AES Functional Description
www.ti.com
616
SWRU543–January 2019
Submit Documentation Feedback
Copyright © 2019, Texas Instruments Incorporated
Advance Encryption Standard Accelerator (AES)
• Mixing the data within each column of the state array: This transformation operates on the state
column-by-column, treating each column as a 4-term polynomial. The columns are considered
polynomials over GF(2
8
) and multiplied modulo x
4
+ 1 with a fixed polynomial a(x).
• Adding a round key to the state: In this transformation, a round key is added to the state by a simple
bitwise XOR operation. Each round key consists of Nb words from the key schedule.
The AES algorithm takes the cipher key (K) and performs a key expansion routine to generate a key
schedule. The key expansion generates a total of Nb × (Nr + 1) words: The algorithm requires an initial set
of Nb words, and each Nr round requires Nb words of key data. The resulting key schedule consists of a
linear array of 4-byte words, denoted [w
i
], with i in the range 0 ≤ i ≤ Nb × (Nr + 1).
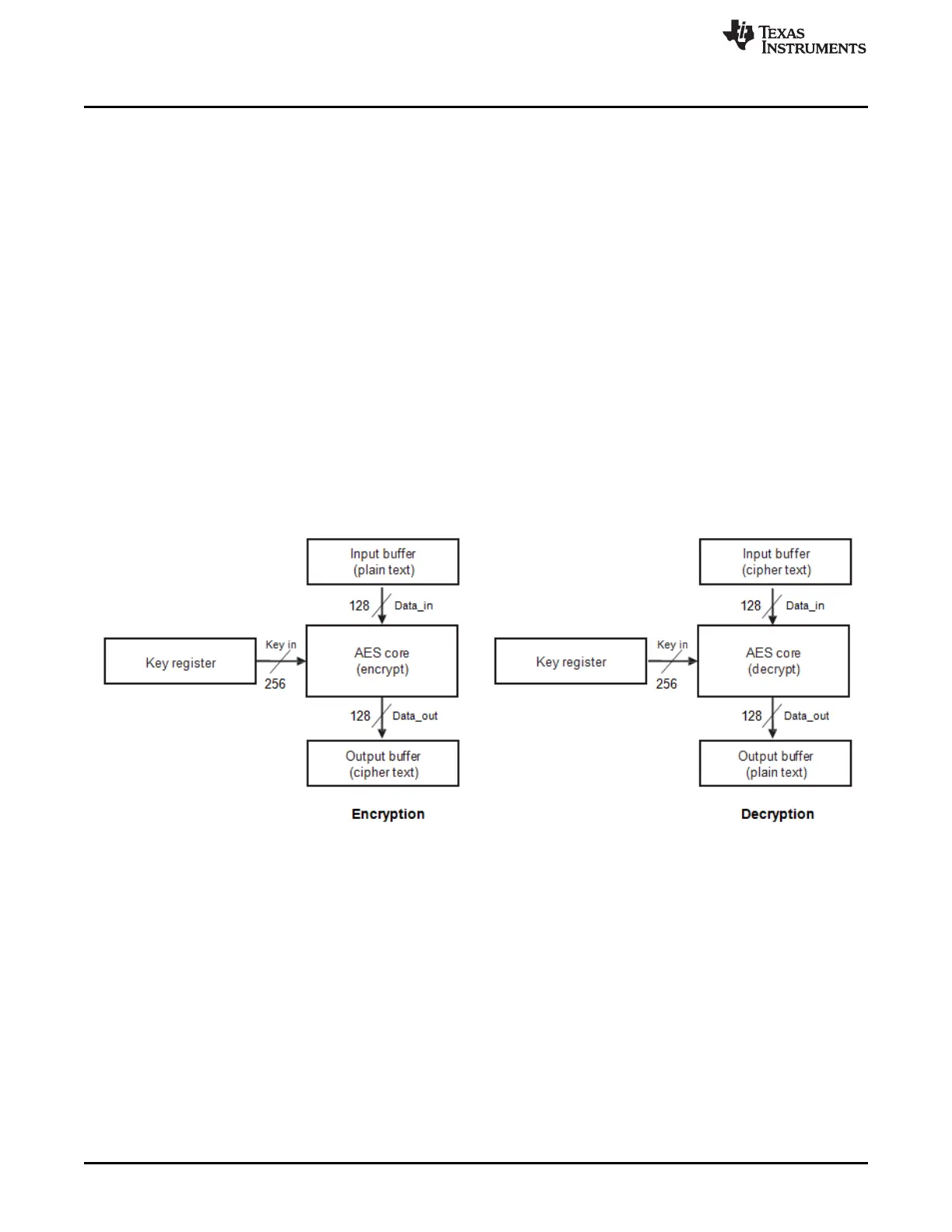
17.2.3 AES Operating Modes
17.2.3.1 Supported Modes of Operation
ECB Feedback Mode
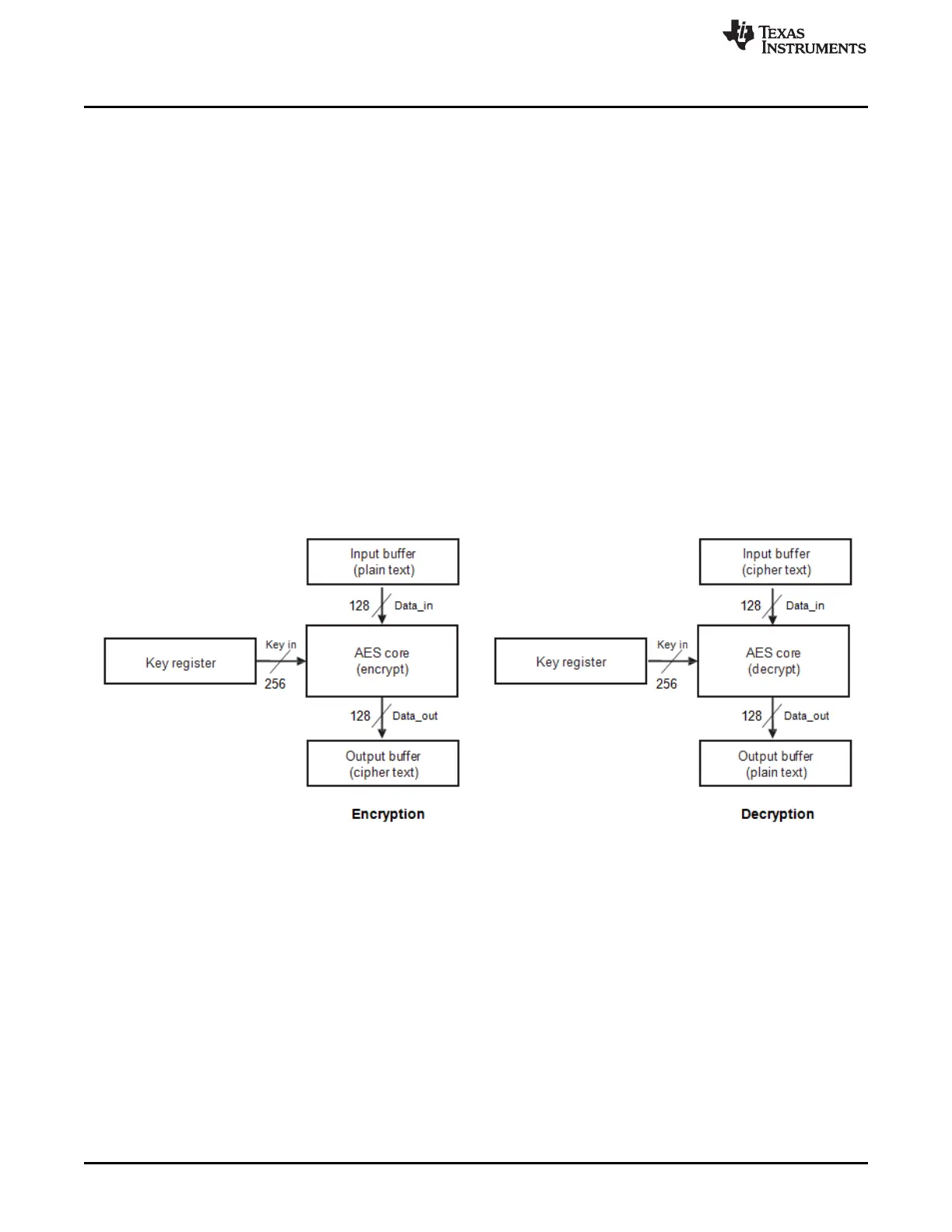
Figure 17-2 shows the basic ECB feedback mode of operation, where the input data is passed directly to
the basic cryptographic core and the output is passed directly to the output buffer.
For decryption, the cryptographic core operates in reverse: the decryption data path is used for data
processing, whereas encryption uses the encryption data path.
Figure 17-2. AES - ECB Feedback Mode
 Loading...
Loading...