U
SER
A
UTHENTICATION
C
OMMANDS
22-34
Port Security Commands
These commands can be used to enable port security on a port. When
using port security, the switch stops learning new MAC addresses on the
specified port when it has reached a configured maximum number. Only
incoming traffic with source addresses already stored in the dynamic or
static address table for this port will be authorized to access the network.
The port will drop any incoming frames with a source MAC address that is
unknown or has been previously learned from another port. If a device
with an unauthorized MAC address attempts to use the switch port, the
intrusion will be detected and the switch can automatically take action by
disabling the port and sending a trap message.
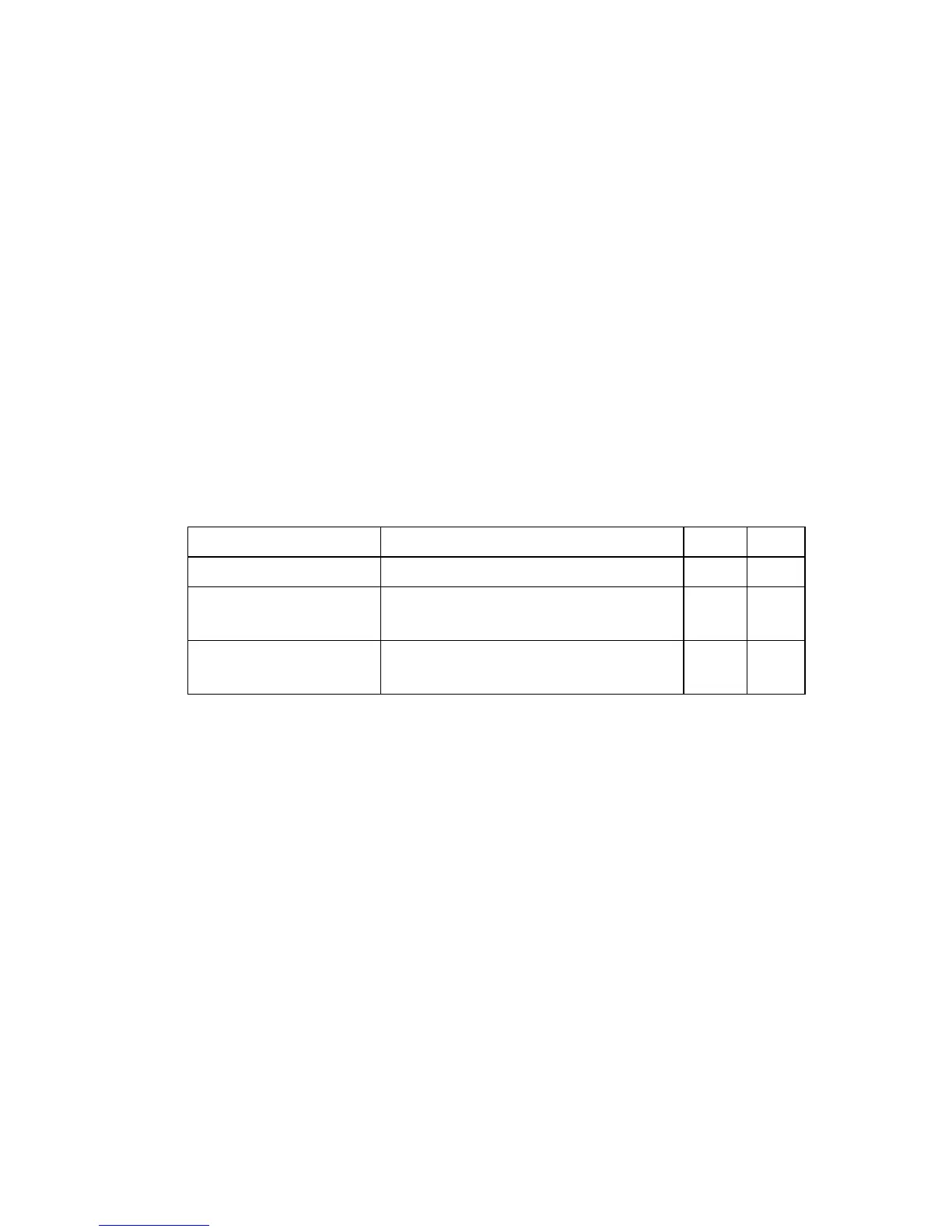
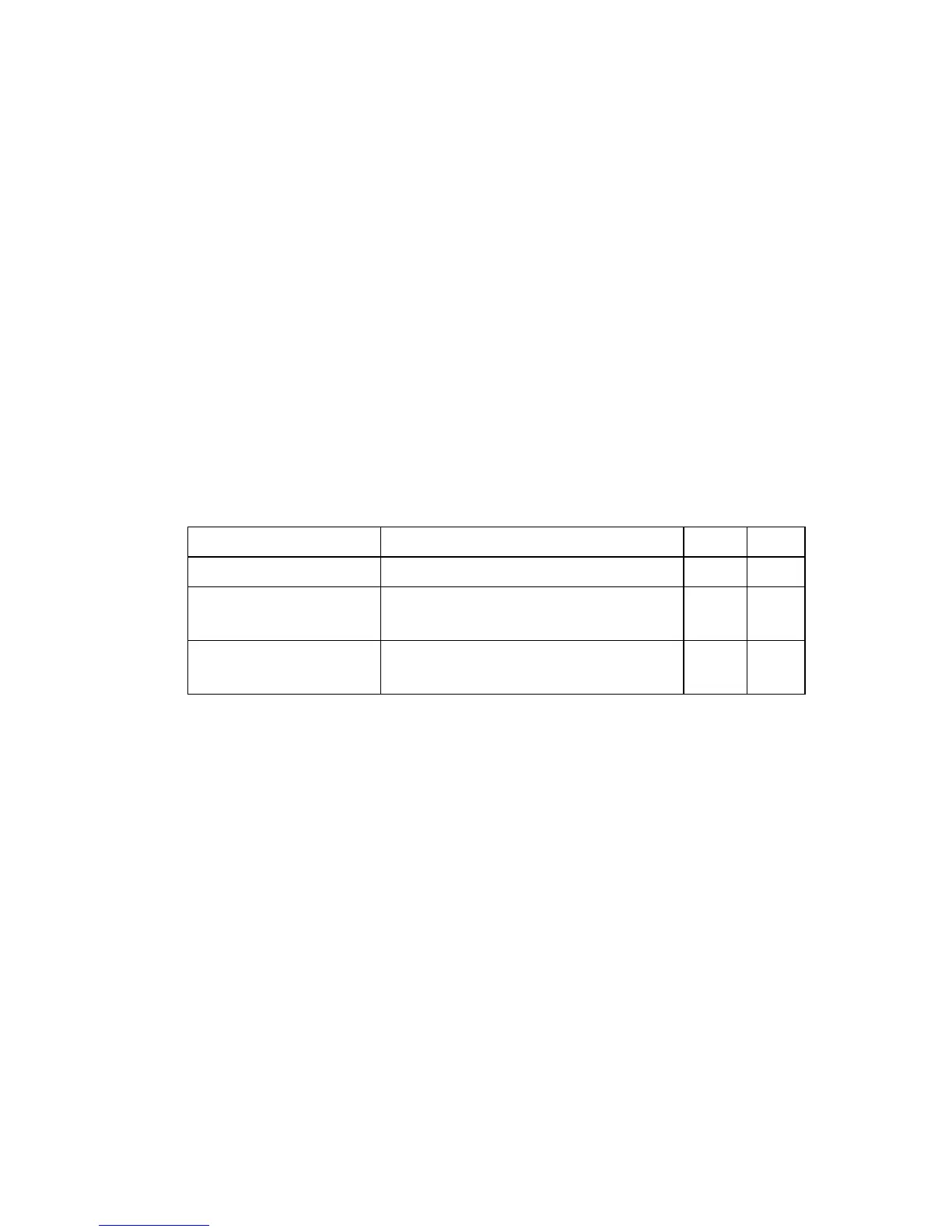
Table 22-12 Port Security Commands
Command Function Mode Page
port security Configures a secure port IC 22-35
mac-address-table static Maps a static address to a port in a
VLAN
GC 28-2
show mac-address-table Displays entries in the
bridge-forwarding database
PE 28-4

 Loading...
Loading...