User Manual UMN:CLI
V5808
223
request from client net through the concentrating switch.
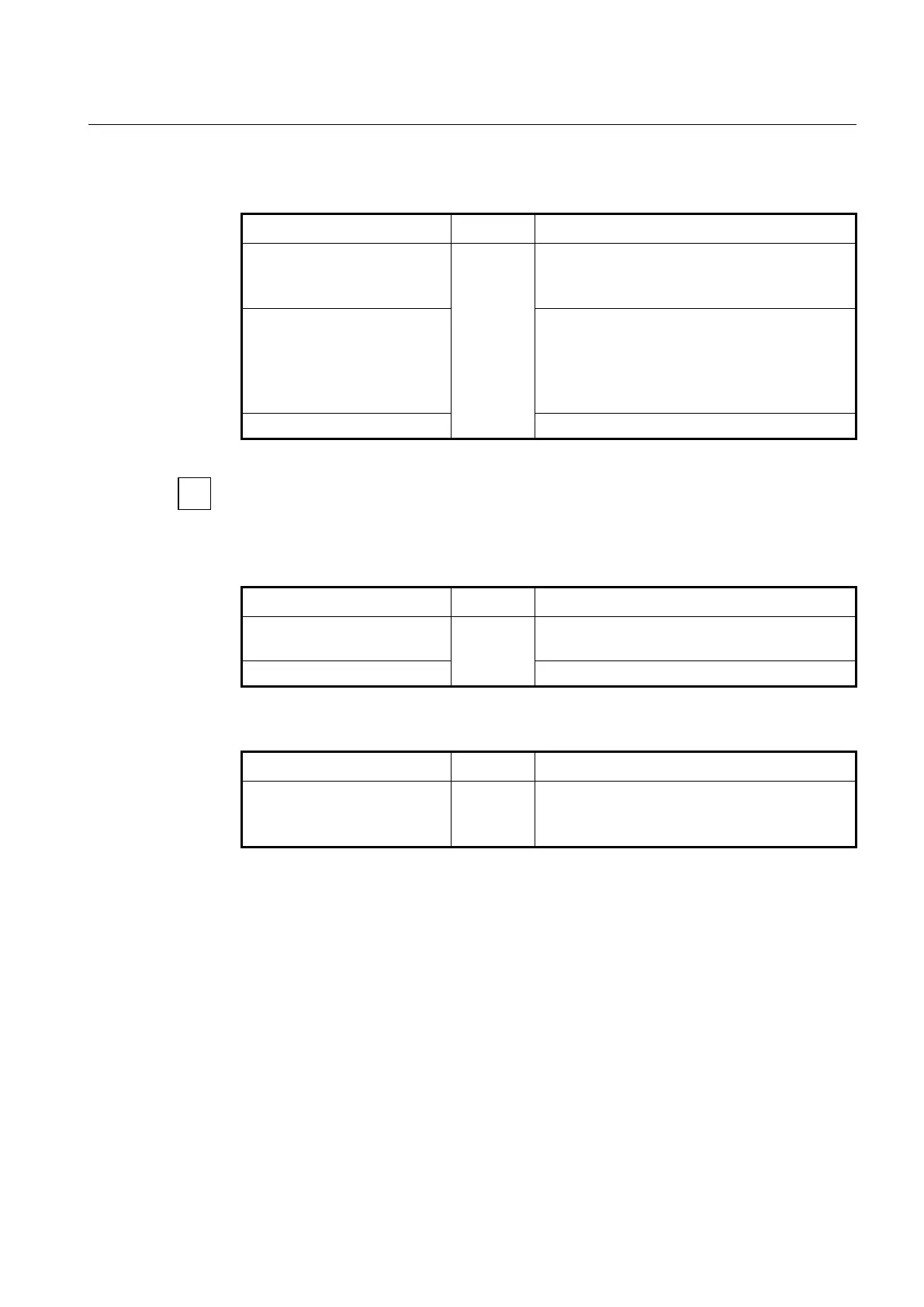
To register the address of client net range in ARP alias, use the following command.
arp alias A.B.C.D A.B.C.D
[XX:XX:XX:XX:XX:XX]
Registers the IP address range and MAC address in
ARP alias to make the system response to an ARP
request.
arp alias A.B.C.D A.B.C.D vlan
VLAN gateway GATEWAY
Registers gateway IP address within IP address range
to make the system response automatically MAC
address of gateway.
VLAN: 1-4094
GATEWAY: gateway IP address
no arp alias A.B.C.D A.B.C.D
Deletes the registered IP address range of ARP alias.
Unless you input a MAC address, the MAC address of user’s device will be used for ARP
response.
To set aging time of gateway IP address in ARP alias, use the following command.
arp alias aging-time
<5-2147483647>
Sets the aging time of gateway IP address.
5-2147483647: aging time (default: 300 seconds)
Deletes the aging time of gateway IP address.
To display a registered ARP alias, use the following command.
Shows a registered ARP alias.
7.15.4 ARP Inspection
ARP provides IP communication by mapping an IP address to a MAC address. However,
a malicious user can attack ARP caches of systems by intercepting the traffic intended for
other hosts on the subnet. For example, Host B generates a broadcast message for all
hosts within the broadcast domain to obtain the MAC address associated with the IP
address of Host A. If Host C responses with an IP address of Host A (or B) and a MAC
address of Host C, Host A and Host B can use Host C’s MAC address as the destination
MAC address for traffic intended for Host A and Host B.
ARP Inspection is a security feature that validates ARP packets in a network. It discards
ARP packets with invalid IP-MAC address binding.
 Loading...
Loading...