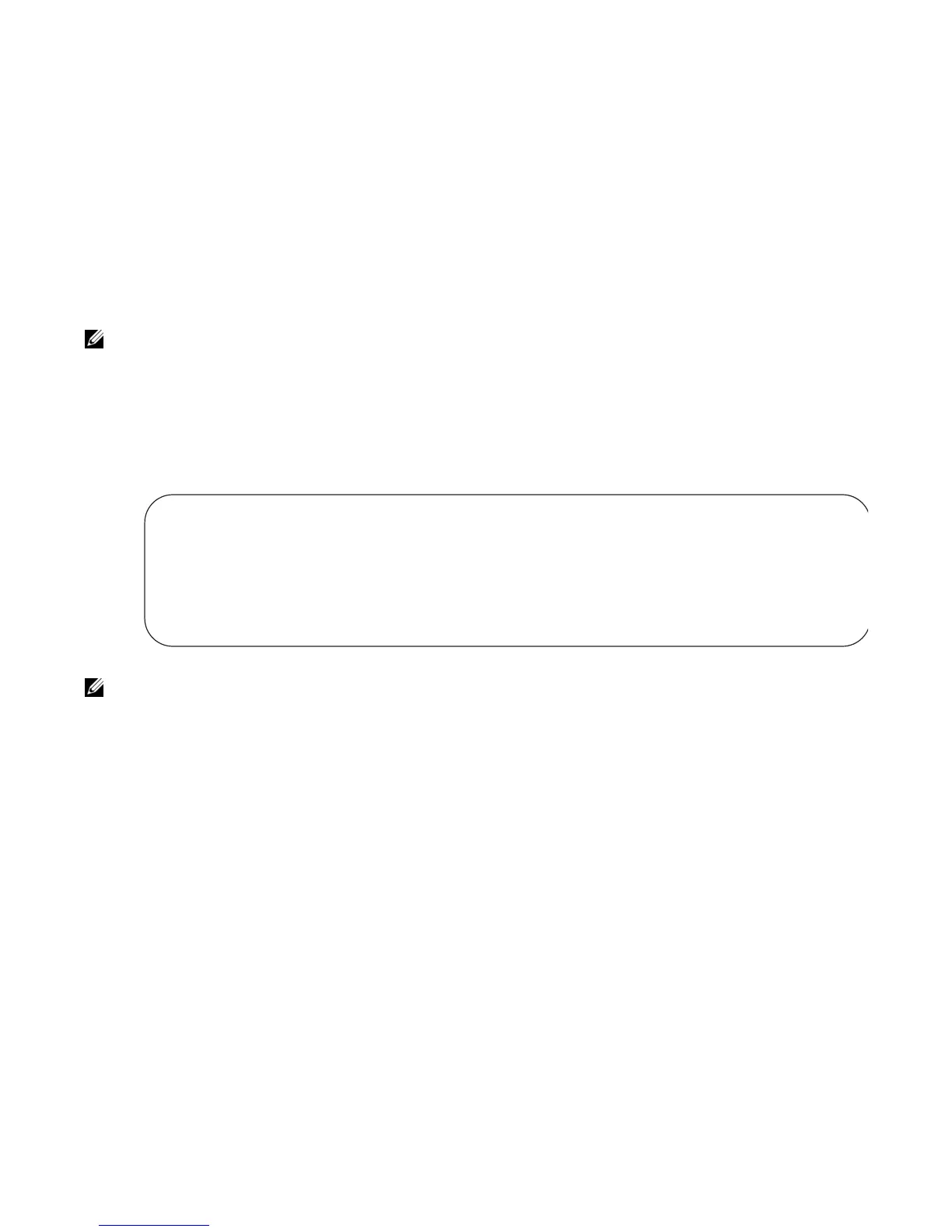
Figure 28-16 shows how to allow or deny a Telnet connection to a user. Users see a login prompt, even if
they cannot login. No access class is configured for the VTY line. It defaults from the local database.
Figure 28-16. Example Access-Class Configuration Using Local Database
VTY Line Remote Authentication and Authorization
FTOS takes the access class from the VTY line and applies it to ALL users. FTOS does not need to know
the identity of the incoming user and can immediately apply the access class. If the authentication method
is radius, TACACS+, or line, and you have configured an access class for the VTY line, FTOS
immediately applies it. If the access-class is
deny all or deny for the incoming subnet, FTOS closes the
connection without displaying the login prompt. Figure 28-17 shows how to deny incoming connections
from subnet 10.0.0.0 without displaying a login prompt. The example uses TACACS+ as the
authentication mechanism.
Note: If a VTY user logs in with RADIUS authentication, the privilege level is applied from the RADIUS
server only if you configure RADIUS authentication.
Note: For more information, refer to Access Control Lists (ACLs).
FTOS(conf)#user gooduser password abc privilege 10 access-class permitall
FTOS(conf)#user baduser password abc privilege 10 access-class denyall
FTOS(conf)#
FTOS(conf)#aaa authentication login localmethod local
FTOS(conf)#
FTOS(conf)#line vty 0 9
FTOS(conf-line-vty)#login authentication localmethod
FTOS(conf-line-vty)#end

 Loading...
Loading...