49-3
Catalyst 4500 Series Switch, Cisco IOS Software Configuration Guide - Cisco IOS XE 3.9.xE and IOS 15.2(5)Ex
Chapter 49 Configuring 802.1X Port-Based Authentication
About 802.1X Port-Based Authentication
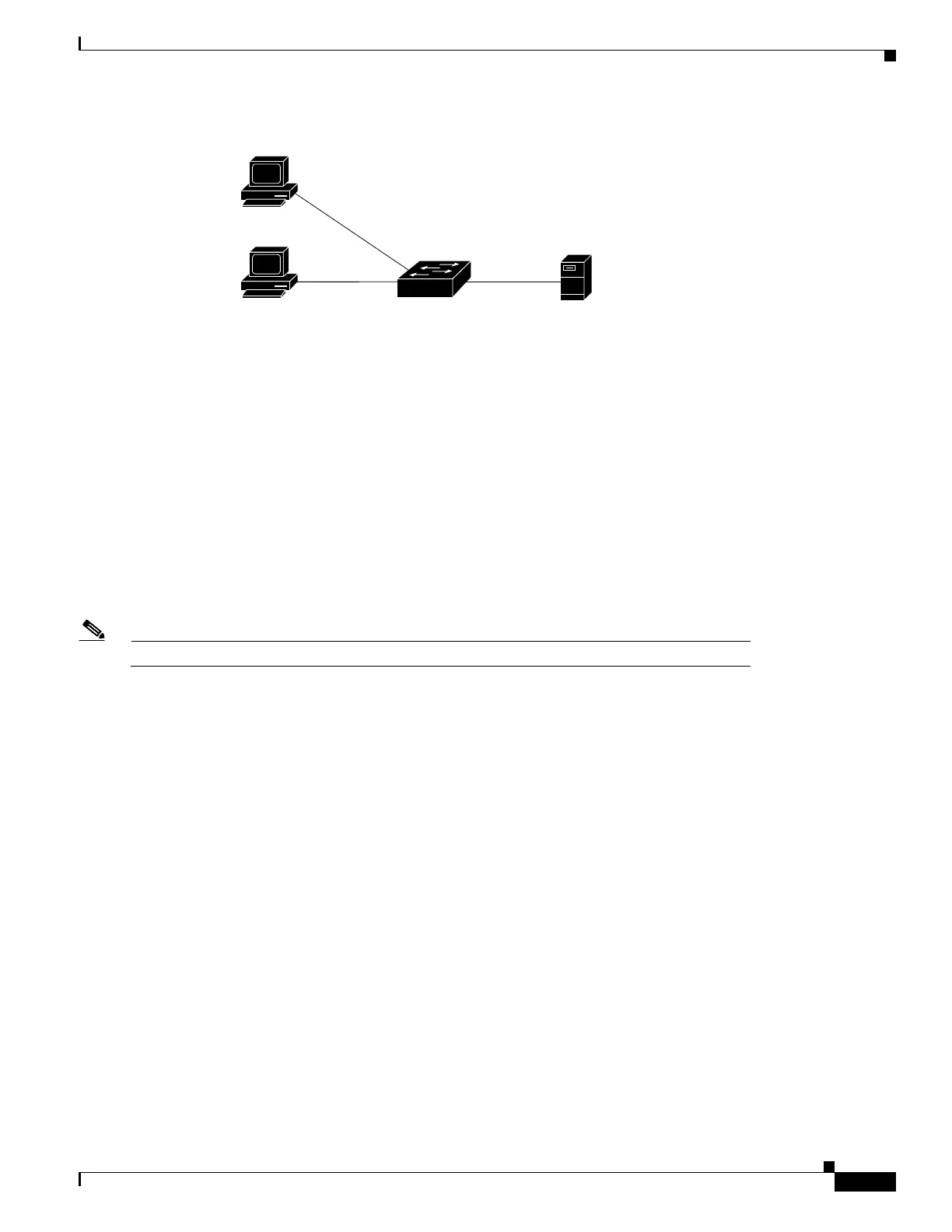
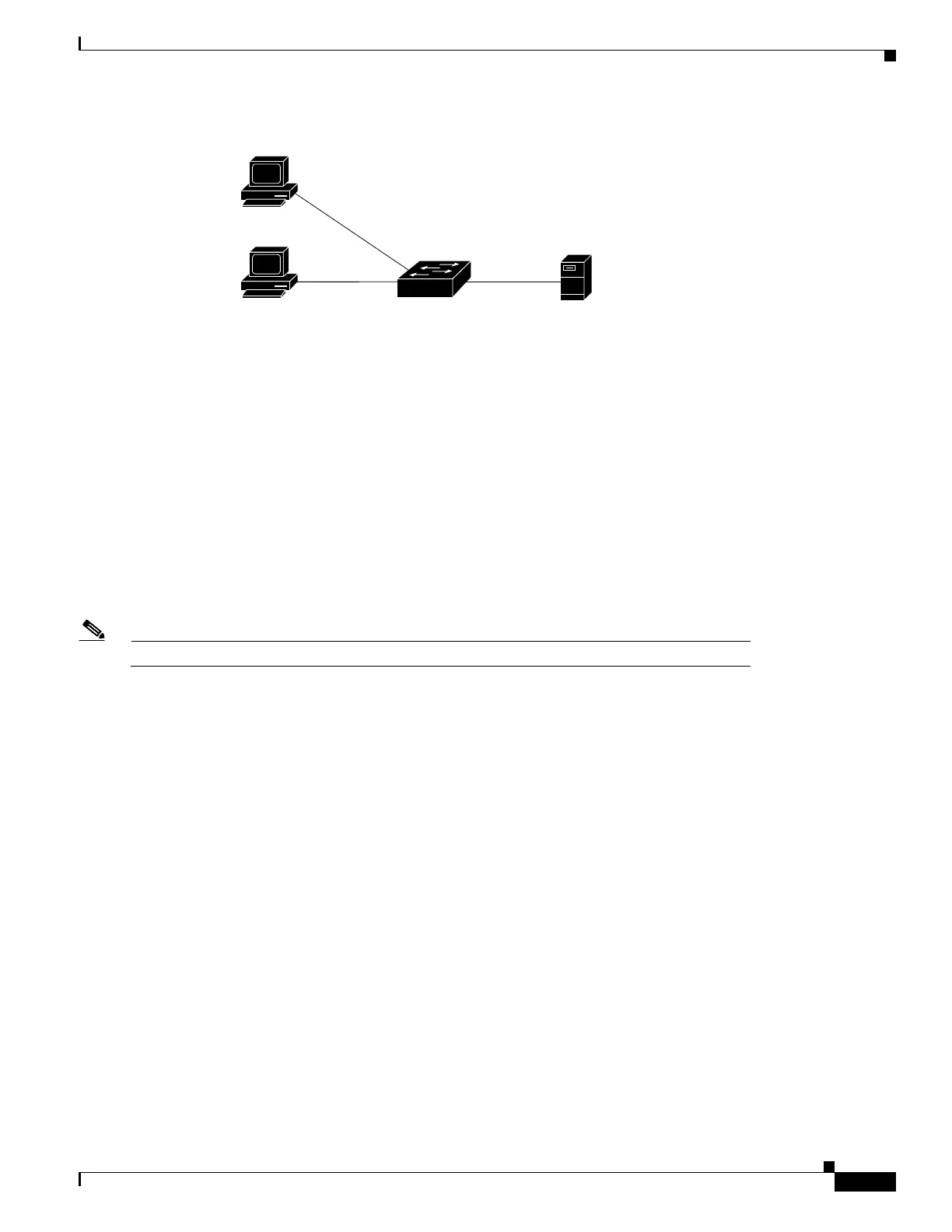
Figure 49-1 802.1X Device Roles
•
Client—The workstation that requests access to the LAN, and responds to requests from the switch. The workstation must
be running 802.1X-compliant client software.
• Authenticator—Controls physical access to the network based on the authentication status of the client. The Catalyst 4500
series switch acts as an intermediary between the client and the authentication server, requesting identity information from
the client, verifying that information with the authentication server, and relaying a response to the client. The switch
encapsulates and decapsulates the Extensible Authentication Protocol (EAP) frames and interacts with the RADIUS
authentication server.
When the switch receives EAPOL frames and relays them to the authentication server, the Ethernet header is stripped and
the remaining EAP frame is reencapsulated in the RADIUS format. The EAP frames are not modified or examined during
encapsulation, and the authentication server must support EAP within the native frame format. When the switch receives
frames from the authentication server, the frame header is removed from the server, leaving the EAP frame, which is then
encapsulated for Ethernet and sent to the client.
Note The Catalyst 4500 series switches must be running software that supports the RADIUS client and 802.1X.
• Authentication server—Performs the actual authentication of the client. The authentication server validates the identity of
the client and notifies the switch that the client is authorized to access the LAN and switch services. (The only supported
authentication server is the RADIUS authentication server with EAP extensions; it is available in Cisco Secure Access
Control Server version 3.2 and later releases.)
802.1X and Network Access Control
Network Access Control is a feature that allows port access policies to be influenced by the antivirus posture of the
authenticating device.
Antivirus posture includes such elements as the operating system running on the device, the operating system version, whether
antivirus software is installed and what version of antivirus signatures is available. If the authenticating device has a
NAC-aware 802.1X supplicant and the authentication server is configured to support NAC using 802.1X, antivirus posture
information is automatically included as part of the 802.1X authentication exchange.
For information on NAC, refer to the URL:
http://www.cisco.com/en/US/products/ps6128/index.html
Client
Workstations
Supplicants
Authenticator
Authentication
server
94158
Catalyst 4500 Network
Access Switch
RADIUS

 Loading...
Loading...