Operation Manual – SSH
H3C S3100 Series Ethernet Switches Chapter 1 SSH Configuration
1-3
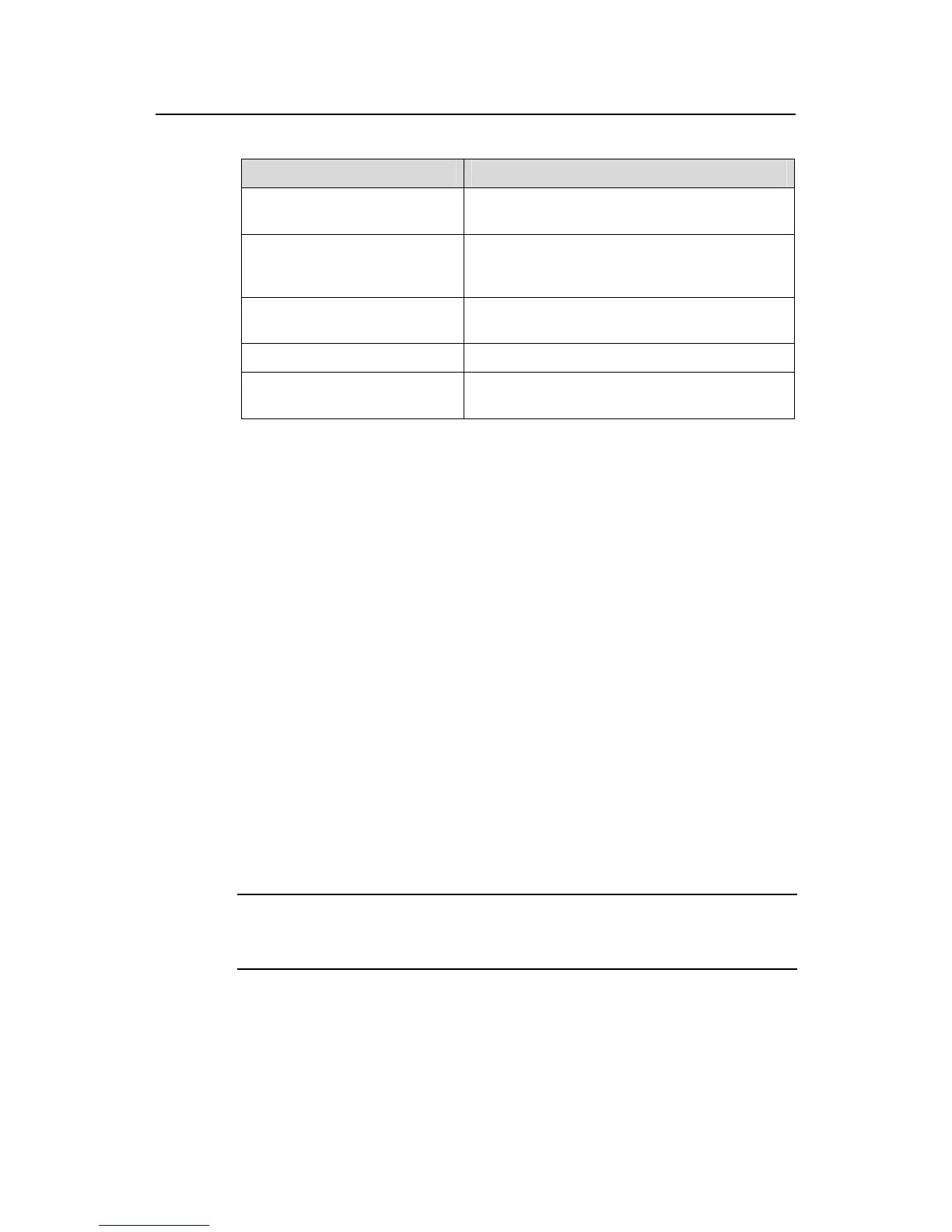
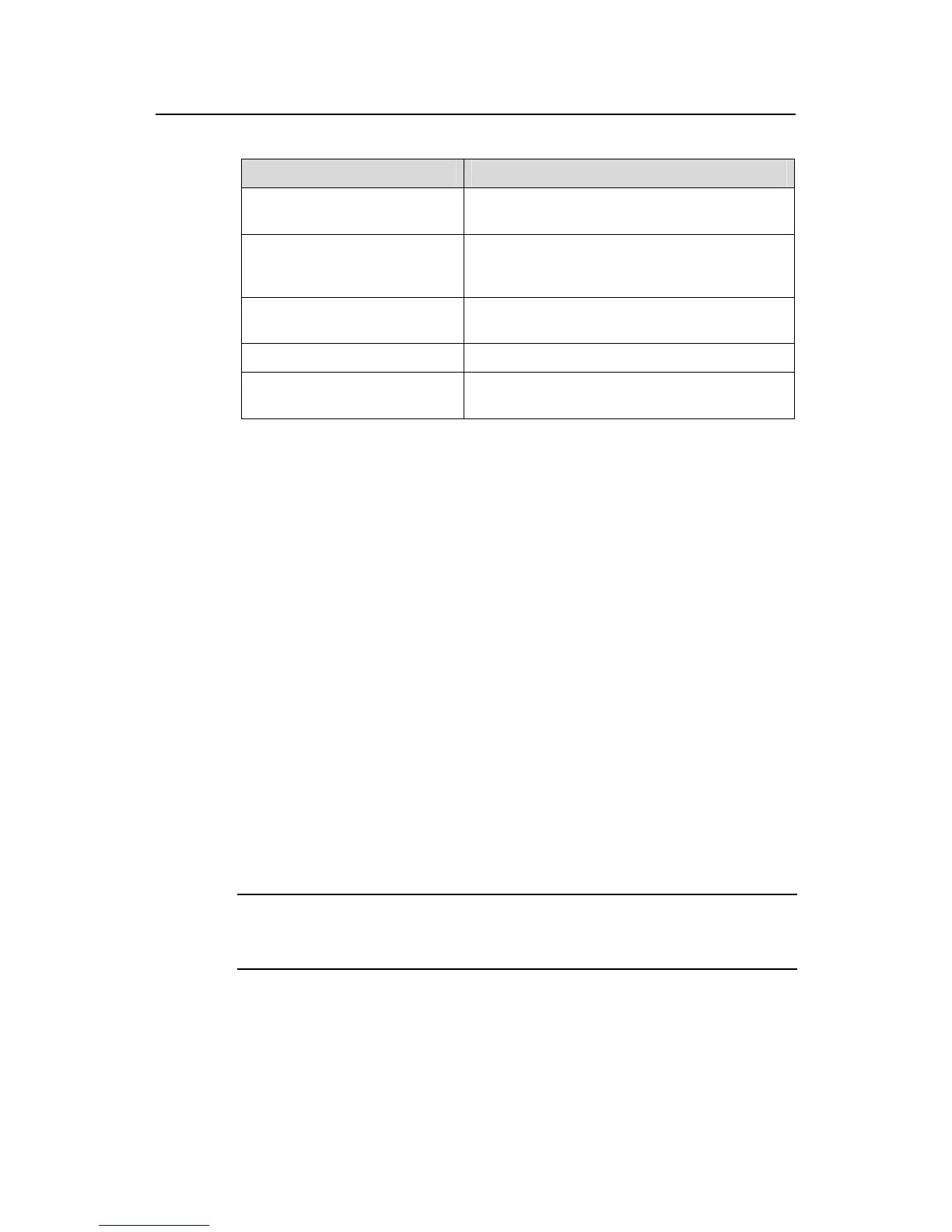
Table 1-1 Stages in establishing a session between the SSH client and server
Stages Description
Version negotiation
SSH1 and SSH2 are supported. The two parties
negotiate a version to use.
Key and algorithm negotiation
SSH supports multiple algorithms. The two
parties negotiate an algorithm for
communication.
Authentication
The SSH server authenticates the client in
response to the client’s authentication request.
Session request This client sends a session request to the server.
Data exchange
The client and the server start to communicate
with each other.
I. Version negotiation
z The server opens port 22 to listen to connection requests from clients.
z The client sends a TCP connection request to the server. After the TCP
connection is established, the server sends the first packet to the client, which
includes a version identification string in the format of “SSH-<primary protocol
version number>.<secondary protocol version number>-<software version
number>”. The primary and secondary protocol version numbers constitute the
protocol version number, while the software version number is used for
debugging.
z The client receives and resolves the packet. If the protocol version of the server is
lower but supportable, the client uses the protocol version of the server; otherwise,
the client uses its own protocol version.
z The client sends to the server a packet that contains the number of the protocol
version it decides to use. The server compares the version carried in the packet
with that of its own to determine whether it can cooperate with the client.
z If the negotiation is successful, the server and the client go on to the key and
algorithm negotiation. If not, the server breaks the TCP connection.
Note:
All the packets above are transferred in plain text.
II. Key negotiation
z The server and the client send algorithm negotiation packets to each other, which
contain public key algorithm lists supported by the server and the client, encrypted

 Loading...
Loading...