C
ONFIGURING
THE
S
WITCH
3-86
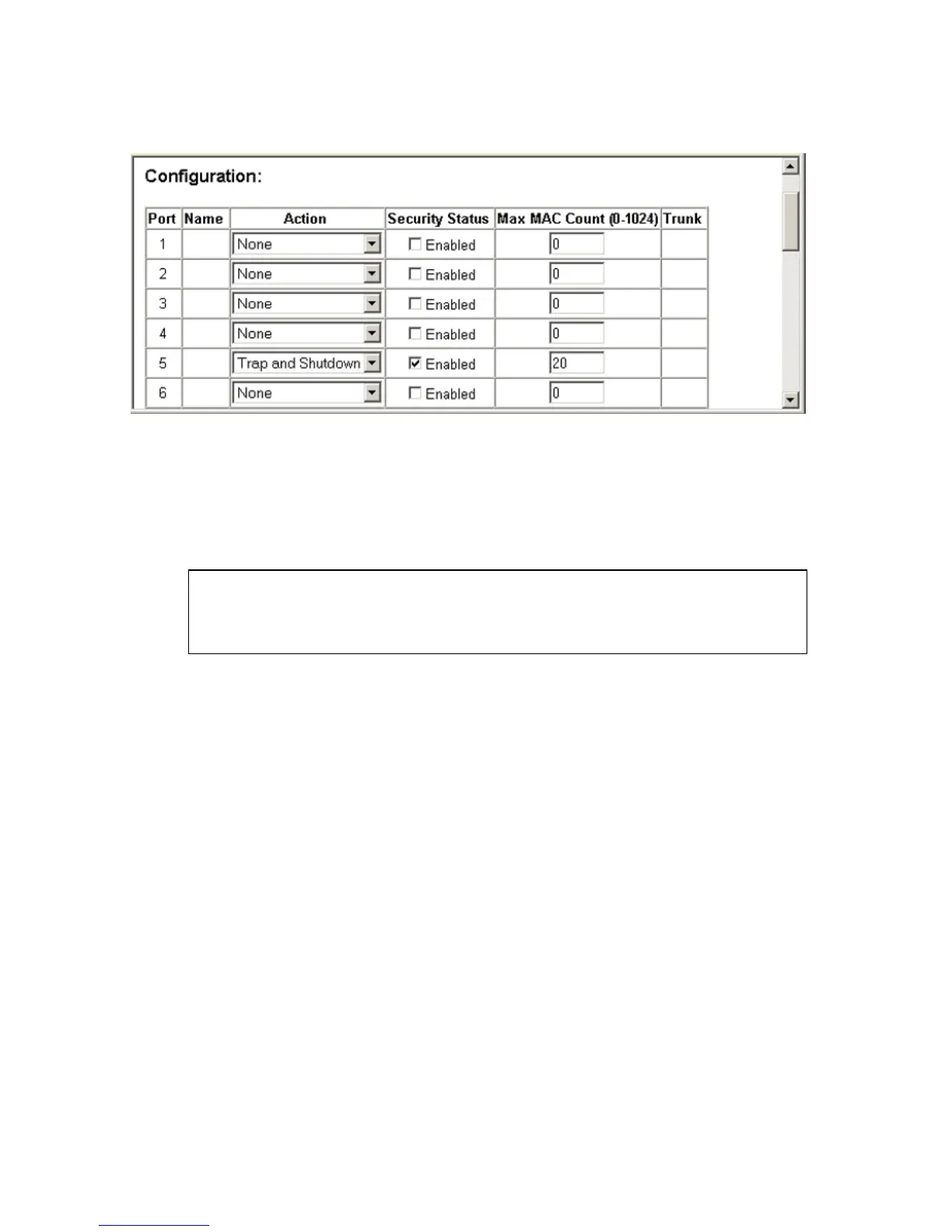
Figure 3-37. Configuring Port Security
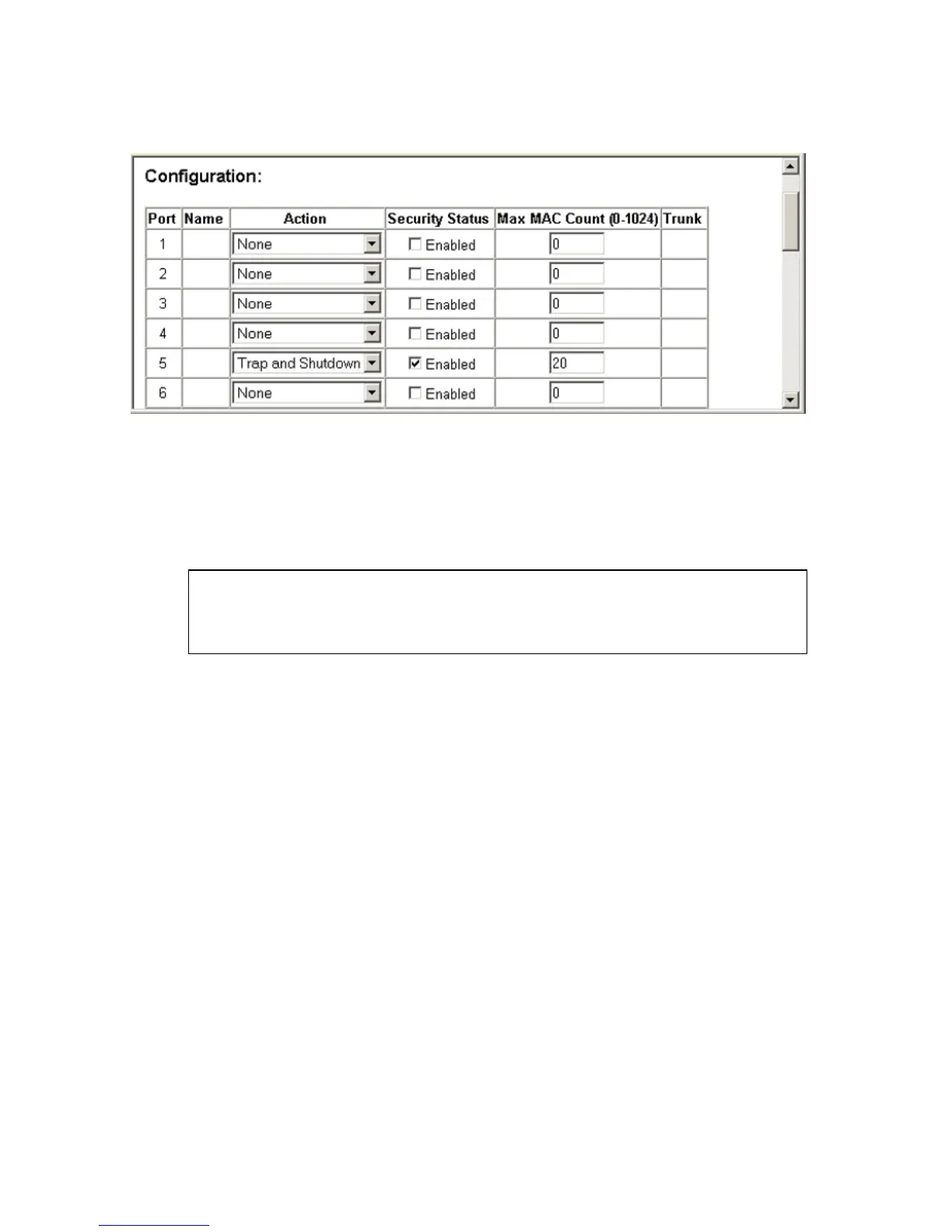
CLI – This example selects the target port, sets the port security action to
send a trap and disable the port and sets the maximum MAC addresses
allowed on the port, and then enables port security for the port.
Configuring 802.1X Port Authentication
Network switches can provide open and easy access to network resources
by simply attaching a client PC. Although this automatic configuration and
access is a desirable feature, it also allows unauthorized personnel to easily
intrude and possibly gain access to sensitive network data.
The IEEE 802.1X (dot1X) standard defines a port-based access control
procedure that prevents unauthorized access to a network by requiring
users to first submit credentials for authentication. Access to all switch
ports in a network can be centrally controlled from a server, which means
that authorized users can use the same credentials for authentication from
any point within the network.
Console(config)#interface ethernet 1/5
Console(config-if)#port security action trap-and-shutdown 4-108
Console(config-if)#port security max-mac-count 20 4-108
Console(config-if)#port security 4-108
Console(config-if)#

 Loading...
Loading...