CHAPTER 11: Using Virtual Private Networks (VPN)
300 Vcontroller
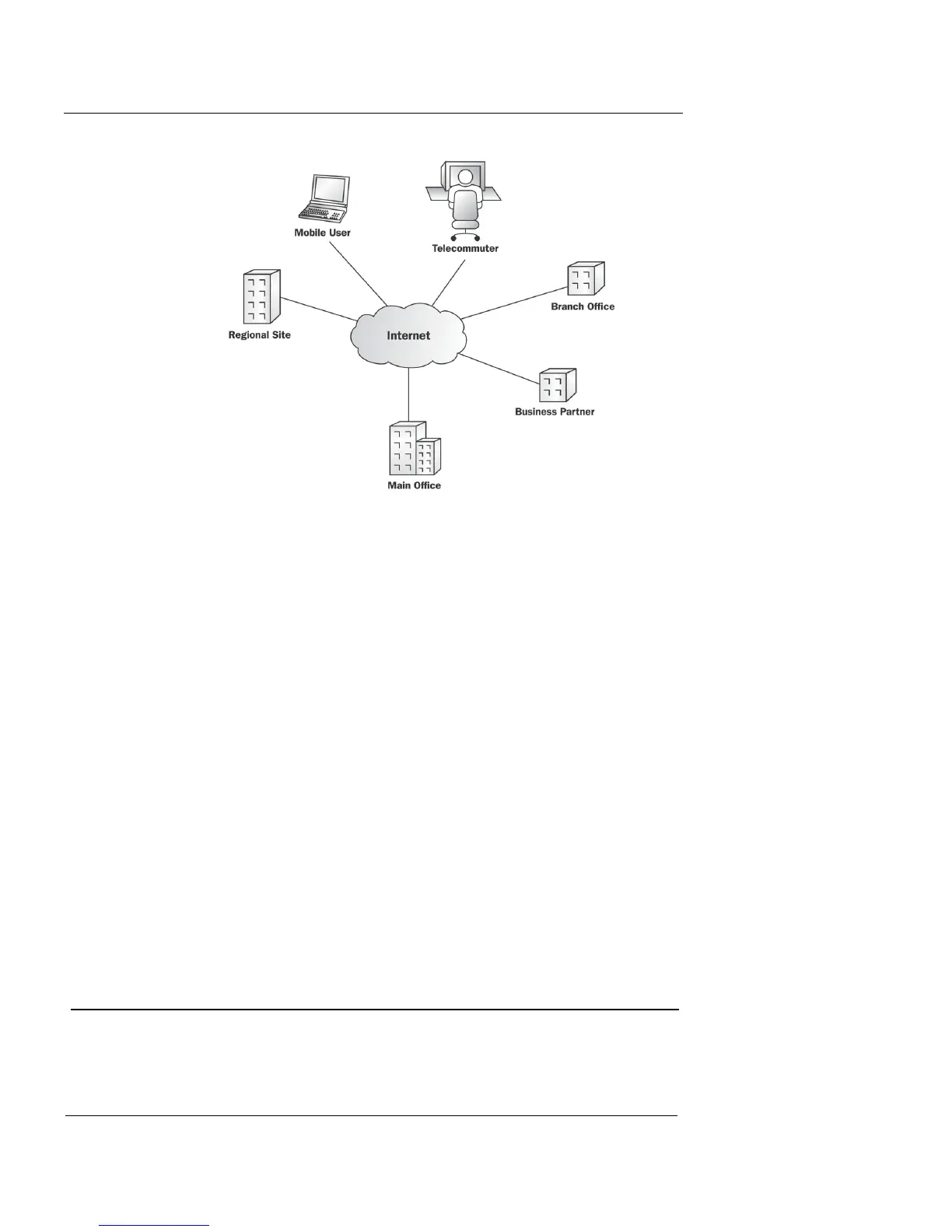
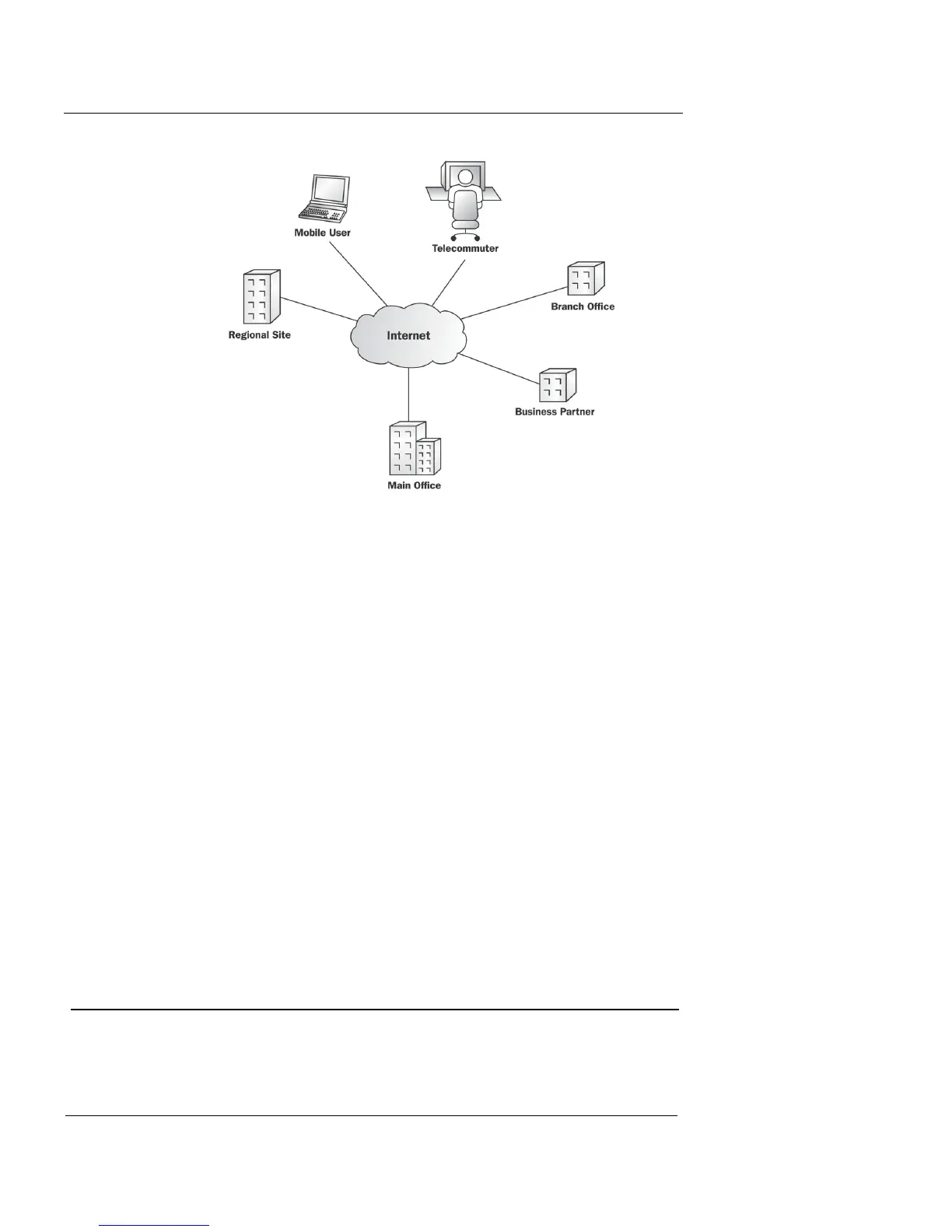
Virtual private networking technology counters this threat
by using the Internet’s vast capabilities while reducing its
security risk. A virtual private network (VPN) allows com-
munication to flow across the Internet between two net-
works or between a host and a network in a secure manner.
The networks and hosts at the endpoints of a VPN are typ-
ically corporate headquarters, branch offices, remote users,
telecommuters, and traveling employees. User authentica-
tion verifies the identity of both the sender and the
receiver. Data sent by way of the Internet is encrypted so
that only the sender and the receiver of the message can see
it in a clearly readable state.
For more information on VPN technology, see the online
support resources at http://support.watchguard.com. The
main page contains links to basic FAQs, advanced FAQs,
and the WatchGuard User’s Forum.
Tunneling Protocols
Tunneling—the foundation of VPN implementations—is the
transmission of private data through a public network,
 Loading...
Loading...