49-56
Catalyst 4500 Series Switch, Cisco IOS Software Configuration Guide - Cisco IOS XE 3.9.xE and IOS 15.2(5)Ex
Chapter 49 Configuring 802.1X Port-Based Authentication
Configuring 802.1X Port-Based Authentication
The following syslog messages displays when MAC-move happens:
%AUTHMGR-5-SECUREMACMOVE: <mac-addr> moved from <interface-name> to <interface-name>
Configuring MAC Replace
MAC replace allows new users to connect to abandoned ports.
If a user disconnects but the switch has not received the EAPoL-Logoff, the session will remain up. For single or multiple-
domain modes, no new hosts can connect to that port. If a new host tries to connect, a violation is triggered on the port. Where
the violation action is configured as replace, the desired behavior is for the NAD (switch) to terminate the initial session and
reset the authentication sequence based on the new MAC.
To enable MAC replace on a switch, perform this task:
This example shows how to globally enable MAC replace on a switch:
Switch# configure terminal
Switch(config)# interface f7/1
Switch(config-if)# authentication violation replace
The following syslog messages displays when MAC-replace occurs:
%AUTHMGR-5-SECUREMACREPLACE: <mac-addr> replaced <mac-addr> on <interface-name>
Configuring Violation Action
You can configure 802.1X security violation behavior as either shutdown, restrict, or replace mode, based on the response to
the violation.
To configure the violation action, performing the following task:
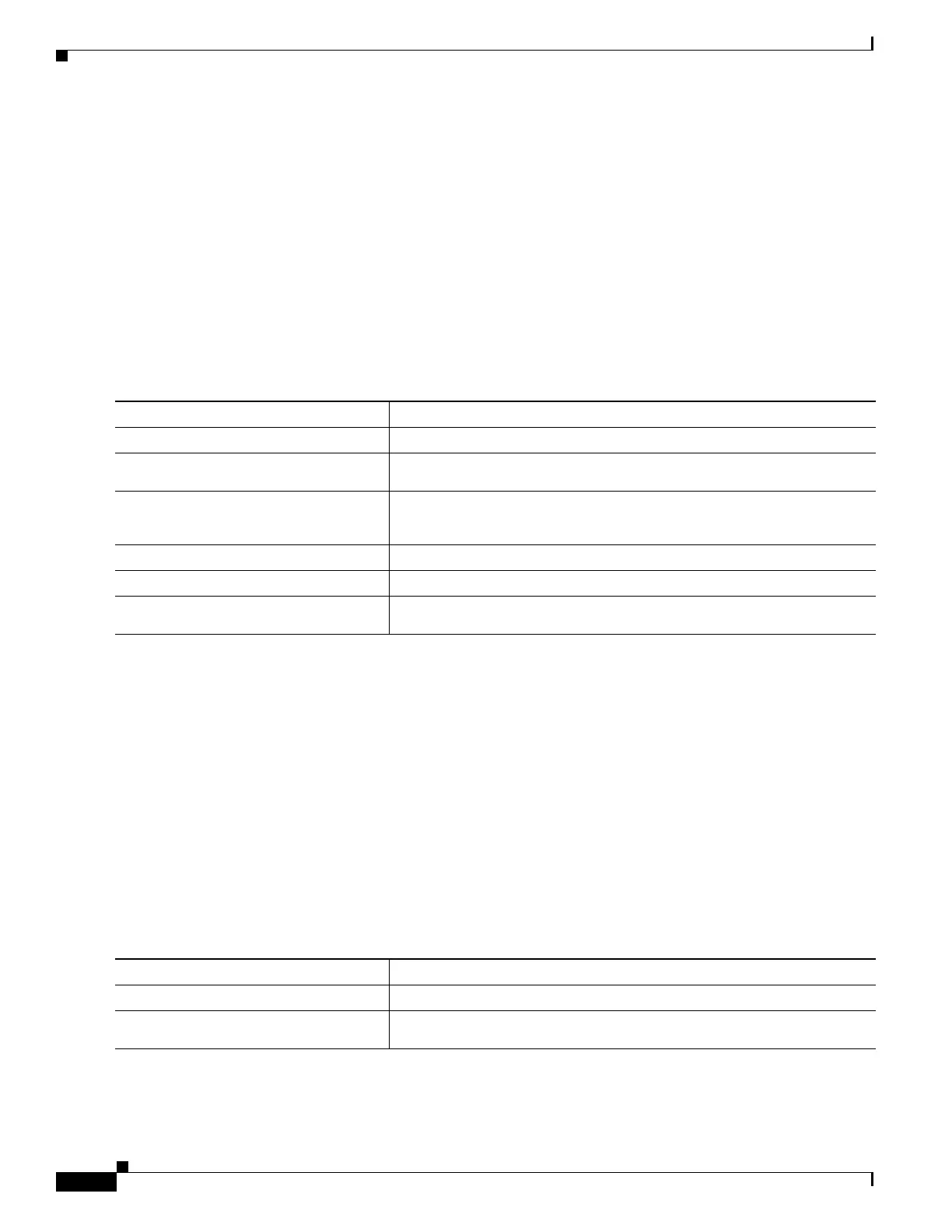
Command Purpose
Step 1
Switch# configure terminal
Enters global configuration mode.
Step 2
Switch(config)# interface
interface-id
Enters interface configuration mode.
Step 3
Switch(config-if)# authentication
violation [restrict | shutdown |
replace]
Tears down the old session and authenticates the new host, when a new
host is seen in single or multiple- domain modes.
Step 4
Switch(config-if)# end
Returns to privileged EXEC mode.
Step 5
Switch# show run
Verifies your entries.
Step 6
Switch # copy running-config
startup-config
(Optional) Saves your entries in the configuration file.
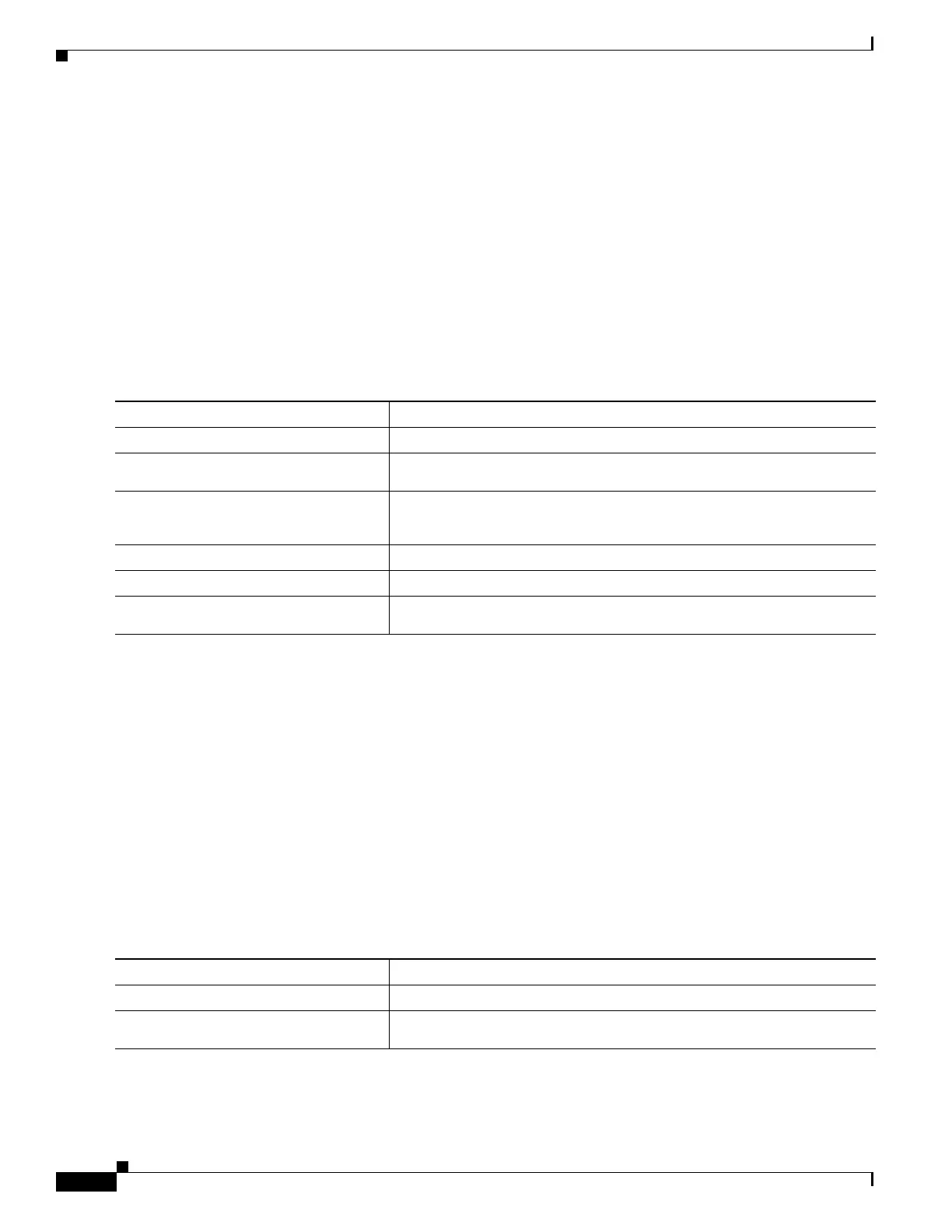
Command Purpose
Step 1
Switch# configure terminal
Enters global configuration mode.
Step 2
Switch(config)# interface
interface-id
Enters interface configuration mode.

 Loading...
Loading...