45-7
Software Configuration Guide—Release IOS XE 3.6.0E and IOS 15.2(2)E
OL_28731-01
Chapter 45 Configuring MACsec Encryption
Configuring MACsec and MACsec Key Agreement
• Replay protect is YES with a window size of 1000. If the frame received has a packet number (PN)
of 1020, for example, all frames with a PN of 20 to 1020 can come out of order (i.e, frame with PN
900 can come first and frame with PN 800 can come later). However, if a frame with a PN of 1021
is received first, followed by a frame with a PN of 20, the frame with PN of 20 is dropped. In this
scenario, the expected PN is 1022 and the window size is 1000, so the acceptable PN number is
anything greater than or equal to (expected PN - window size) = 22. So, any frame with PN < 22 is
dropped.
To apply the MKA protocol default policy on an interface, use the mka default-policy interface
configuration command. This command also enables MKA on the interface if no MKAs were applied.
When we configure the MKA default policy, all the values in the policy (such as confidentiality, offset,
and replay protection) take the default values. For example,
• Confidentiality offset is 0—Encrypts the payload that is immediately after the SA (source MAC
address).
• Replay protect is YES with window size 0—Frames cannot come out of order.
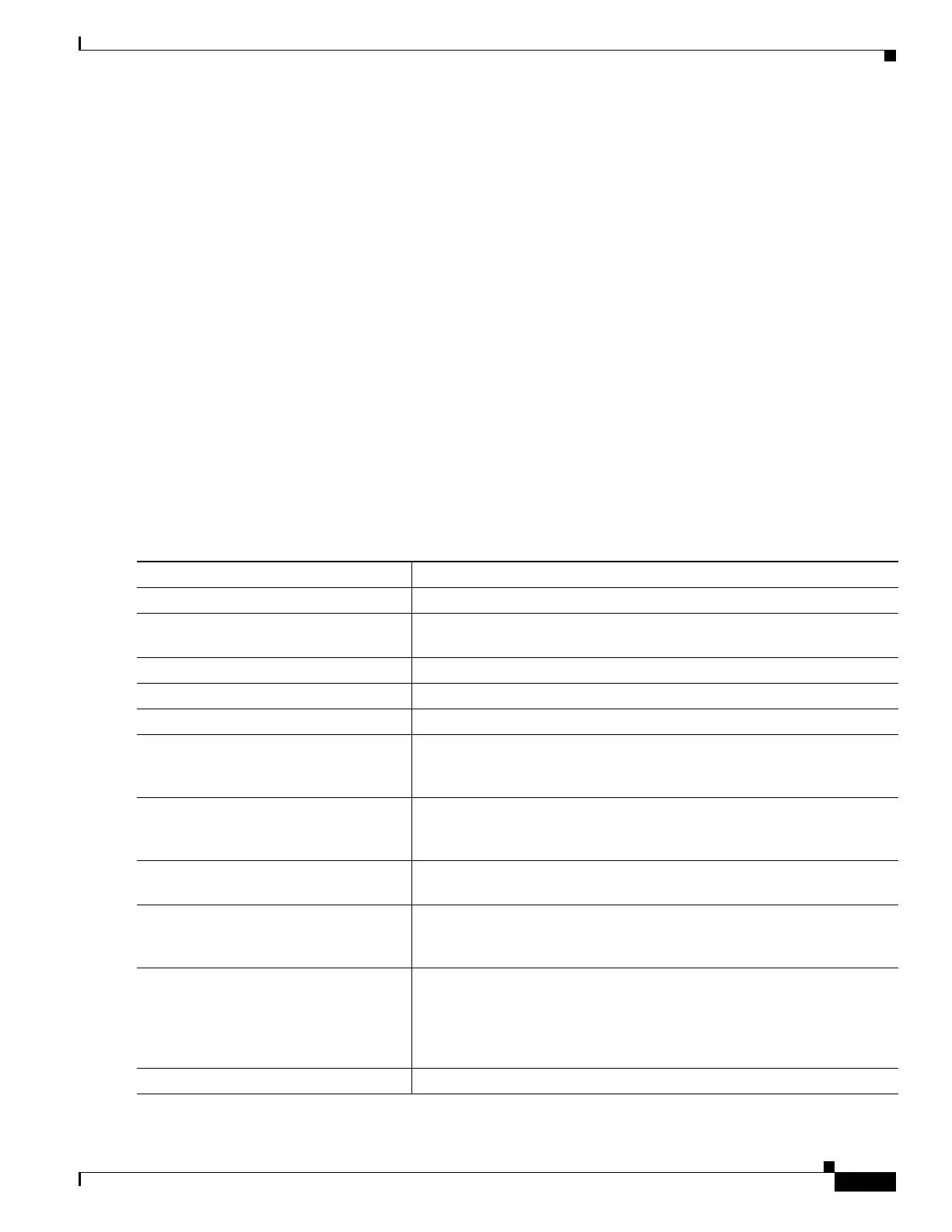
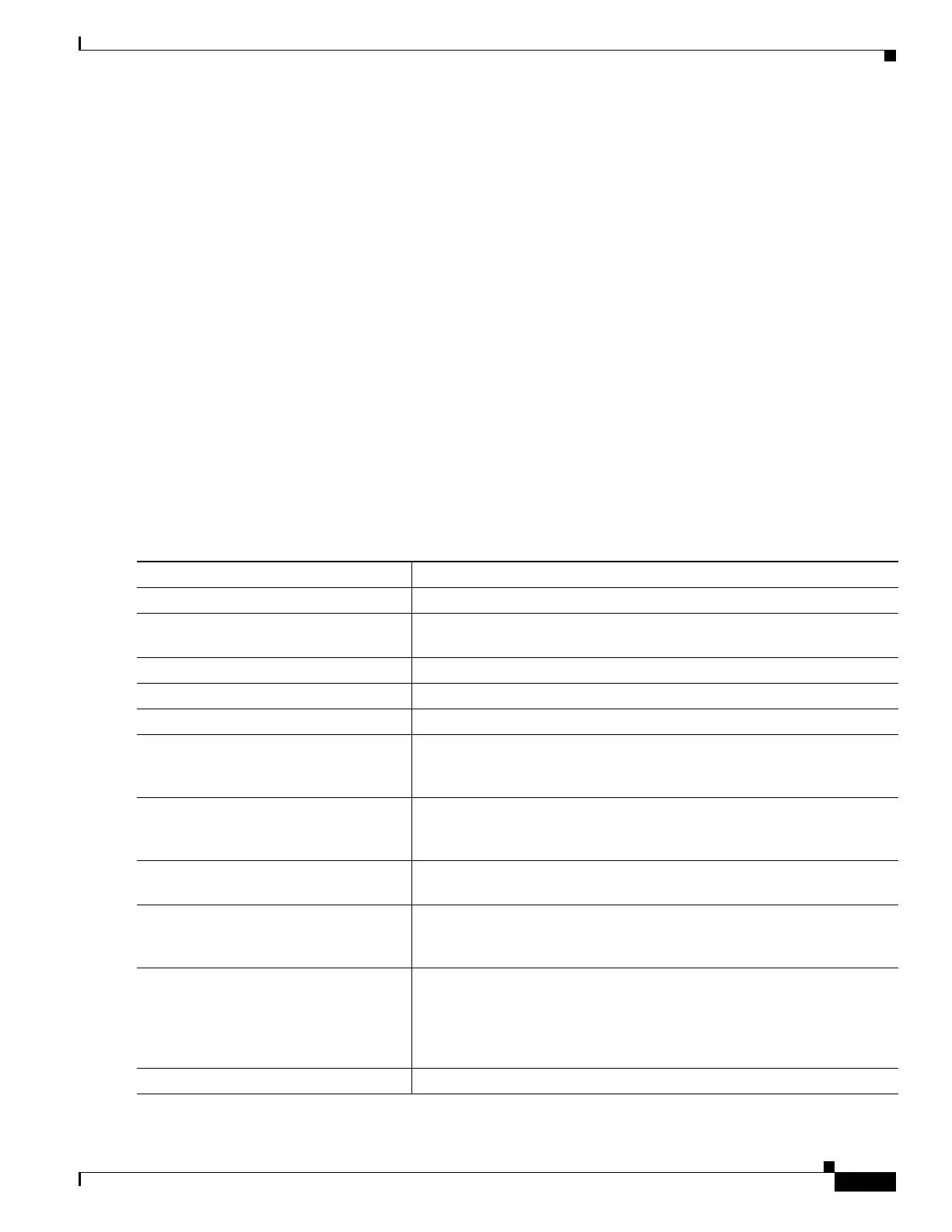
Configuring MACsec on an Interface
To configure MACsec on an interface with one MACsec session for voice and one for data, perform this
task:
Command Purpose
Step 1
configure terminal
Enters global configuration mode.
Step 2
interface interface-id
Identifies the MACsec interface, and enter interface configuration mode.
The interface must be a physical interface.
Step 3
switchport access vlan vlan-id
Configures the access VLAN for the port.
Step 4
switchport mode access
Configures the interface as an access port.
Step 5
macsec
Enables 802.1ae MACsec on the interface.
Step 6
authentication event linksec fail
action authorize vlan vlan-id
(Optional) Specifies that the switch processes authentication link-security
failures resulting from unrecognized user credentials by authorizing a
restricted VLAN on the port after a failed authentication attempt.
Step 7
authentication host-mode
multi-domain
Configures authentication manager mode on the port to allow both a host
and a voice device to be authenticated on the 802.1X-authorized port. If
not configured, the default host mode is single.
Step 8
authentication linksec policy
must-secure
Sets the LinkSec security policy to secure the session with MACsec if the
peer is available. If not set, the default is should secure.
Step 9
authentication port-control auto
Enables 802.1X authentication on the port. The port changes to the
authorized or unauthorized state based on the authentication exchange
between the switch and the client
Step 10
mka policy policy-name
Applies an existing MKA protocol policy to the interface, and enable
MKA on the interface. If no MKA policy was configured (by entering the
mka policy global configuration command), you must apply the MKA
default policy to the interface by entering the mka default-policy
interface configuration command.
Step 11
dot1x pae authenticator
Configures the port as an 802.1X port access entity (PAE) authenticator.

 Loading...
Loading...