User Manual UMN:CLI
V8102
283
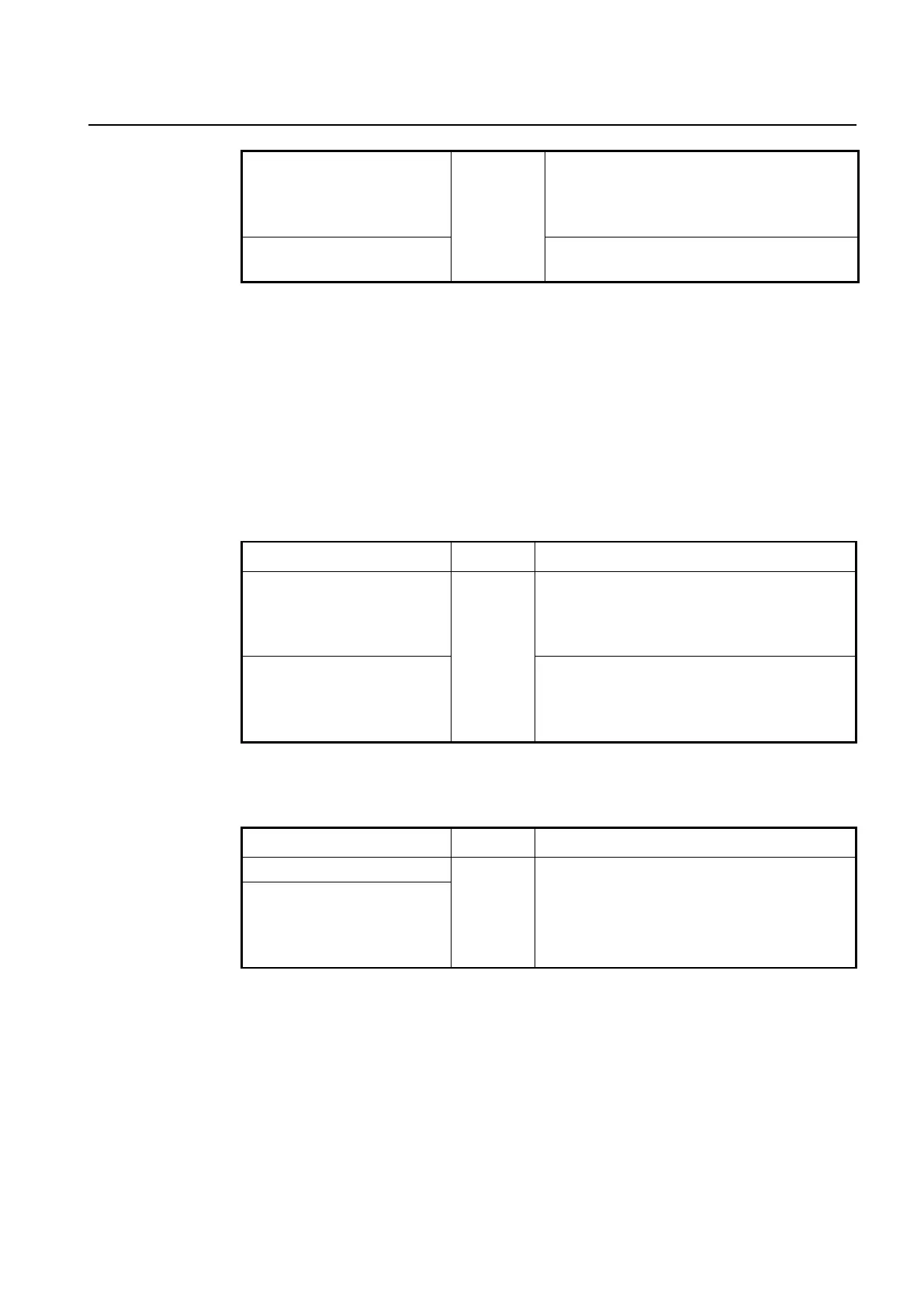
ipv6 nd retrans-time <0-
4294967295>
Interface
[VLAN/MGMT
/LO]
Specifies the interval between IPv6 neighbor solicita-
tion retransmissions.
0-4294967295: IPv6 NS retransmission time in milli-
seconds
Deletes a configured interval between IPv6 neighbor
solicitation retransmissions.
8.2.9 Static IPv6 Neighbor Entry
The Neighbor Discovery (ND) protocol is a new messaging protocol that was created as
part of IPv6 to perform a number of the tasks that ICMP and ARP accomplish in IPv4.
Just like ARP, ND builds a cache of dynamic entries, and the administrator can configure
the mapping between IPv6 address and MAC address to add static entries in the ND
cache table.
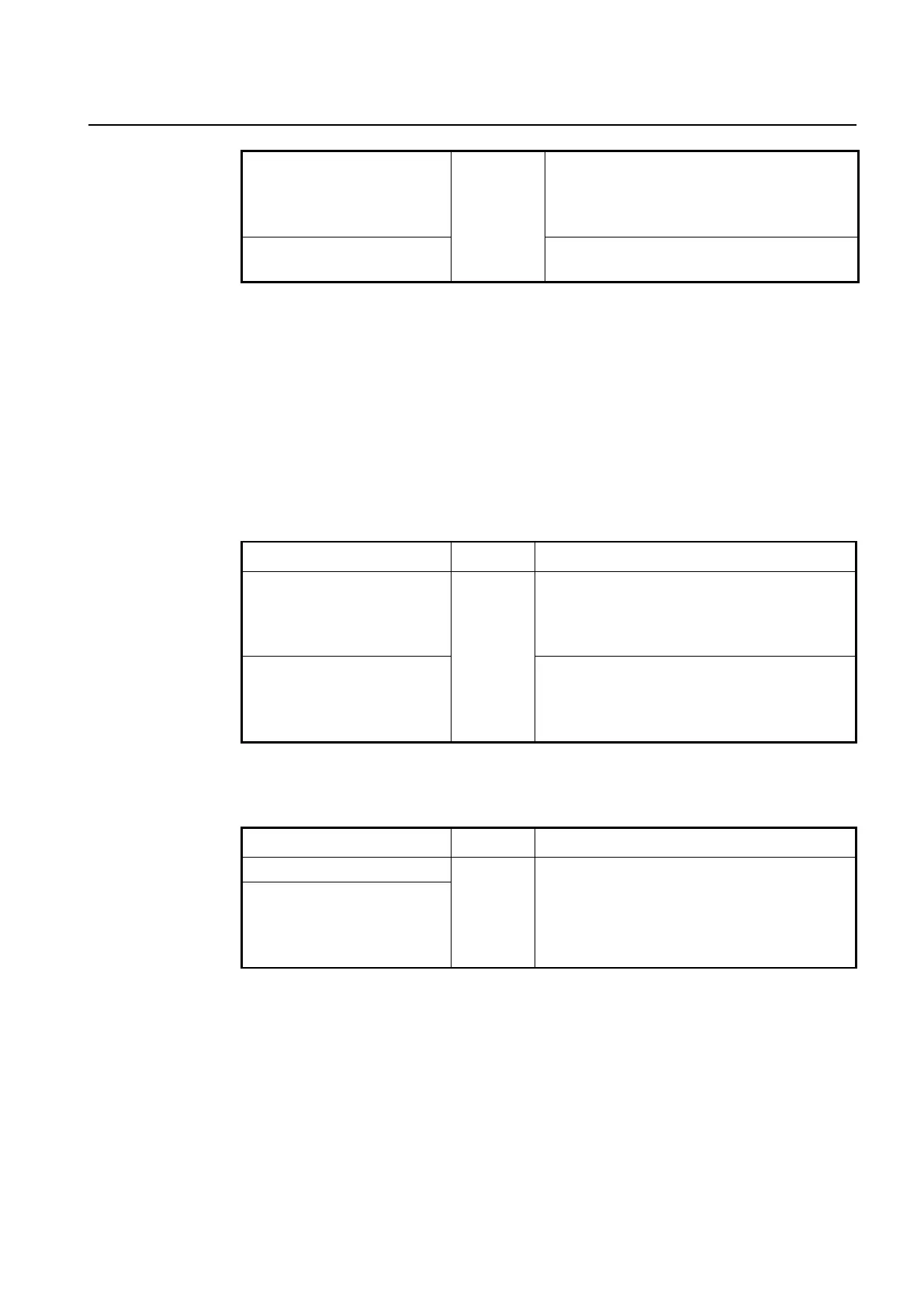
To add a static entry in the ND cache table by specifying the mapping between an IPv6
address and a MAC address, use the following command.
ipv6 neighbor X:X::X:X MAC-
ADDR
Sets a static neighbor entry, enter the IPv6 address
and the MAC address.
X:X::X:X: IPv6 address
MACADDR: enter the MAC address.
ipv6 neighbor X:X::X:X MAC-
ADDR { gigabitethernet | tengi-
gabitethernet | gpon | chan-
nelgroup} IFPORT
Sets a static neighbor entry, enter the IPv6 address,
MAC address and interface name.
MACADDR: enter the MAC address.
To remove the configured static entry from the ND cache table, use the following com-
mand.
no ipv6 neighbor [X:X::X:X]
Remove the configured static entry from the ND cache
table
no ipv6 neighbor X:X::X:X
{gigabitethernet | tengiga-
bitethernet | gpon | chan-
nelgroup} IFPORT
8.2.10 IPv6 Neighbor Discovery (ND) Inspection
IPv6 Neighbor Discovery (ND) inspection feature can protect switches against IPv6 ad-
dress spoofing. It provides IPv6 communication by mapping an IPv6 address to a MAC
address. However, a malicious user can attack ND caches of system by intercepting the
traffic intended for other hosts on the subnet. ND inspection is a security feature that vali-
dates ND packets in a network. It discards ND packets with invalid IP-MAC address bind-
ing.

 Loading...
Loading...